Back to Blog 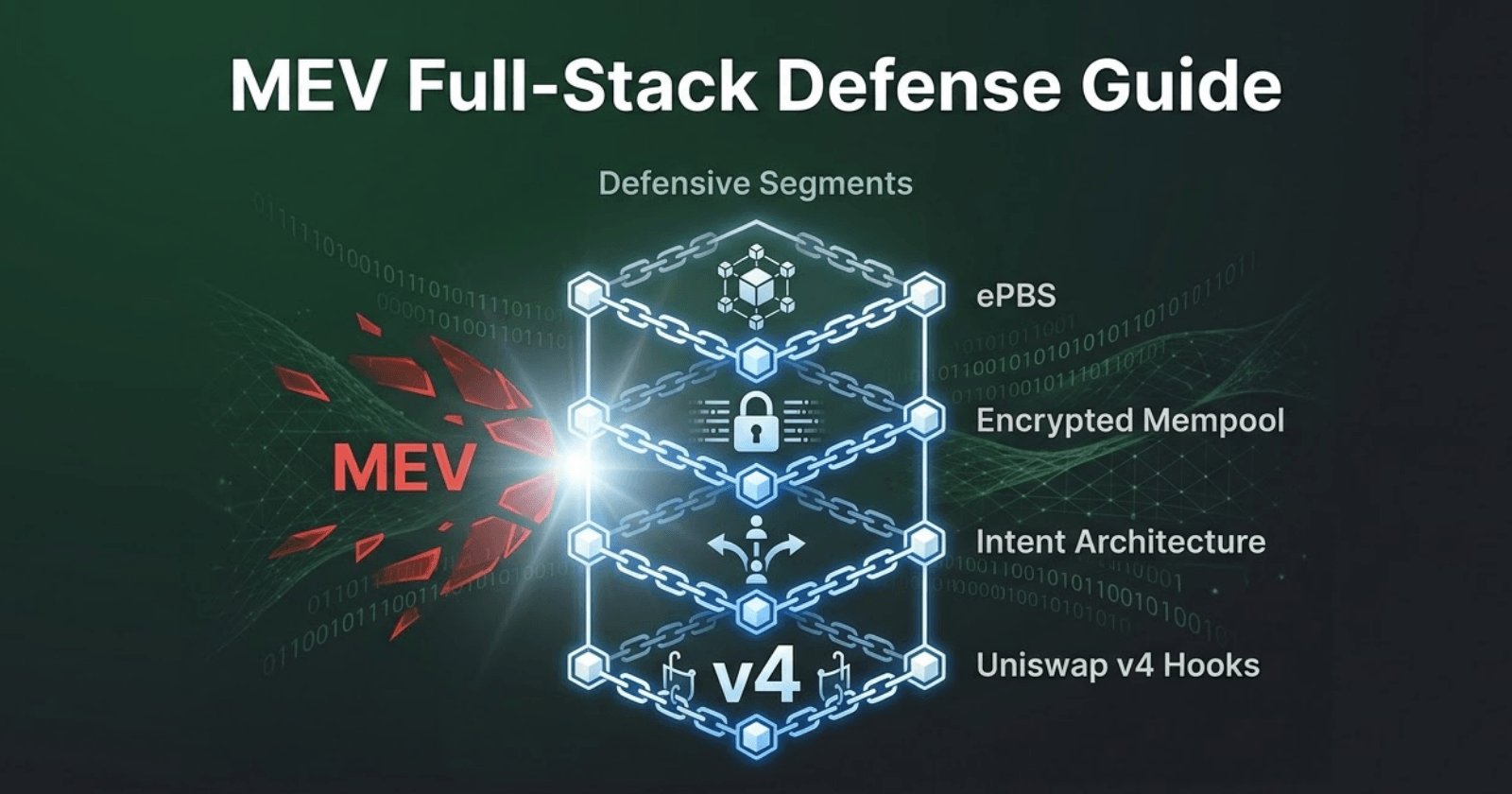
DeFiWeb3 SecurityAudit
How to protect your DeFi protocol from MEV: A full-stack defense guide
12 min
In this article: How MEV searchers extract value from your users via sandwich attacks and front-running, why L2s and alt-chains are not immune, and how to architect multi-layered defenses using PBS, commit-reveal schemes, and private mempools to stop your protocol from bleeding value.
Imagine if the PreCogs from Minority Report weren't using their visions of the future to stop crimes, but were instead using them to aggressively front-run the stock market. They see exactly which asset you are about to buy, purchase it milliseconds before you do, and then forcefully sell it back to you at a premium.
In Web3, adversaries don't need psychic mutants in a pool of water to pull this off. They just need to monitor the public mempool.
Maximal Extractable Value (MEV) is the invisible, cryptographic tax draining your users' wallets. Because public blockchains broadcast execution intents before finality, your users' transactional parameters are exposed to a global arena of heavily capitalized, algorithmic predators. By the time a block is sequenced, the searcher has already calculated the precise price impact of your user's trade, sandwiched the execution, and walked away with a risk-free profit derived entirely from artificially induced slippage.
Since tracking began, malicious MEV vectors have siphoned over 13.4 million via 1.55 million distinct sandwich attacks.
As a DeFi developer or security engineer, ignoring MEV is no longer an option. If your smart contracts do not actively mitigate this predatory extraction, you are serving your users to the wolves. Here is how to architect robust, multi-layered defenses across the protocol, network, and application layers to stop your protocol from bleeding value.
