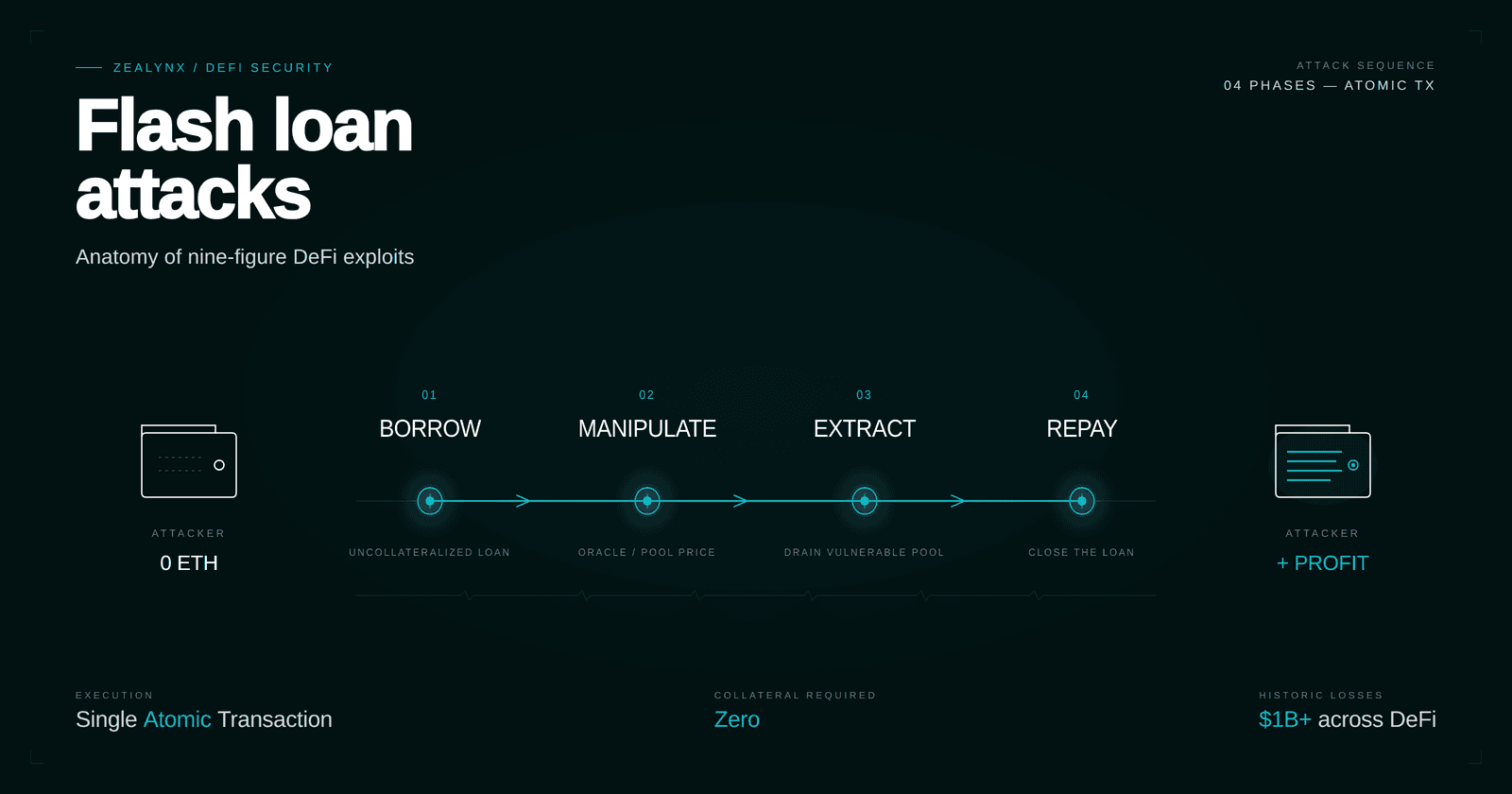
Flash loan attacks: anatomy of nine-figure DeFi exploits
How flash loans amplify oracle, donation, and reentrancy bugs into $200M+ DeFi exploits — Cetus, Penpie, KyberSwap, UwU Lend case studies plus defenses that hold.
ReadCataloged smart contract attack patterns: reentrancy, oracle manipulation, flash loans, MEV, front-running, and the rest of the bestiary.
