Back to Blog 
Security ChecklistAuditDeFi
Base OP Stack Security Audit: 29 Checks EVM Equivalence Hides
"EVM equivalent" is the most dangerous phrase in L2 security.
Developers hear it from the OP Stack documentation, repeat it in architecture reviews, and use it to justify deploying L1 contracts to Base without modification. The logic feels airtight: if Base runs the same opcodes, the same Solidity, the same execution client (
op-geth), then the same contracts should just work.They don't.
Base's OP Stack architecture introduces divergences in block timing, gas economics, transaction origin semantics, cross-domain message authentication, and state finality that silently break assumptions baked into contracts designed for Ethereum mainnet. A
block.number-based cooldown that enforces three hours on L1 enforces thirty-three minutes on Base. A tx.origin check that gates admin access on L1 passes for an aliased attacker address on a deposit transaction. A gas estimation that accounts for execution cost but ignores the L1 data fee underprices every transaction on the network.These aren't hypothetical edge cases. They are the actual attack surface that separates a secure Base deployment from a drained protocol.
This guide breaks down the specific architectural divergences, known vulnerability classes, bridging mechanics, and tooling configurations that auditors and developers must account for when building or reviewing smart contracts on Base. The goal: a deployment where every L2-specific assumption is documented, tested, and hardened — not one where "EVM equivalent" substitutes for actual security analysis.
Understand the OP Stack execution model
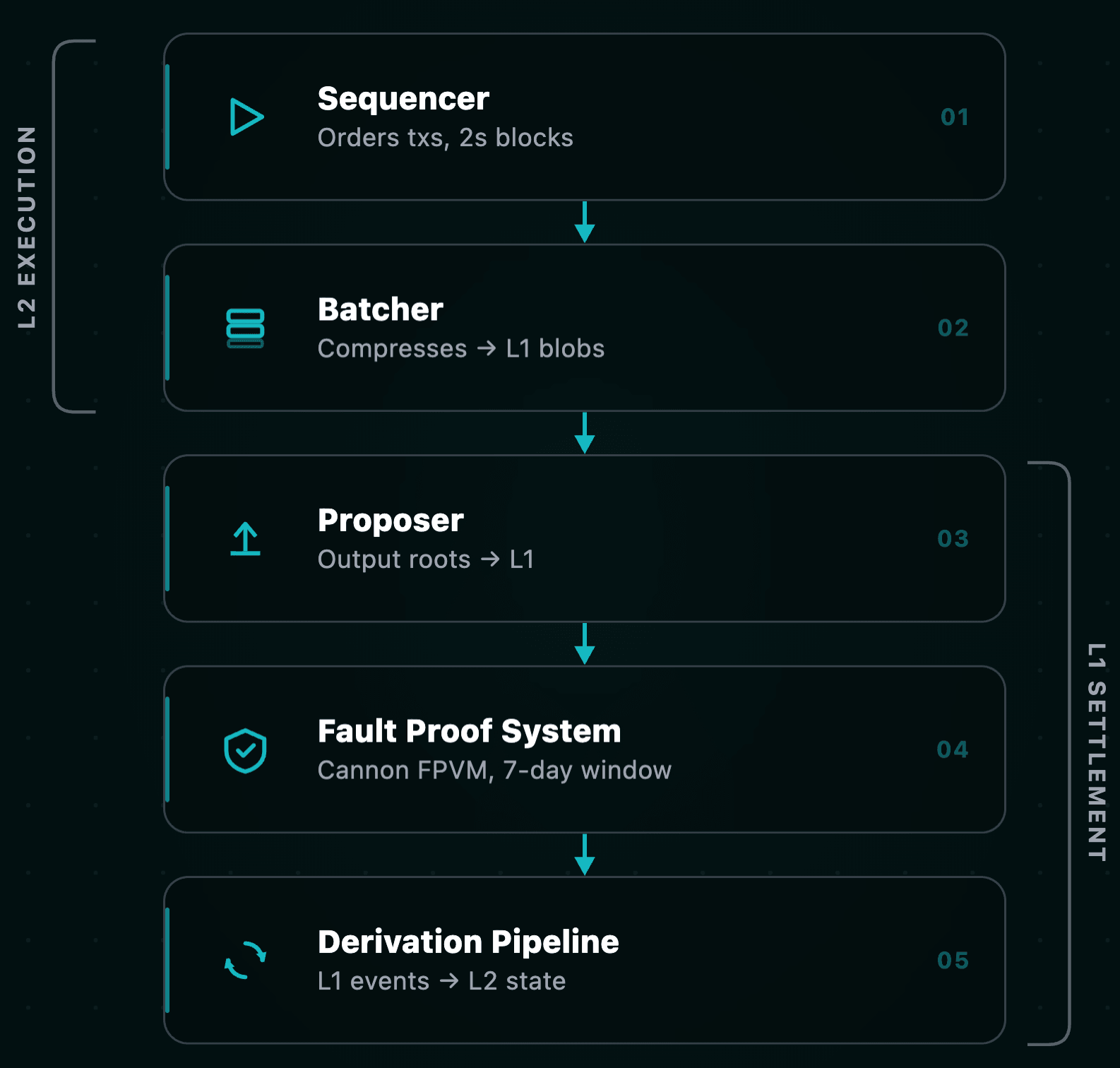
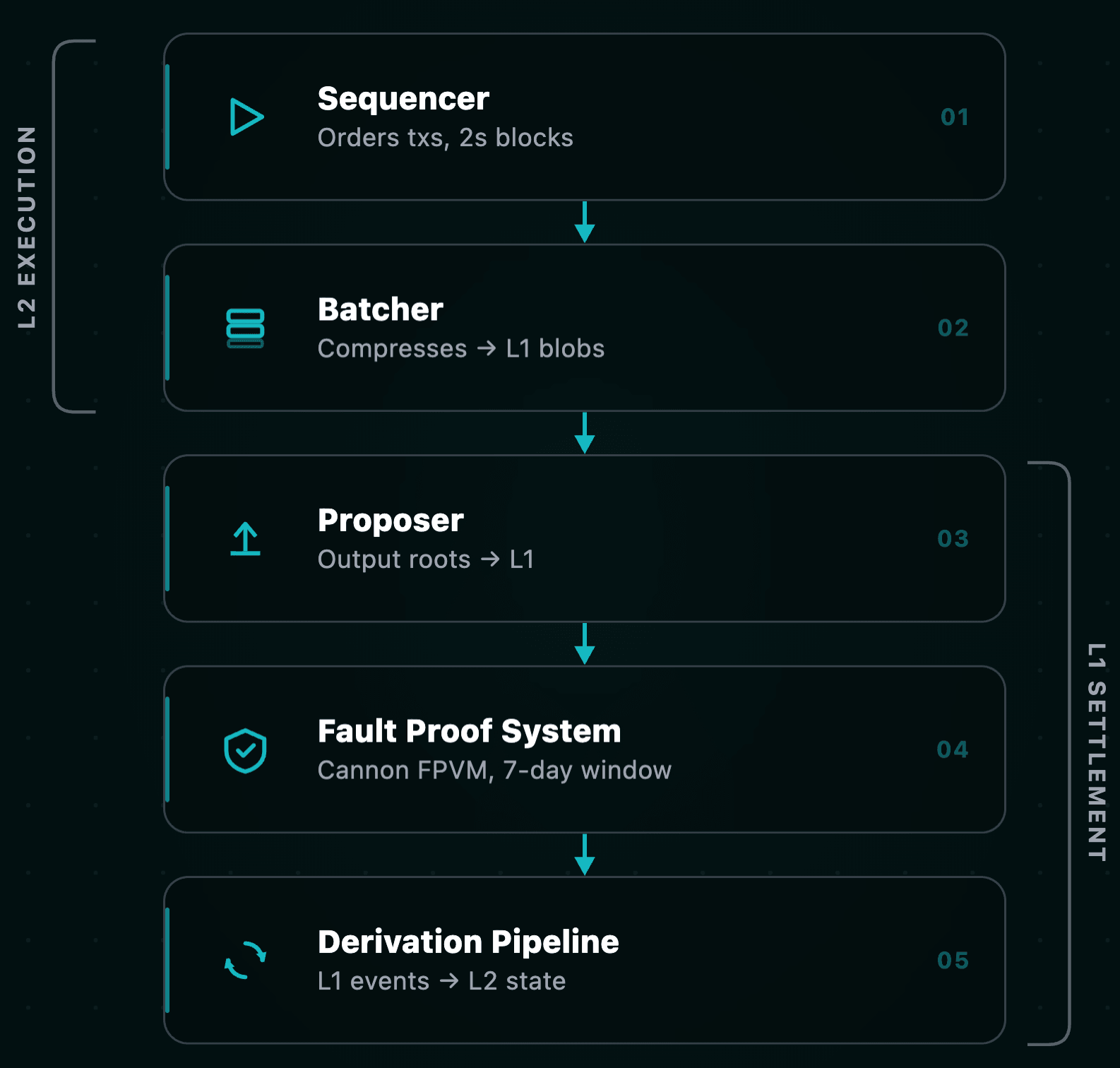
Base is an optimistic rollup built on Optimism's OP Stack, launched on Ethereum mainnet in August 2023 by Coinbase. The architecture separates execution from settlement across several distinct components:
- Sequencer — A single, Coinbase-operated node that orders transactions, produces L2 blocks every 2 seconds (with Flashblocks targeting 200ms pre-confirmation), and submits compressed batches to Ethereum. The sequencer cannot steal funds but has unilateral power over transaction ordering and censorship.
- Batcher — Compresses L2 transaction data and posts it to Ethereum L1. Since the Dencun upgrade (EIP-4844), Base uses blob-carrying transactions for data availability, cutting L1 posting costs dramatically versus calldata.
- Proposer — Submits output roots (L2 state commitments) to L1. Since October 2024, proposing is permissionless — anyone can submit via the