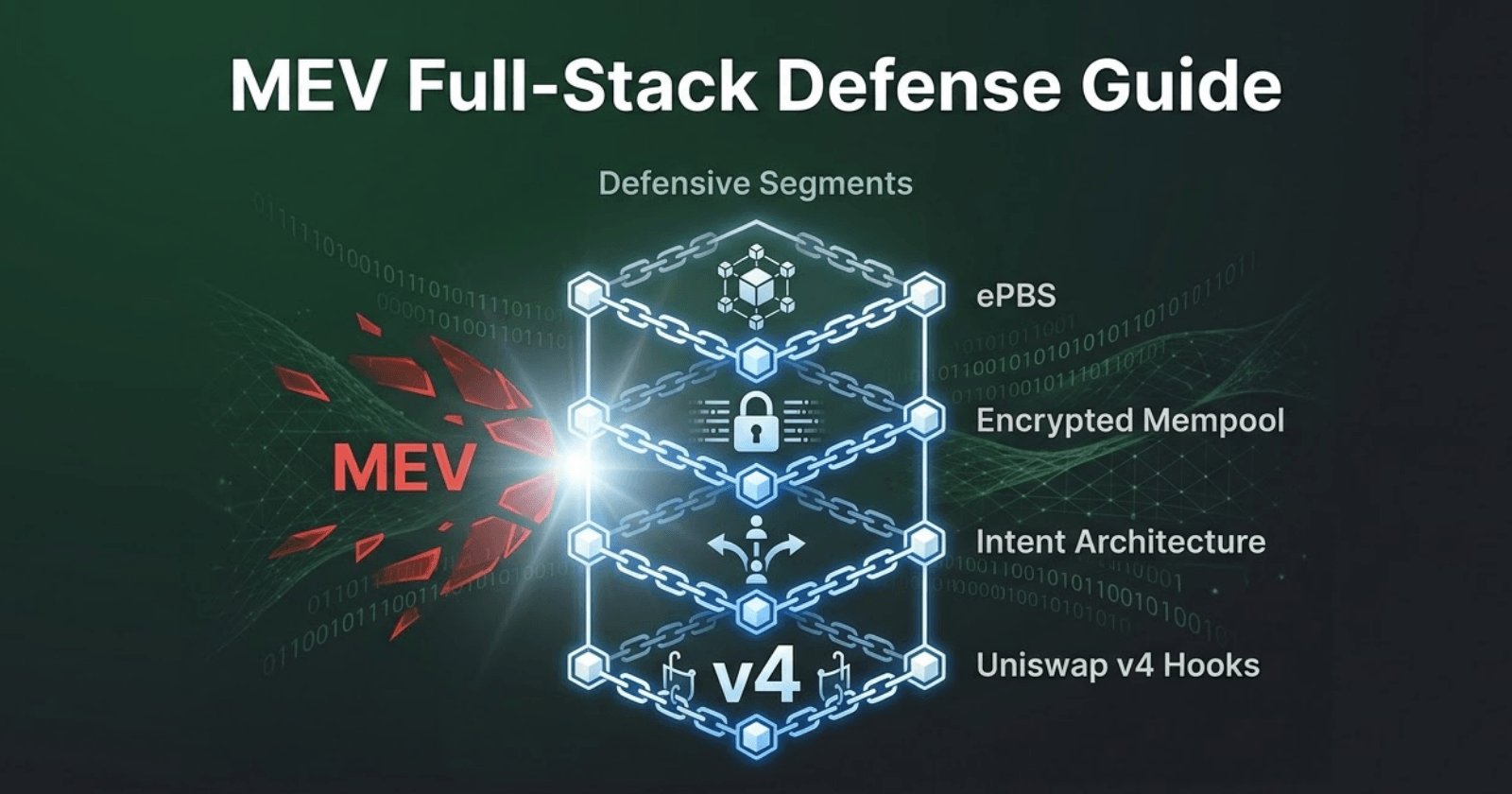
Delegate block building to secure consensus
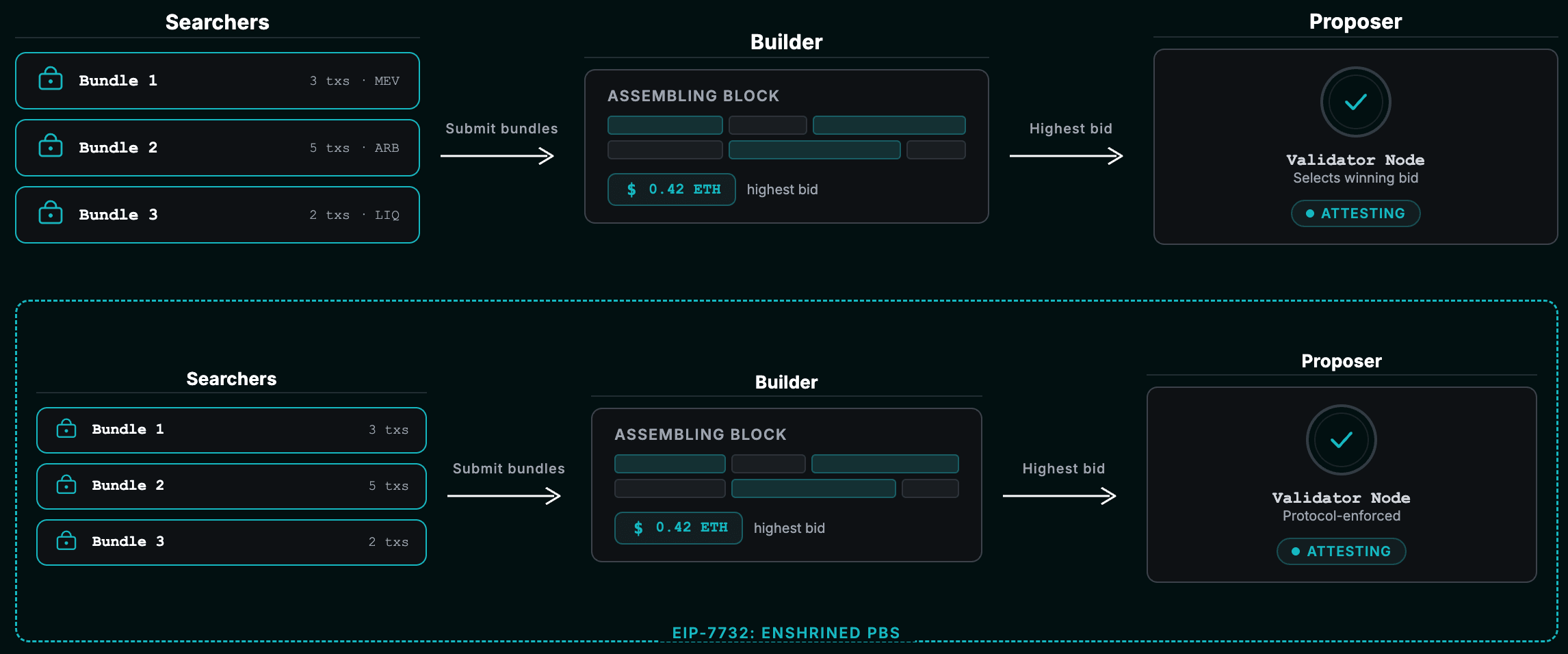
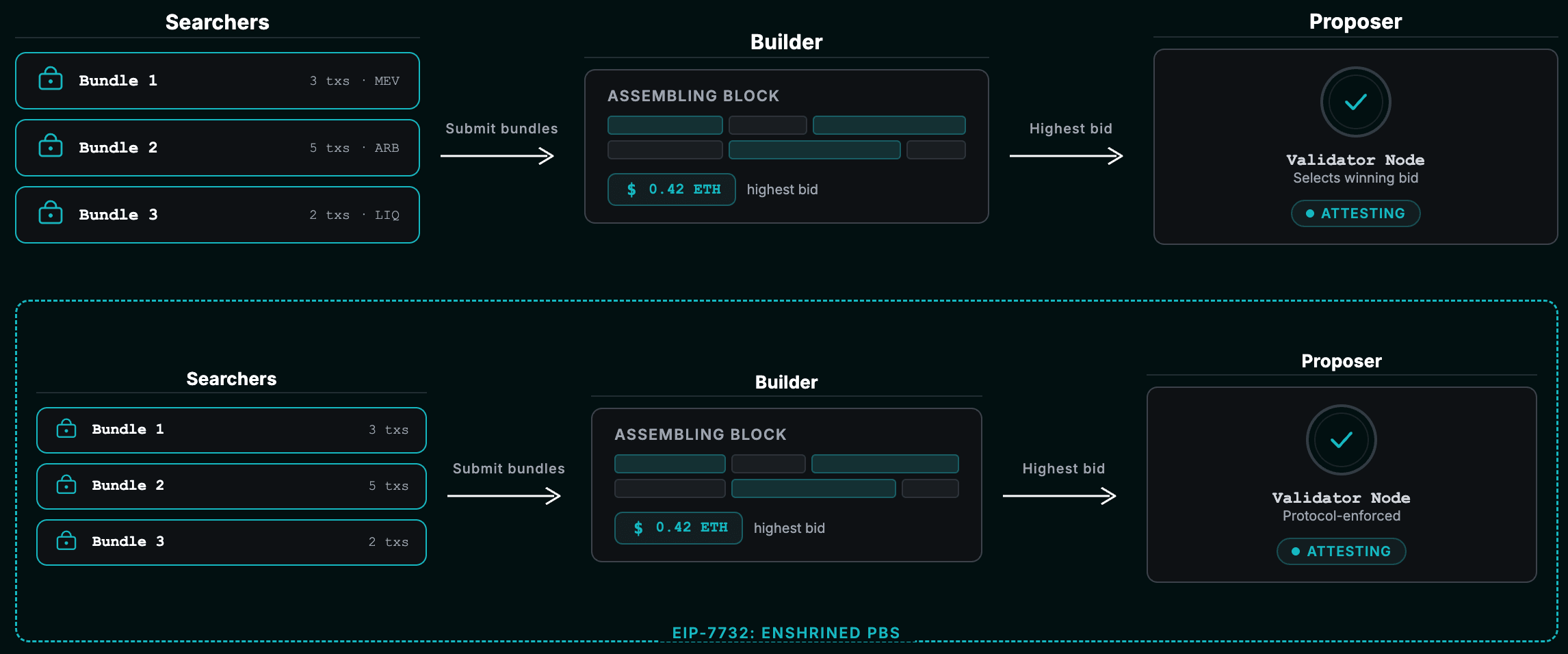
Historically, validator nodes (proposers) handled both consensus validation and the local assembly of transactions. But because optimal MEV extraction requires algorithmic high-frequency trading infrastructure, home validators were rapidly being outcompeted by massive centralized staking pools.
The ecosystem's answer is Proposer-Builder Separation (PBS). By decoupling these roles, validators simply monitor an off-chain marketplace (like MEV-Boost) and blindly accept the highest-bidding execution payload. This fundamentally democratizes validator rewards — median revenue for PBS blocks jumped 104% post-Merge — but it introduces a new nightmare: hyper-centralized block builders operating as oligopolies.
To systematically eliminate the reliance on vulnerable off-chain relays, Ethereum is advancing toward Enshrined PBS (ePBS) via EIP-7732. This integrates the builder-proposer auction directly into the consensus layer, relying on protocol-native cryptographic commitments instead of trusted third parties.
The developer reality: PBS and ePBS are critical for network decentralization, but they do absolutely nothing to protect your end users. ePBS mathematically optimizes the extraction of MEV; it doesn't prevent it. To stop sandwich attacks, you must address the fundamental information asymmetry at the network and application layers.
Blind the searchers with network cryptography
If MEV relies on mempool observability, the logical defense is to encrypt the mempool. By forcing the consensus protocol to blindly commit to a transaction sequence before the contents are revealed, you mathematically neutralize the searcher's algorithmic advantage.