How flash loans amplify oracle, donation, and reentrancy bugs into $200M+ DeFi exploits — Cetus, Penpie, KyberSwap, UwU Lend case studies plus defenses that hold.
Read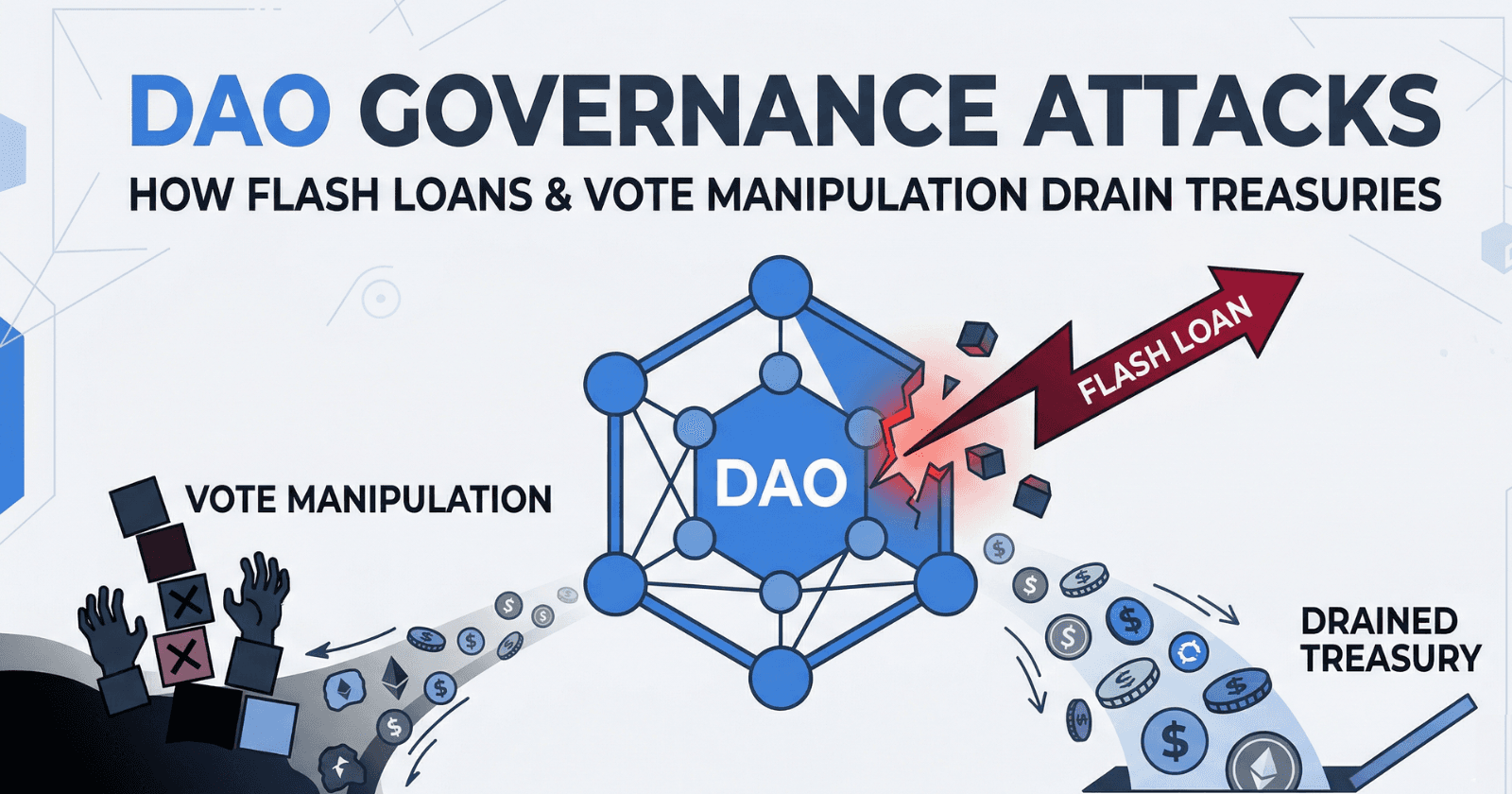
