Supply Chain Attacks in Web3 — From NPM to Protocol Exploits
Complete guide to Web3 supply chain attacks with 5 vectors, real incidents, and actionable checklist.
ReadAI security, MCP server reviews, and red-team write-ups across smart contracts, dApps, and Web2 infrastructure.
Complete guide to Web3 supply chain attacks with 5 vectors, real incidents, and actionable checklist.
Read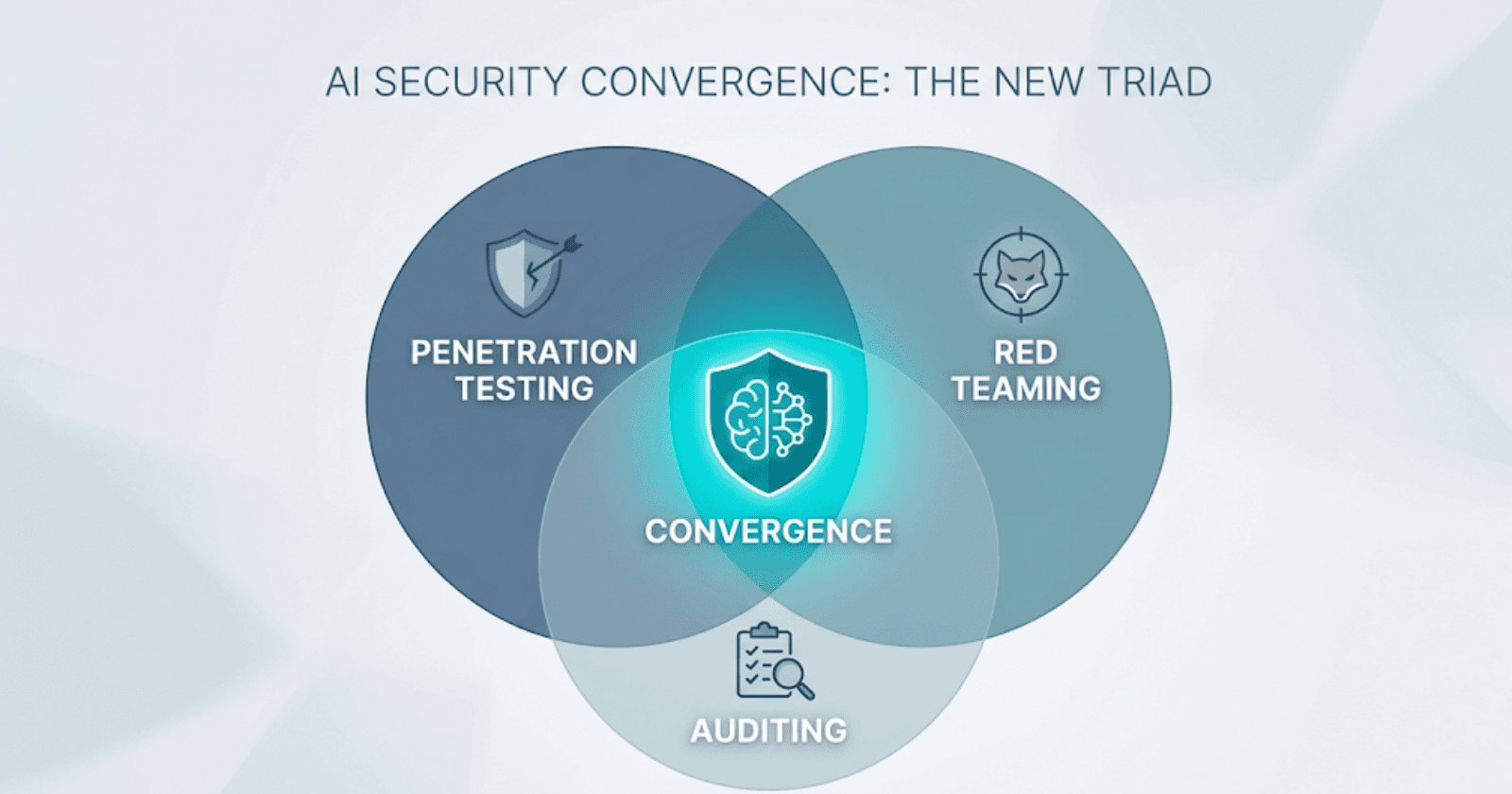
Pentesting finds bugs, red teaming tests defenses, audits prove compliance. Learn why AI security demands all three integrated into one TEVV lifecycle.
Read
Five systemic vectors targeting AI trading bots — adversarial ML, data poisoning, prompt injection, API exploits, supply chain compromise — with strategic mitigation.