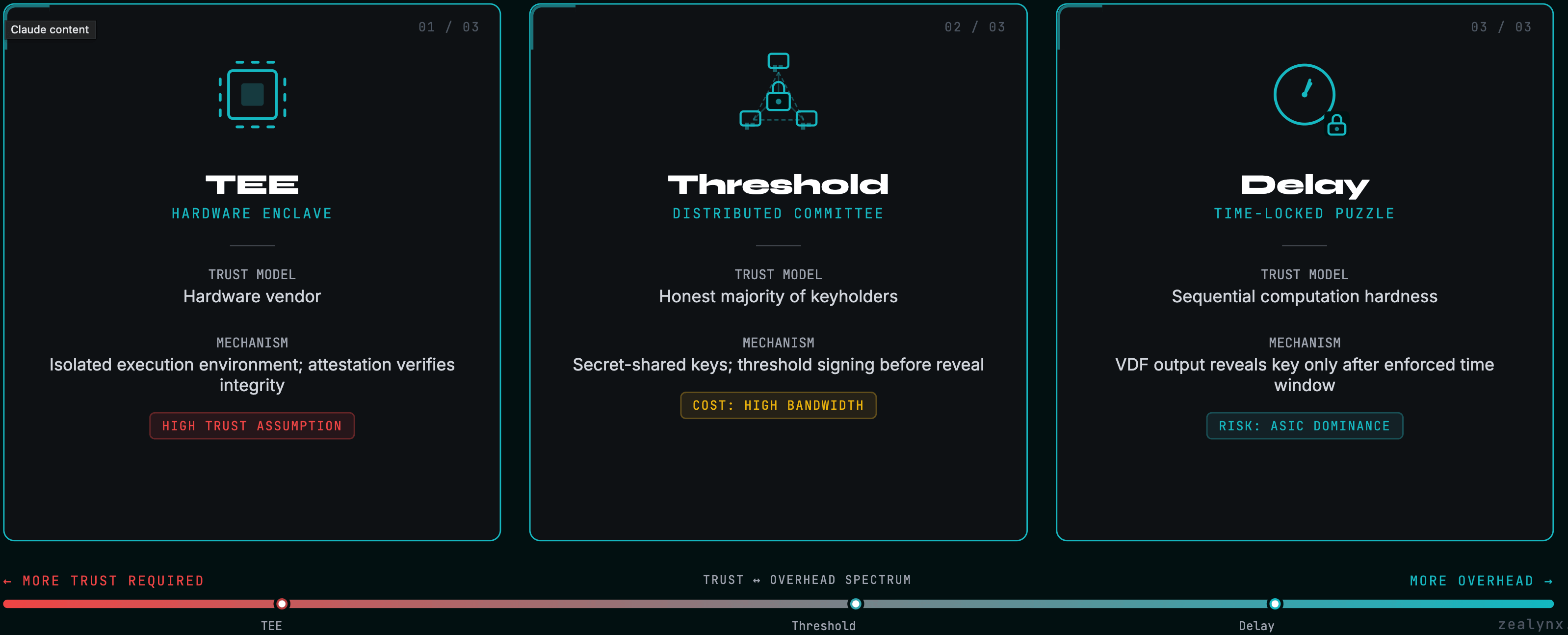
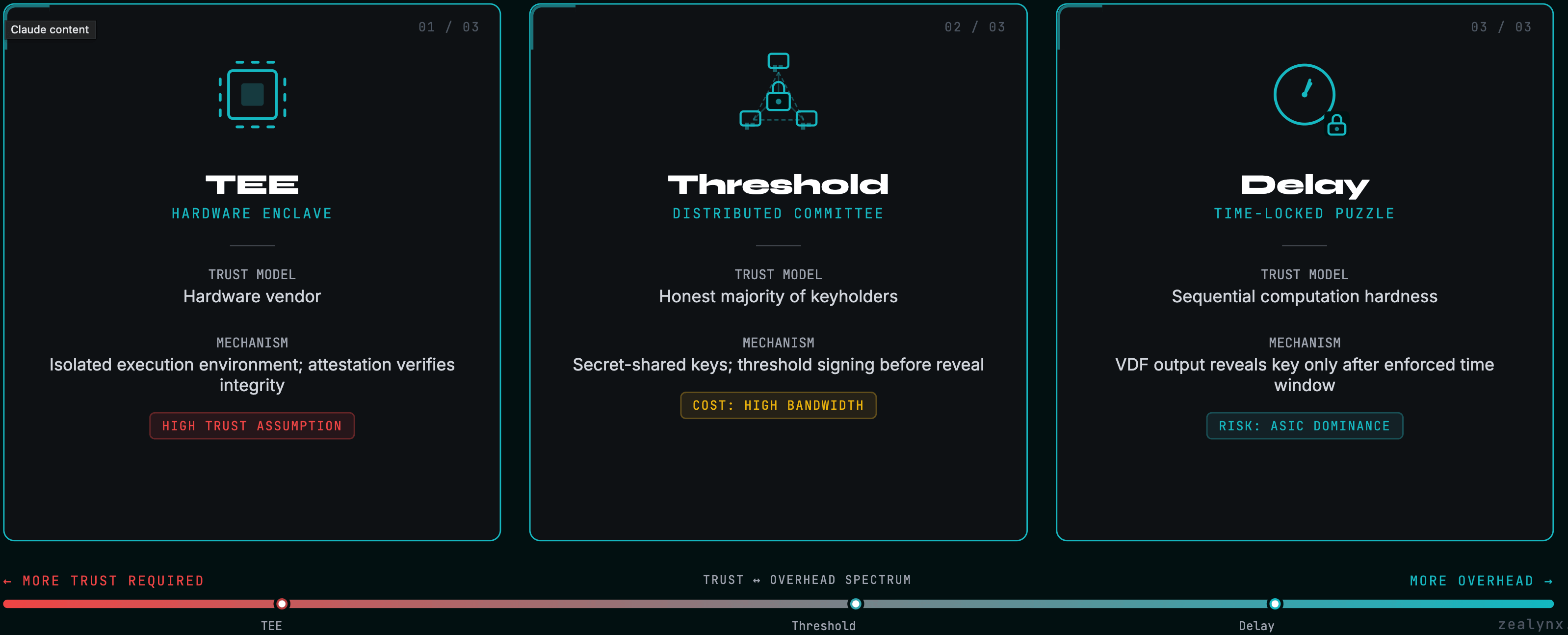
However, engineering a decentralized encrypted mempool is a brutal cryptographic undertaking. Here is how the primitives stack up:
| Cryptographic primitive | How it works | The structural trade-offs |
|---|---|---|
| Trusted Execution Environments (TEEs) | Keys are locked in hardware enclaves (e.g., Intel SGX). Decryption only occurs to build the final block. | Requires absolute trust in hardware manufacturers; historically vulnerable to side-channel attacks. |
| Threshold encryption | Keys are distributed across a decentralized committee. Decryption requires a supermajority (e.g., Shutter Network). | High computational/bandwidth overhead; requires continuous, intensive Distributed Key Generation. |
| Delay encryption | Ciphertexts are locked inside sequential computational puzzles, naturally unlocking after time T. | Exceedingly difficult to calibrate across global networks; incentivizes specialized ASIC dominance. |
The security minefield: Implementing custom threshold encryption workflows is incredibly dangerous. Even if you manage to deploy a commit-reveal architecture flawlessly, you face the lethal threat of metadata leakage. Searchers don't necessarily need to read your payload; highly optimized machine learning models can identify your specific smart contract interactions purely based on the encrypted blob's byte size and broadcast timestamp. They can — and will — execute statistical CEX-DEX arbitrage against your protocol without ever decrypting the payload. Relying on battle-tested, deeply audited infrastructure like the Shutter Network is the only viable path to deploying threshold cryptography safely.