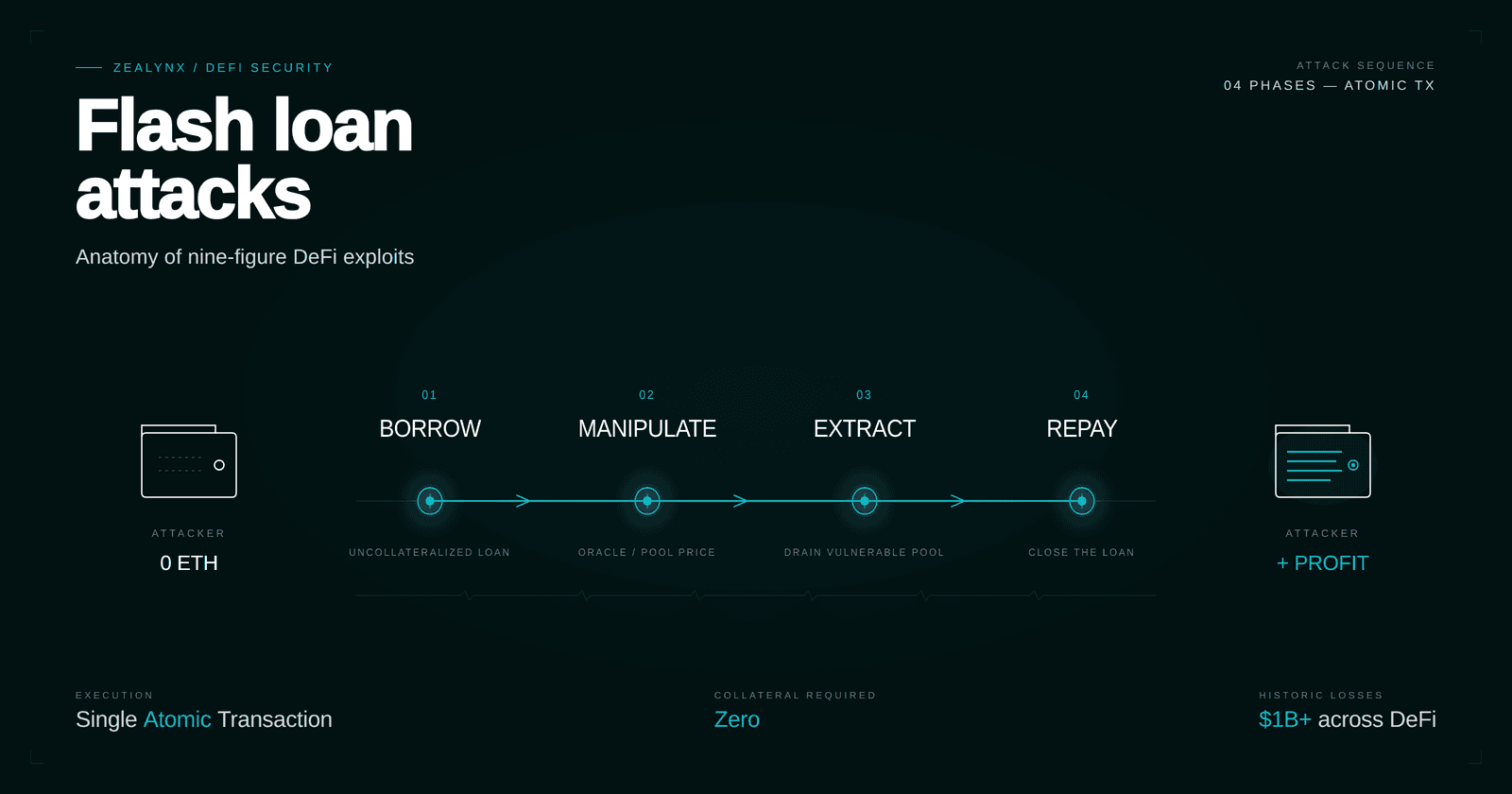
How attackers exploit DAO governance with flash loans, EVM opcode injection, and quorum exhaustion — plus audit strategies and defense architectures.