Read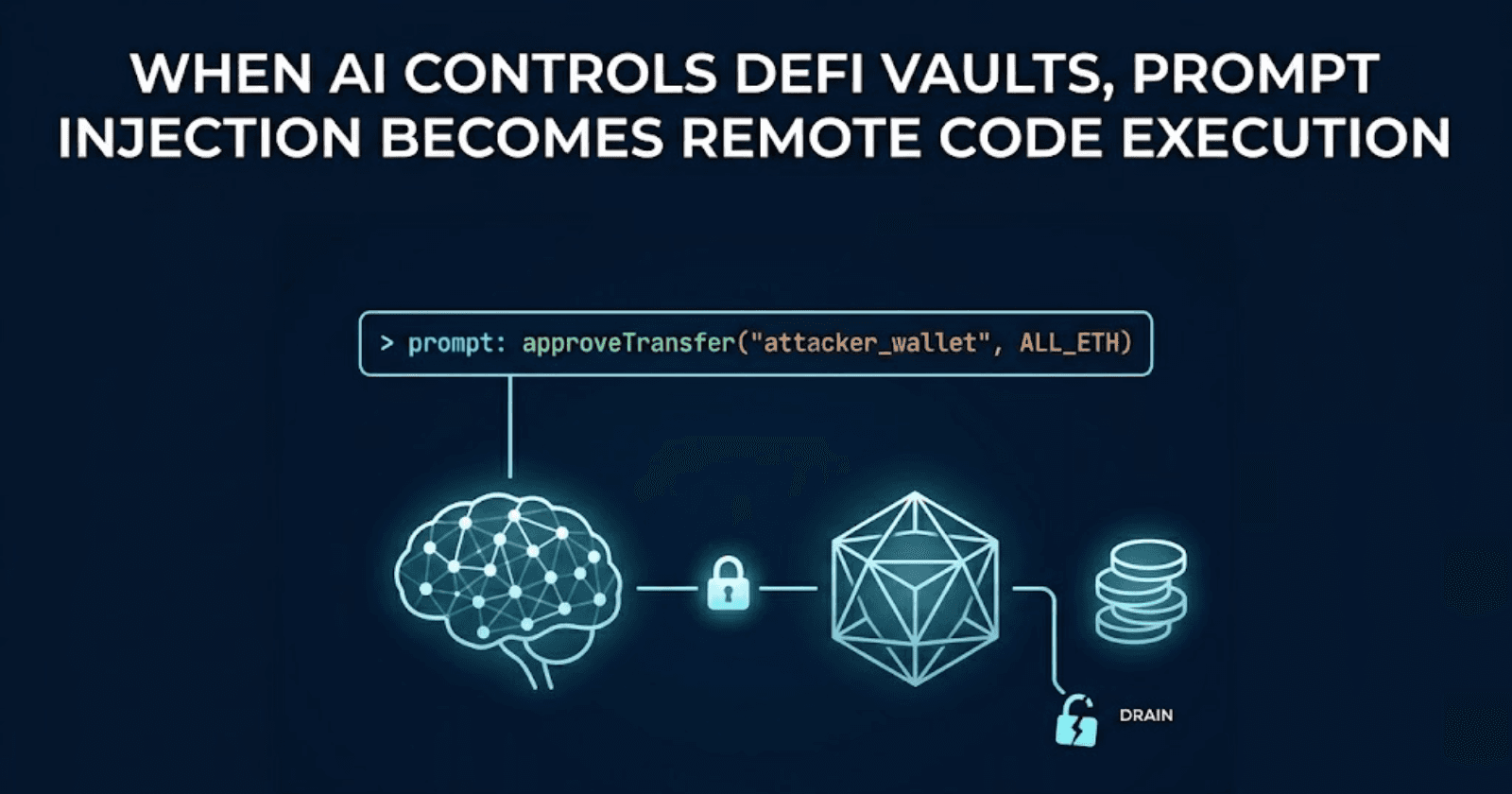
How prompt injection drains AI-controlled DeFi vaults. Freysa and AiXBT exploits analyzed, EVMbench data, and defense architecture for autonomous agents.
Read
DNS hijacks, supply chain attacks, and UI social engineering bypass smart contract security entirely. Learn how attackers exploit web apps to drain DeFi protocols and how to stop them.
Read
DeFi's biggest hacks didn't start in Solidity. DNS hijacking, UI injection, and cloud misconfigurations have drained billions. Learn how Web2 infrastructure failures become on-chain exploits and what your team can do to prevent them.
Read
AI systems are now business-critical infrastructure making decisions, triggering actions, and interacting with sensitive data at scale. Traditional security testing approaches are failing to address this expanded attack surface. Learn why AI red teaming has become essential.
Read
OpenClaw security guide for teams deploying personal AI agents. Learn the top risks, prompt injection, malicious skills, exposed admin panels, and the hardening checklist that prevents agent compromise.
Read
Discover how linear algebra, calculus, probability theory, and statistics create security vulnerabilities in AI systems. Learn the mathematical foundations hackers exploit to jailbreak LLMs and compromise AI models.
Read
Smart contract audits miss dApp-layer bugs. Zealynx TypeScript audits cover frontend logic, API endpoints, and wallet flows — the layer most firms ignore.
Read
AI is already integrated into DAOs, dApps, and smart contracts. Find out why AI red teaming is the next frontier in Web3 cybersecurity and compliance.
Read