Shift execution risk via intent architectures
If you can't out-engineer the searchers at the network layer, change the rules of engagement at the application layer. Standard DeFi relies on imperative execution: "Swap exactly 1000 USDC for ETH on Uniswap, maximum 1% slippage." This static target is exactly what MEV bots prey upon.
Modern protocols are pivoting to intent-centric architectures, pioneered by platforms like the CoW Protocol. Instead of specifying an exact route, users sign an off-chain EIP-712 message outlining their strict constraints (e.g., minimum output acceptable).
This intent is routed to a frequent batch auction where algorithmic "solvers" fiercely compete to find the most optimal settlement path. This neutralizes MEV through:
- Coincidence of Wants (CoW): Solvers match opposing orders directly peer-to-peer off-chain, bypassing AMM liquidity pools entirely. No pool interaction means zero opportunity for sandwich attacks.
- Uniform directional clearing prices: All trades for the same token pair in the same direction clear at the exact same price within a batch. If sequence dictates nothing about the final price, the fundamental premise of front-running is destroyed.
By adopting intents, you shift the execution risk from the retail user to heavily bonded, highly sophisticated solvers.
For a deeper exploration of how AMM mechanics create the price impact that MEV bots exploit, read our AMM security foundations series.
Weaponize AMM hooks with extreme caution
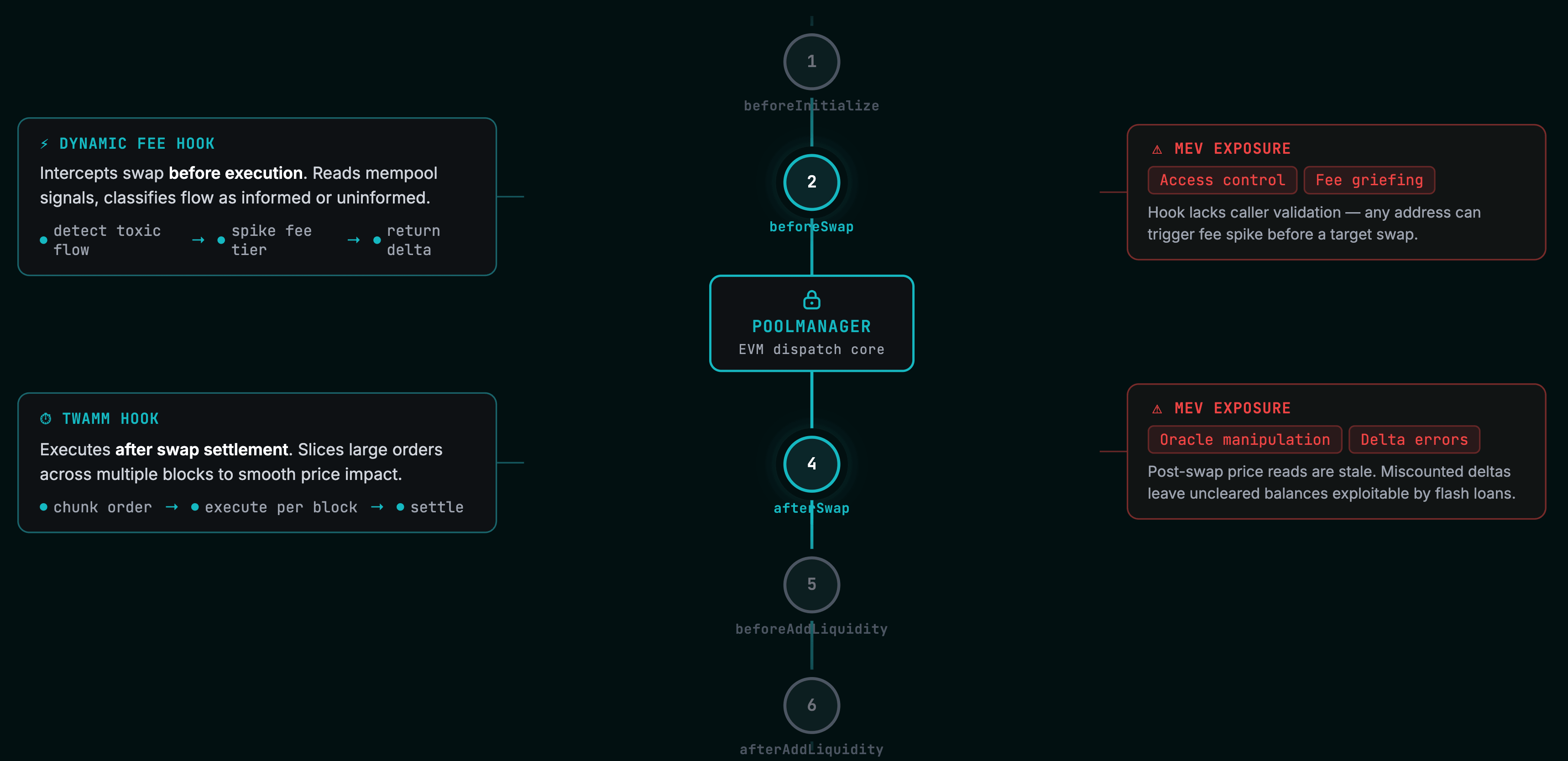
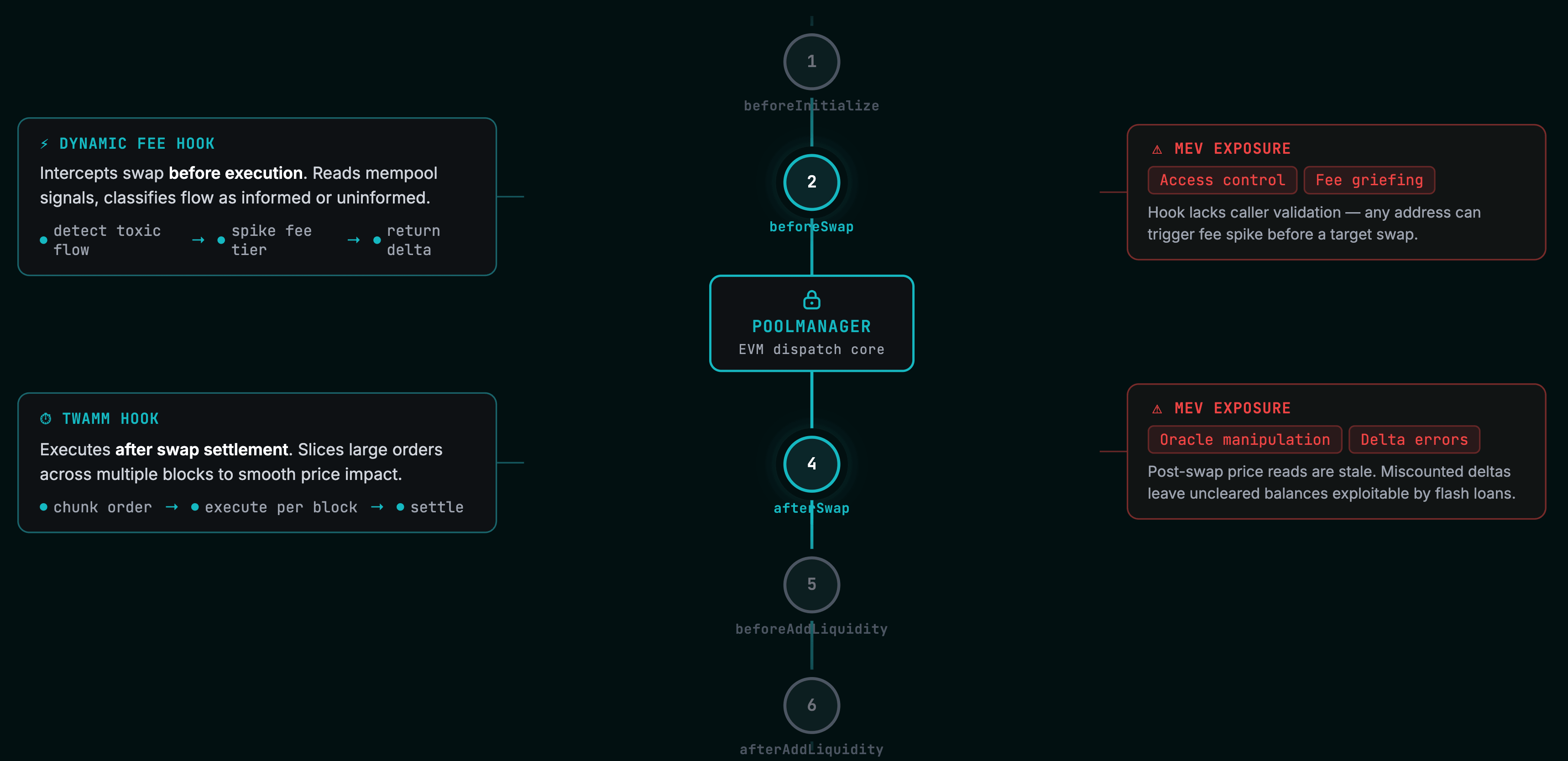
For protocols requiring deep, on-chain liquidity, entirely bypassing automated market makers isn't feasible. To structurally protect liquidity providers (LPs), developers are leveraging Uniswap v4 Hooks — custom smart contracts that execute arbitrary logic at precise lifecycle points (e.g.,