Read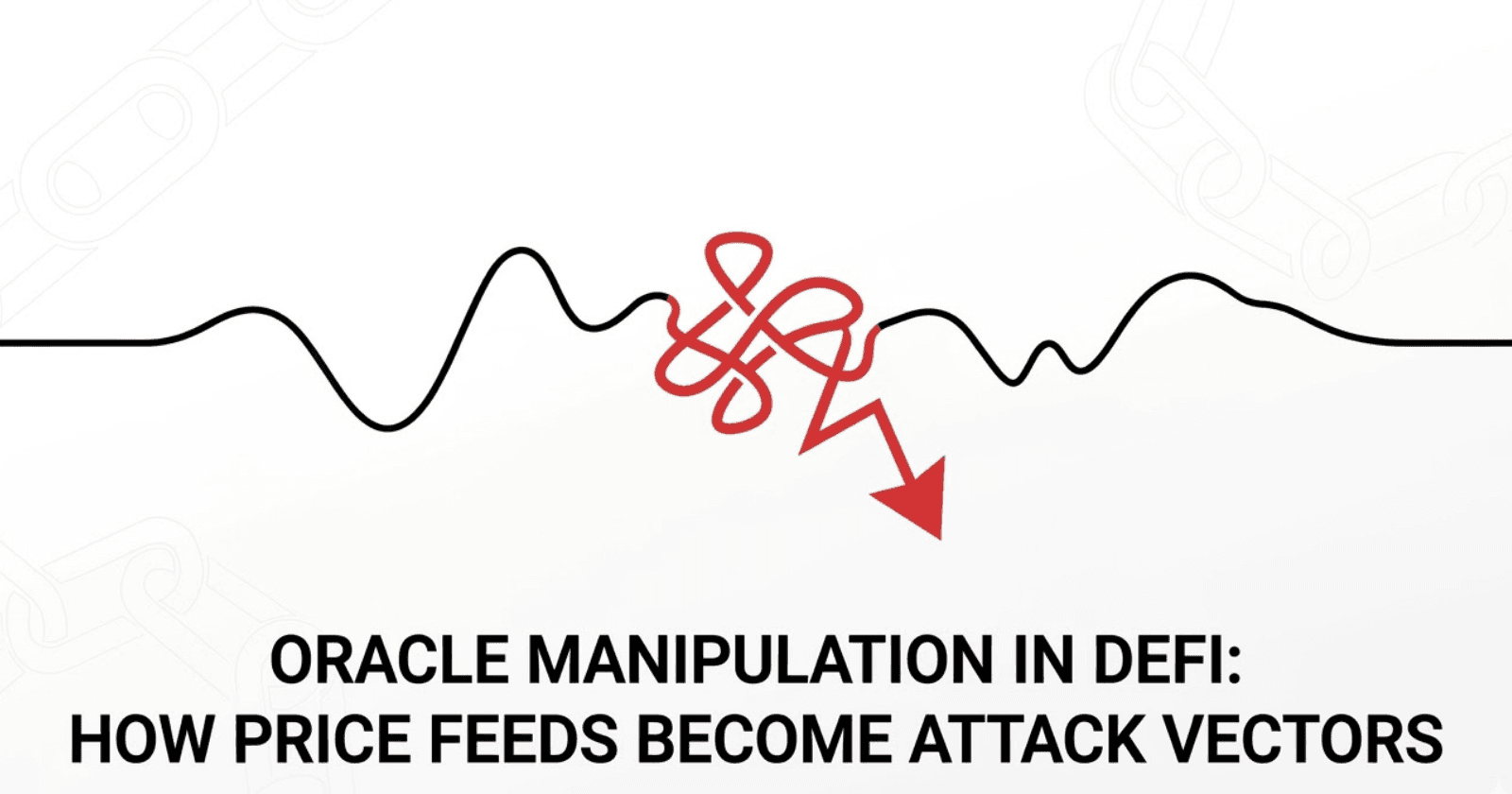
How attackers exploit oracle price feeds in DeFi using flash loans, AMM imbalances, and governance subversion — with defense patterns for protocol architects.
