Donation Attack
An exploit on empty or near-empty vaults where a direct token transfer inflates share price, letting an attacker round subsequent depositors down to zero shares.
A donation attack (also called a first-depositor attack or share inflation attack) is an exploit against vaults, lending markets, and other share-issuing contracts whose share price is computed as totalAssets / totalSupply. When totalSupply is zero or very small, an attacker can transfer underlying assets directly to the contract — bypassing the deposit() function so no shares are minted — driving the share price to absurd values. Subsequent depositors then round down to zero shares, and the attacker withdraws both their position and the victim's deposit.
The attack is the canonical empty-market vulnerability in Compound V2 forks and ERC-4626 vaults without virtual offset protection. Hundred Finance ($7.5M, 2023), Onyx ($2.1M, 2023), Starlay ($2.1M, 2023), and Sonne Finance ($20M, 2024) all lost funds to this single class of bug. Flash loans make the capital requirement irrelevant: an attacker can borrow the donation amount, execute the inflation, drain the victim's deposit, and repay all in one atomic transaction.
Mechanics
The exchange rate of a typical Compound V2 cToken is computed as (totalCash + totalBorrows - totalReserves) / totalSupply. ERC-4626 vaults compute it as totalAssets / totalSupply. In both cases:
- Attacker calls
mint()ordeposit()for a tiny amount (e.g., 1–2 wei), creating a non-zerototalSupplyof essentially nothing. - Attacker transfers a large amount of the underlying asset directly to the contract address using ERC-20
transfer— this raisestotalAssets(ortotalCash) without minting new shares. - The share price is now
largeAmount / 2 wei, an astronomically high number. - Victim deposits
Xunderlying. Their share count isX * totalSupply / totalAssets, which rounds down to 0 ifX < totalAssets / totalSupply. - Attacker redeems their original 2 wei of shares, withdrawing all underlying — including the victim's deposit.
Defenses
Mint-and-burn dead shares on initialization — the simplest fix for Compound V2 forks. When deploying a new market, in the same transaction mint a non-trivial amount of cToken (e.g., 1e8 wei) and send it to address(0). This makes totalSupply unbreachably non-zero and the donation uneconomical.
Virtual offset (ERC-4626) — OpenZeppelin's ERC4626._decimalsOffset() adds virtual shares and assets to the conversion math, so the attacker would need to lose 10^offset × victim_deposit to extract the victim's deposit. A _decimalsOffset of 6 makes the attack economically irrational.
Bundled deployment — never split market initialization across multiple transactions. Sonne Finance's "deploy → seed → set collateral factor" was three separate multisig transactions; the attacker only needed to call steps 1 and 3. Bundle everything into a single Multicall payload or restrict the executor role on the timelock.
Permissioned market creation — restrict _supportMarket() and similar functions to roles that won't get front-run. This eliminates the race entirely on permissioned forks.
See reentrancy attack and price oracle manipulation for the other two attack classes that flash loans amplify into nine-figure exploits.