beforeSwap, afterAddLiquidity).Hooks allow you to internalize MEV natively:
- Algorithmic dynamic fees: A
beforeSwaphook can monitor for toxic order flow and instantly spike the swap fee when it detects aggressive directional sizing, destroying the MEV bot's profit margin and redistributing the penalty to LPs. - Time-Weighted Average Market Makers (TWAMM): Hooks can slice massive institutional orders into infinitesimal pieces over prolonged blocks, obfuscating the total trade size from mempool observers.
The security minefield: Uniswap v4's architecture relies on a shared security model. Uniswap secures the core PoolManager kernel, but you are entirely responsible for the arbitrary user-space logic inside your hook.
A single flaw in your access control can lead to absolute protocol ruin.
- Access control failures: If your hook fails to cryptographically verify that the callback strictly originated from the
PoolManager, an attacker can bypass the kernel entirely, manipulate state, and drain collateral. - MEV manipulation of dynamic logic: Bots will actively manipulate the integrated on-chain oracle or block timestamp to artificially trigger favorable fee tiers strictly prior to their own execution.
- Delta accounting errors: V4's flash accounting requires netting out positive and negative token deltas perfectly. Unsettled dust or improper delta tracking leads to continuous value leakage.
If you're building hooks, our Uniswap v4 hooks deep dive and first hook tutorial cover the security patterns in detail.
Get the DeFi Protocol Security Checklist
15 vulnerabilities every DeFi team should check before mainnet. Used by 30+ protocols.
No spam. Unsubscribe anytime.