DisputeGameFactorycontract with a 0.08 ETH bond. - Fault proof system — Uses the Cannon FPVM (a MIPS-based instruction-level execution environment) to replay any L2 state transition on-chain. Dispute resolution follows an interactive bisection game that narrows disagreements to a single instruction step.
- Derivation pipeline — The
op-nodemonitors L1 forTransactionDepositedevents, deposit transactions, and batch data. It deterministically reconstructs L2 chain state from L1.
The security model is optimistic: L2 state transitions are assumed valid unless actively challenged during the dispute window. Every component in this pipeline — sequencer ordering, batch posting latency, fault proof timing, derivation determinism — introduces assumptions that contracts can violate.
Map the opcode and state divergences
Post-Bedrock, the OP Stack achieves EVM equivalence by running a minimally modified Ethereum execution client. "Minimally modified" still means modified. The following divergences are the ones that break real contracts:
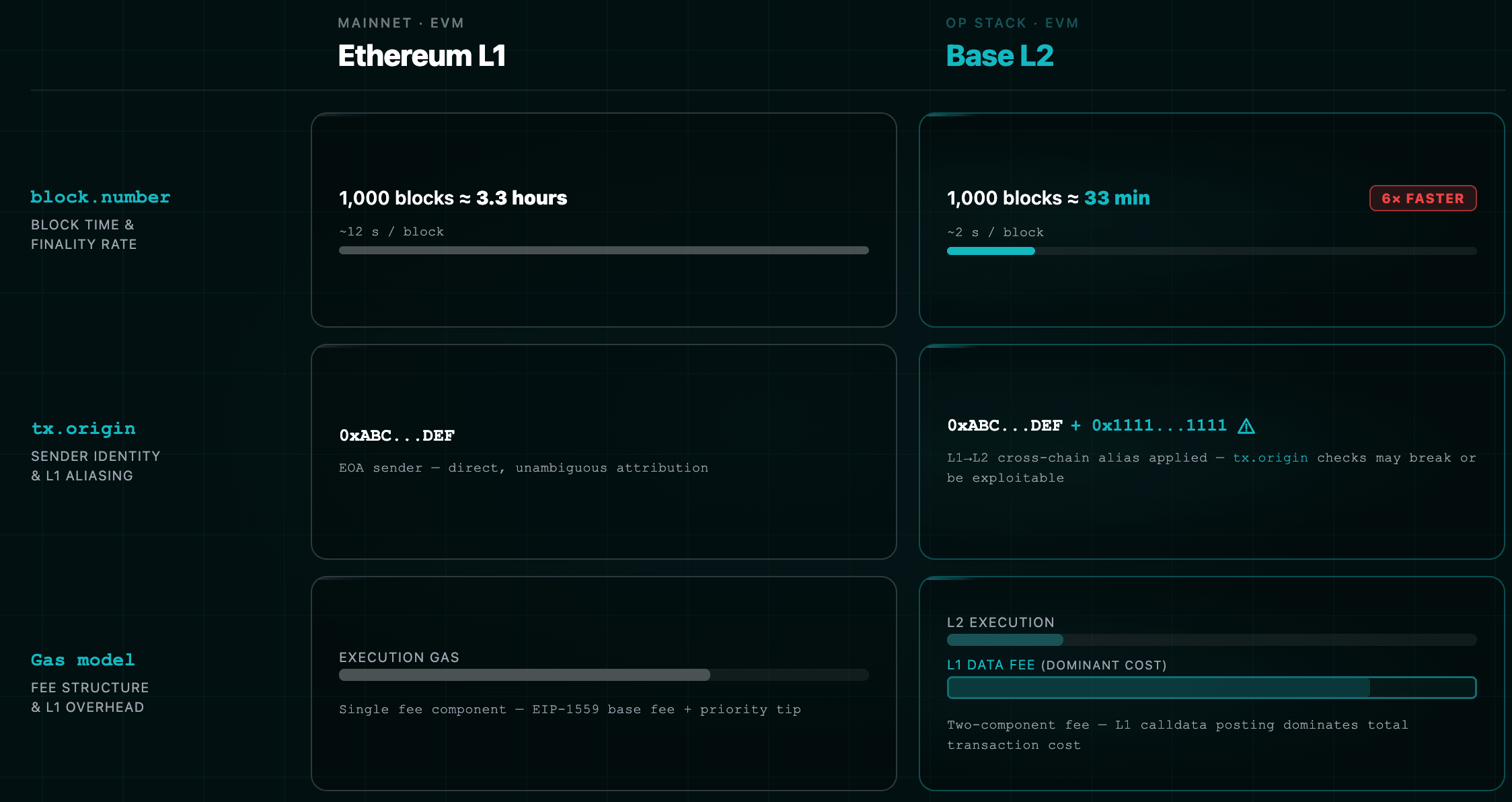
| Aspect | Ethereum L1 | Base L2 | Audit implication |
|---|---|---|---|
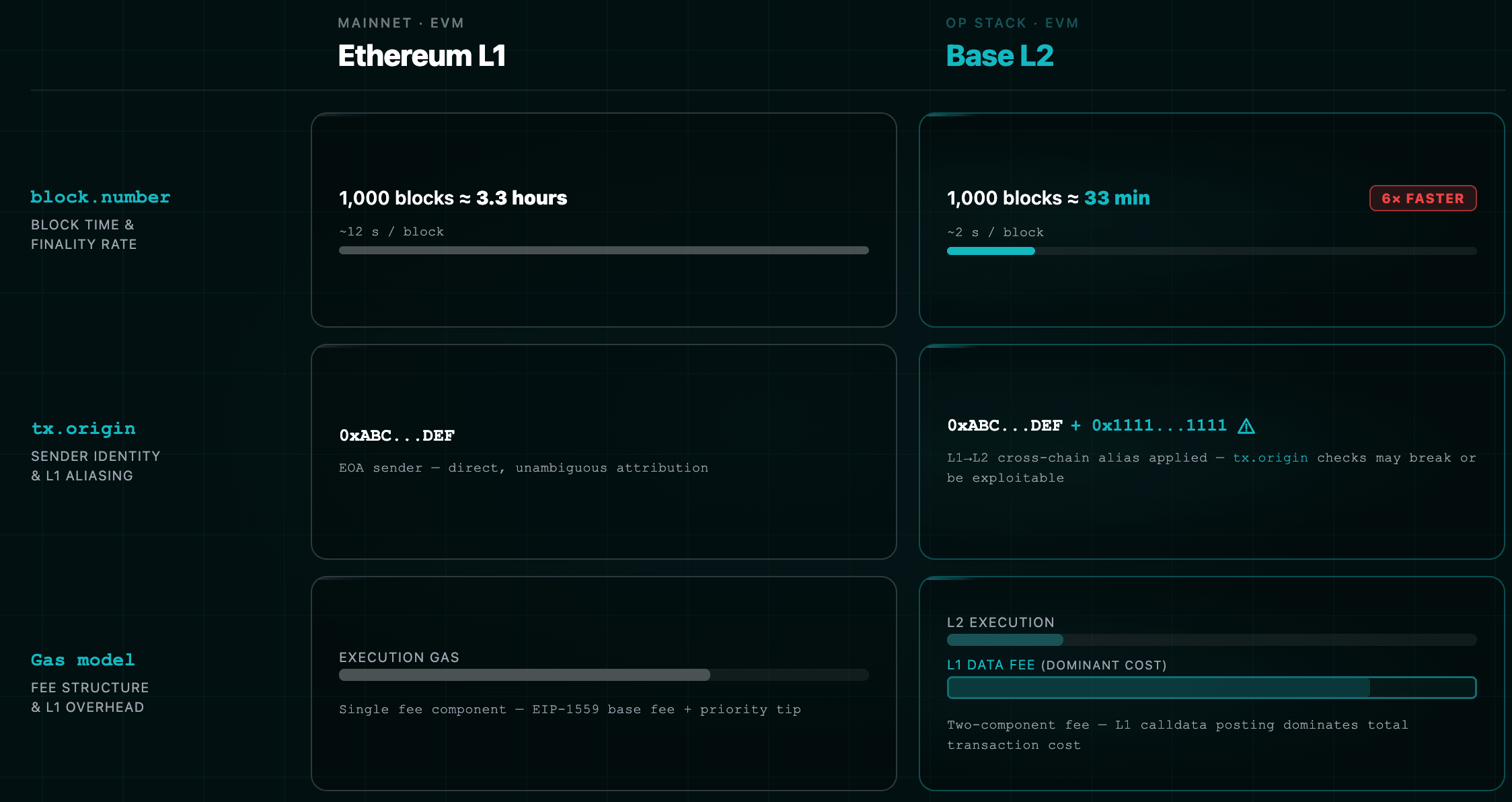