Articles Using This Term
Learn more about Donation Attack in these articles:
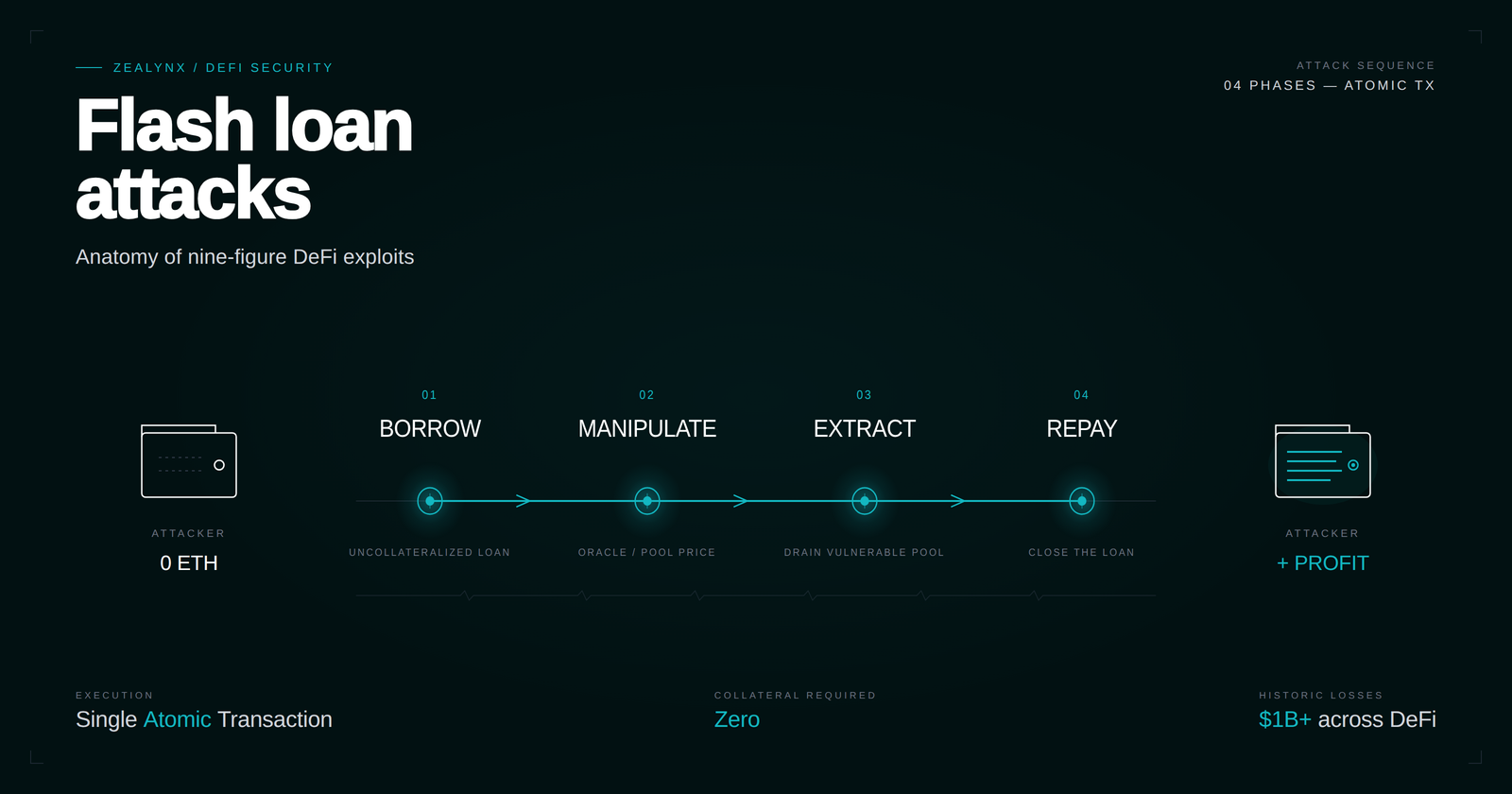
Flash loan attacks: anatomy of nine-figure DeFi exploits
How flash loans amplify oracle, donation, and reentrancy bugs into $200M+ DeFi exploits — Cetus, Penpie, KyberSwap, UwU Lend case studies plus defenses that hold.
Yearn vault security: V2 vs V3 architecture, exploits, and defense patterns
Yearn V2 and V3 vault architecture, exploit case studies (yDAI, yUSDT, Cream), and defense patterns every DeFi auditor and integrator must know.

Top DEX Security Analysis: AMM Vulnerabilities Exposed
AMM security deep dive Part 2: how Uniswap V2–V4, Curve, and Balancer handle capital efficiency — and the slippage, sandwich, and oracle manipulation risks each introduces.
Related Terms
Need expert guidance on Donation Attack?
Our team at Zealynx has deep expertise in blockchain security and DeFi protocols. Whether you need an audit or consultation, we're here to help.
Get a Quote