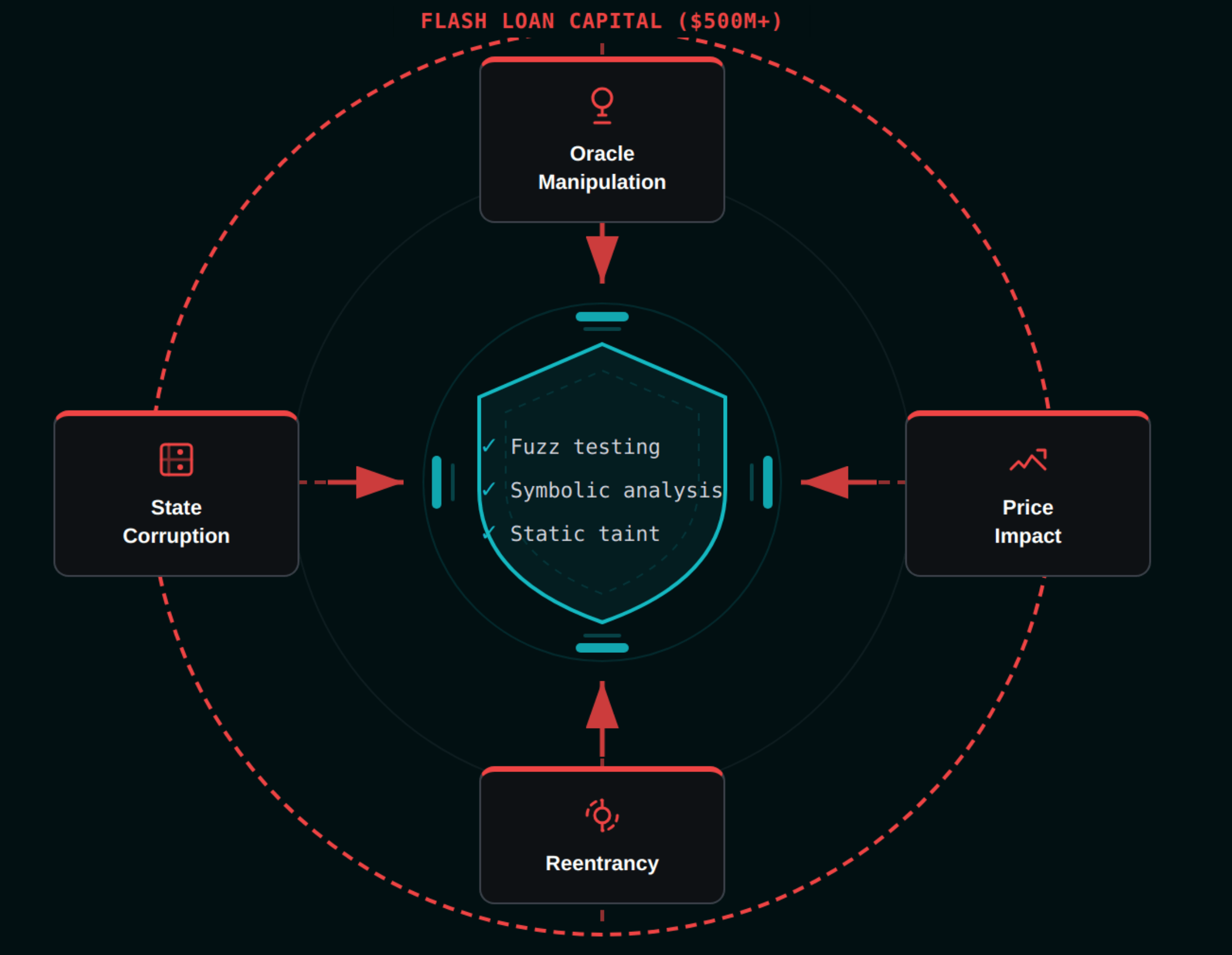
Audit for the omnipresent flash loan threat
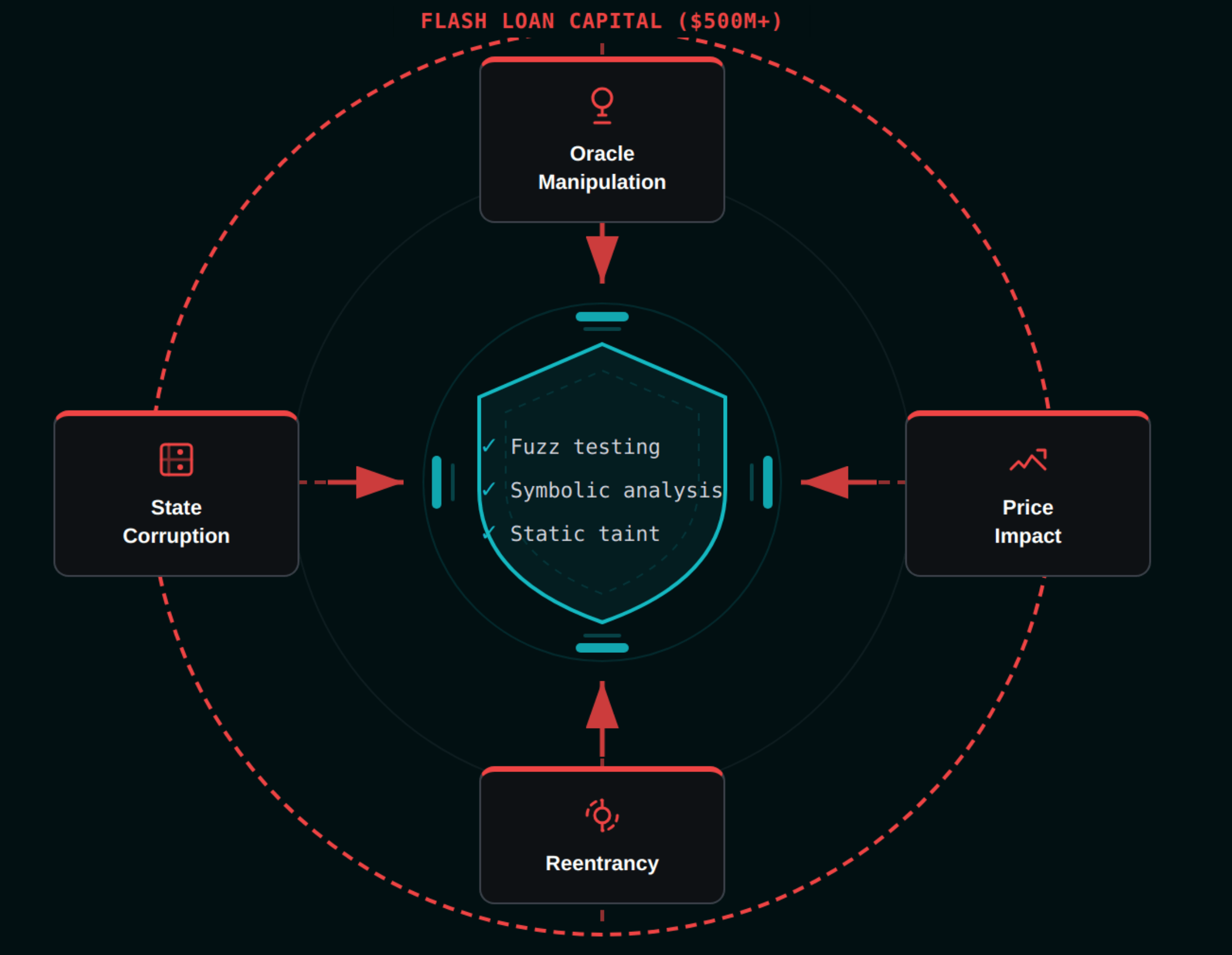
The days of relying on surface-level, checklist-based smart contract audits are over. When an adversary can utilize uncollateralized Flash Loans to borrow hundreds of millions of dollars for a single transaction, the attack surface scales exponentially.