block.number | L1 block number (~12s blocks) | L2 block number (2s blocks) | A 1,000-block delay = ~3.3 hours on L1 but ~33 minutes on Base. Any block-denominated time logic must be reviewed. |
block.timestamp | Set by L1 validators | Set by the sequencer (monotonic, bounded by max_sequencer_drift from L1 origin) | Sequencer has more timestamp influence than L1 validators. Safer than block.number for time logic, but not manipulation-proof. |
tx.origin | Sender's EOA | For L1→L2 deposit transactions, aliased by adding 0x1111000000000000000000000000000000001111 | Any tx.origin-based access control breaks on cross-domain deposits. Normal L2 transactions are unaffected. |
PREVRANDAO | Beacon chain randomness (post-Merge) | Pseudo-random value derived from L1 RANDAO at the corresponding L1 origin block | Updates at L1 cadence (~12s), not L2 cadence (2s). Deterministic from the sequencer's perspective. Never use for security-critical randomness. |
COINBASE | Block proposer address | L2 sequencer fee wallet address | Static between blocks. Not a randomness source. |
| Gas model | Single execution fee | Dual fee: L2 execution gas + L1 data fee | L1 data fee often dominates total cost. Use GasPriceOracle at 0x420...000F for estimation. |
| Block time | ~12 seconds | 2 seconds | 6x faster block production. Vesting schedules, governance timelocks and cooldowns expressed in blocks behave completely differently. |
CREATE determinism | Standard | Same deployer + same nonce = same address, but different bytecode is possible across L1/L2 | Never assume address equivalence implies code equivalence across chains. |
| Pre-EIP-155 transactions | Supported (legacy) | Not supported | Replay protection is mandatory. Old unsigned transaction formats are rejected. |
| Base fee destination | Burned (deflationary) | Accumulated in BaseFeeVault (0x4200...0019) | Protocols assuming deflationary ETH mechanics on L2 will have incorrect token economics models. |
Audit actions
- Flag every
block.numberreference. If used for time calculations, recommend replacement withblock.timestamp. - Flag every
tx.origincheck. Verify whether the contract can receive L1→L2 deposits and whether aliasing is handled. See our deep dive ontx.originphishing vulnerabilities. - Verify gas estimation includes L1 data fees. Call
GasPriceOracle.getL1Fee(bytes)with the unsigned RLP-encoded transaction to get the actual cost. - Access L1 state through the
L1Blockpredeploy at0x4200...0015, not through opcodes. Note that L1Block values update once per L1 block (~12s) — they are inherently stale relative to the L1 tip.