Read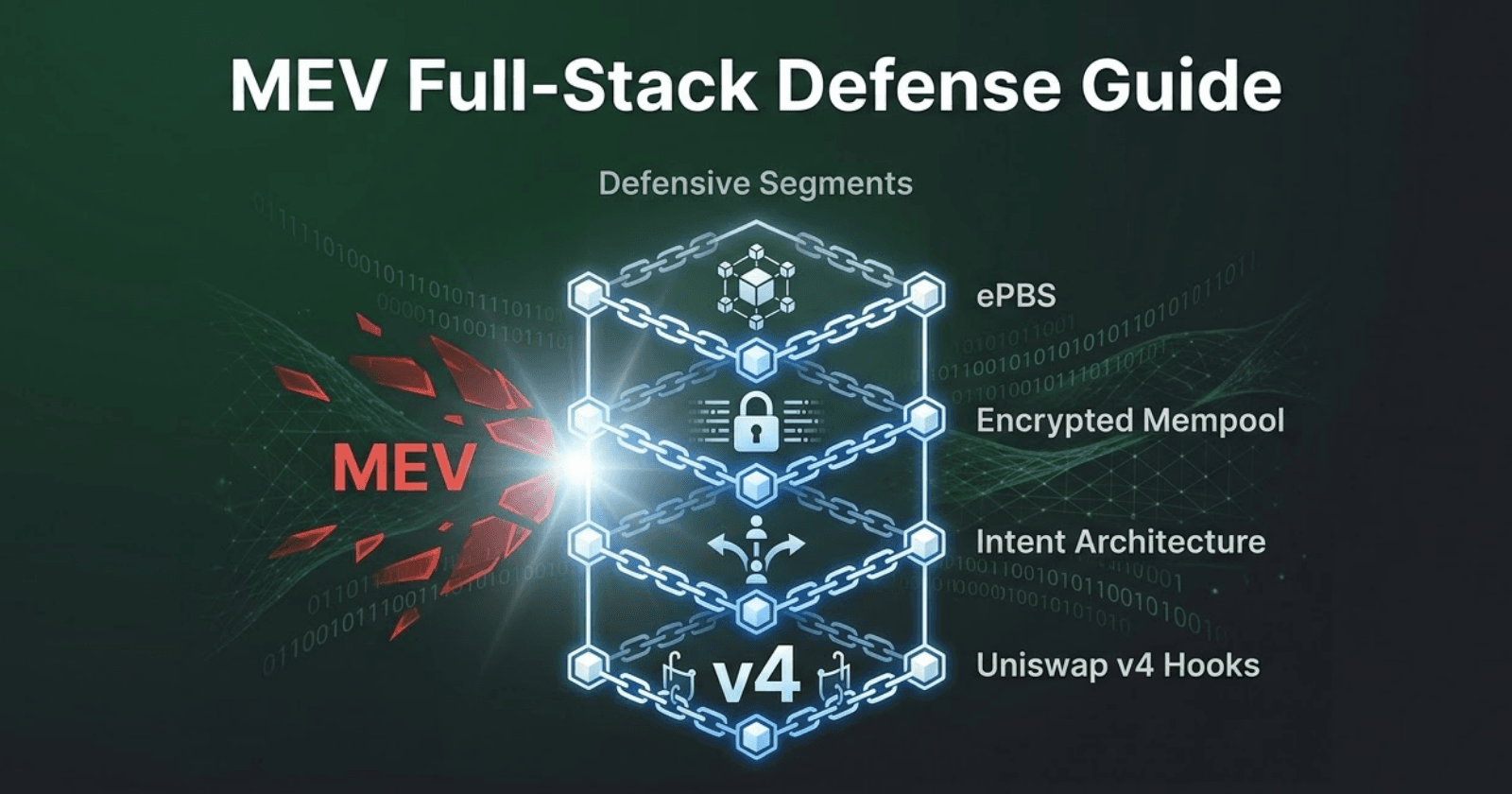
Learn how to defend your DeFi protocol from sandwich attacks and MEV extraction with PBS, encrypted mempools, intent architectures, and Uniswap v4 hooks.
Read
Learn how to prevent front-running in ERC20 smart contracts using safer allowance methods and secure coding practices. Protect your tokens from exploits.
Read
Learn about overflow and underflow vulnerabilities in Solidity with real high and medium severity audit findings, code examples, and an exercise to practice.
Read
Explore real-life examples of Denial of Service (DoS) attacks on smart contracts found in audit contests. Learn about DoS caused by underflow, gas limits, nonReentrant modifiers, external calls, and malicious receivers.
Read
Learn why using tx.origin for authorization in Solidity is vulnerable to phishing attacks, how attackers exploit it, and how msg.sender prevents it.
Read
Learn what reentrancy attacks are in Solidity smart contracts, how attackers exploit them, and three prevention techniques including noReentrant modifiers, Checks-Effects-Interactions pattern, and GlobalReentrancyGuard.
Read