Mitigating MEV from scratch — whether through custom encrypted mempools, highly complex v4 hooks, or off-chain solver networks — introduces immense structural complexity. Delegating execution authority to smart contracts requires rigorous invariant fuzz testing, hybrid symbolic analysis, and deep static taint analysis to mathematically guarantee that your pricing oracles cannot be corrupted by flash-loan-induced manipulation.
See how the defense-in-depth methodology combines static analysis, fuzzing, and formal verification into a layered security pipeline that catches MEV-adjacent vulnerabilities before deployment.
The takeaway is clear: Defeating MEV is a full-stack, combinatorial war. It requires leveraging ePBS for base-layer consensus, utilizing proven encrypted mempools for private transaction broadcasting, and building intent-centric applications fortified by uncompromising security standards. Do not attempt to roll your own cryptographic primitives or complex AMM hooks in isolation. Partner with specialized security researchers, lean on deeply audited infrastructure, and architect your protocol under the assumption that an omniscient adversary is always watching.
Because in the dark forest of Web3, they absolutely are.
Get in touch
If your protocol handles user trades, manages LP positions, or interacts with on-chain liquidity in any form, MEV is already affecting your users. Whether you need a security audit for custom Uniswap v4 hooks, a threat model for your intent-based architecture, or a comprehensive review of your oracle dependencies and flash loan resilience — we can help.
You can also reach us directly at [email protected] or book a free consultation call to discuss your protocol's MEV exposure.
FAQ: MEV protection for DeFi protocols
1. What is MEV and why should DeFi developers care about it?
Maximal Extractable Value (MEV) is profit that block producers, builders, or searchers extract by strategically reordering, inserting, or censoring transactions within a block. For DeFi developers, MEV directly degrades user experience: trades execute at worse prices due to sandwich attacks, transactions fail from front-running, and liquidity providers lose value to toxic order flow. Ignoring MEV means your protocol silently taxes every user interaction — and sophisticated competitors who do address it will offer measurably better execution.
2. How does Proposer-Builder Separation (PBS) work, and does it actually protect users from sandwich attacks?
PBS splits the block production process into two roles: proposers (validators who attest to blocks) and builders (specialized actors who assemble the most profitable transaction ordering). Proposers select the highest-bidding block from builders via an auction. While PBS democratizes validator revenue and reduces centralization pressure, it does not protect end users. Builders still optimize for MEV extraction — PBS simply makes the extraction market more competitive. User-facing protection requires additional layers like encrypted mempools or intent-based execution.
3. What is an encrypted mempool and how does it prevent front-running?
An encrypted mempool requires users to submit transactions in encrypted form. The consensus protocol commits to a transaction ordering before the contents are revealed and decrypted. Since MEV searchers cannot read transaction parameters (token, amount, direction) until after sequencing is finalized, they cannot construct profitable front-running or sandwich attacks. Implementations include threshold encryption (Shutter Network), Trusted Execution Environments (Intel SGX enclaves), and delay encryption (time-locked puzzles). Each carries trade-offs in trust assumptions, latency, and computational overhead.
4. What are intent-based architectures and how do they differ from standard DEX swaps?
In a standard DEX swap, users specify an imperative instruction: "swap X tokens for Y on this specific pool with this slippage." This deterministic execution path is trivially sandwichable. Intent-based architectures (like CoW Protocol) flip the model: users sign a declarative message stating constraints ("I want at least Z output tokens") without specifying execution details. Professional solvers then compete in batch auctions to find the optimal settlement — including peer-to-peer matching that bypasses AMM pools entirely, eliminating sandwich attack vectors at the architectural level.
5. Can Uniswap v4 hooks introduce new security vulnerabilities while trying to mitigate MEV?
Yes — hooks are user-deployed smart contracts that execute arbitrary logic at critical pool lifecycle points (before/after swaps, liquidity changes). If a hook fails to validate that calls originate from the legitimate PoolManager contract, attackers can invoke hook logic directly and manipulate pool state. Dynamic fee hooks are particularly vulnerable: MEV bots can manipulate the on-chain data the hook reads (oracles, timestamps) to trigger favorable fee tiers before their own trades. Delta accounting errors in v4's flash accounting system can also create subtle value leakage that compounds over time. Every custom hook requires a dedicated security audit.
6. Why do flash loans make MEV-related vulnerabilities exponentially more dangerous?
Flash loans provide attackers with unlimited capital within a single atomic transaction — at zero collateral cost. This means any vulnerability that is "theoretically exploitable but requires large capital" becomes immediately practical. An attacker can borrow $500M, manipulate an AMM's spot price to corrupt a protocol's oracle, exploit the mispriced state (triggering bad liquidations, draining lending pools), reverse the price manipulation, and repay the loan — all within one transaction. If the attack fails, the transaction simply reverts with no cost to the attacker. This is why every DeFi audit must model threats assuming adversaries have effectively infinite capital for a single block.
Glossary
| Term | Definition |
|---|---|
| MEV (Maximal Extractable Value) | Profit extracted by reordering, including, or excluding transactions within a block. |
| Sandwich Attack | An MEV attack where an attacker front-runs and back-runs a victim's trade to extract profit. |
| Front-running | Observing pending transactions and submitting similar transactions with higher gas to execute first. |
| Flash Loan | Uncollateralized loan borrowed and repaid within a single atomic transaction. |
| Slippage | The difference between expected and actual execution price of a trade. |
| Flash Accounting | Uniswap v4's system for netting token debits and credits within a single transaction. |
| Hooks | Custom smart contracts that execute logic at specific pool lifecycle points in Uniswap v4. |
| Automated Market Maker | A protocol that uses mathematical formulas instead of order books to price assets. |
MEV Exposure in Your Protocol? Get It Audited.
Sandwich attacks, frontrunning, and flash loan exploitation become practical the moment a protocol goes live with liquidity. Our audits model adversarial behavior assuming infinite capital — catching AMM oracle exposure, slippage manipulation, and hook-level MEV vectors before they cost users.
Get the DeFi Protocol Security Checklist
15 vulnerabilities every DeFi team should check before mainnet. Used by 30+ protocols.
No spam. Unsubscribe anytime.