Identify the predeploy attack surface
Base inherits the full OP Stack predeploy ecosystem at the
0x4200... address namespace. These are not optional libraries — they are system-level contracts that govern bridging, fee collection, and chain state. Any protocol integrating with them must understand their interfaces and trust assumptions.| Contract | Address | Purpose |
|---|---|---|
L1Block | 0x4200...0015 | Exposes L1 block info (number, timestamp, basefee, hash, blobBaseFee). Updated once per epoch. |
L2CrossDomainMessenger | 0x4200...0007 | Handles authenticated cross-chain message relay from L1→L2. |
L2StandardBridge | 0x4200...0010 | Standard bridge for ETH and ERC-20 deposits/withdrawals. |
L2ToL1MessagePasser | 0x4200...0016 | Stores withdrawal commitments. Its storage root feeds into the output root used in fault proofs. |
GasPriceOracle | 0x4200...000F | L1 data fee estimation via getL1Fee(bytes). |
SequencerFeeVault | 0x4200...0011 | Collects sequencer priority fees. |
BaseFeeVault | 0x4200...0019 | Collects L2 base fees (not burned). |
ProxyAdmin | 0x4200...0018 | Owner of all predeploy proxies. The entity controlling this contract can upgrade any predeploy. |
Critical detail: All predeploy contracts are upgradeable proxies. The
ProxyAdmin controls all of them. As of April 2025, upgrades approved by the required three parties (Base Security Council, BaseMultisig2, OpFoundationOperationsSafe) can be executed instantly — no timelock. This is a systemic trust assumption that every protocol built on Base inherits.Mitigate OP Stack fault proof vulnerabilities
Since Base inherits the OP Stack fault proof system wholesale, all vulnerabilities found in that system apply directly to Base. Three findings from 2024 deserve detailed attention:
Timer manipulation in bisection games
In March 2024, Offchain Labs (Arbitrum's development team) disclosed two critical vulnerabilities in the OP Stack fault proof system on testnet:
- Fraudulent root acceptance via timer inheritance: The "chess clock" mechanism in
FaultDisputeGameallowed a malicious actor to inherit timer credit from honest actors' claims through grandparent relationships. By submitting a fraudulent root, waiting for an honest challenge, then responding at the last second, the attacker caused the honest challenge to expire while the fraudulent root remained uncountered. A single block of L1 censorship at the critical moment was sufficient to force acceptance of an invalid state root. - Honest root rejection: The same timer manipulation worked in reverse — an attacker could defeat a correct root claim, blocking valid withdrawals.
Both were patched before mainnet deployment. The lesson: bisection game timing logic is a critical attack surface that requires formal analysis. Any protocol interacting directly with the dispute game contracts must verify that the resolution logic has been audited against timing attacks.
GameType validation bypass
An audit finding revealed that a malformed
GameType (a uint32 used to select the dispute game implementation) could pass through validation checks in OptimismPortal.sol, potentially routing withdrawals through a game with weaker security properties.Blob data handling in op-challenger
The off-chain
op-challenger mishandled transactions involving EIP-4844 blob data, causing divergence between on-chain and off-chain execution traces in Cannon. Since fault proofs depend on identical execution, this divergence could allow a malicious proposer to construct an unchallengeable invalid state.Audit actions
- Do not build withdrawal logic that bypasses the 7-day dispute window. The fault proof system is the only mechanism preventing invalid state roots from draining the bridge.
- Monitor OP Stack security disclosures. Fault proof vulnerabilities affect every chain on the Superchain, including Base.
- If your protocol interacts with
DisputeGameFactoryorOptimismPortal2, audit forGameTypevalidation and ensure your logic handles game resolution edge cases (e.g., the Guardian shifting toPermissionedDisputeGameunder attack).
Audit the bridge integration layer
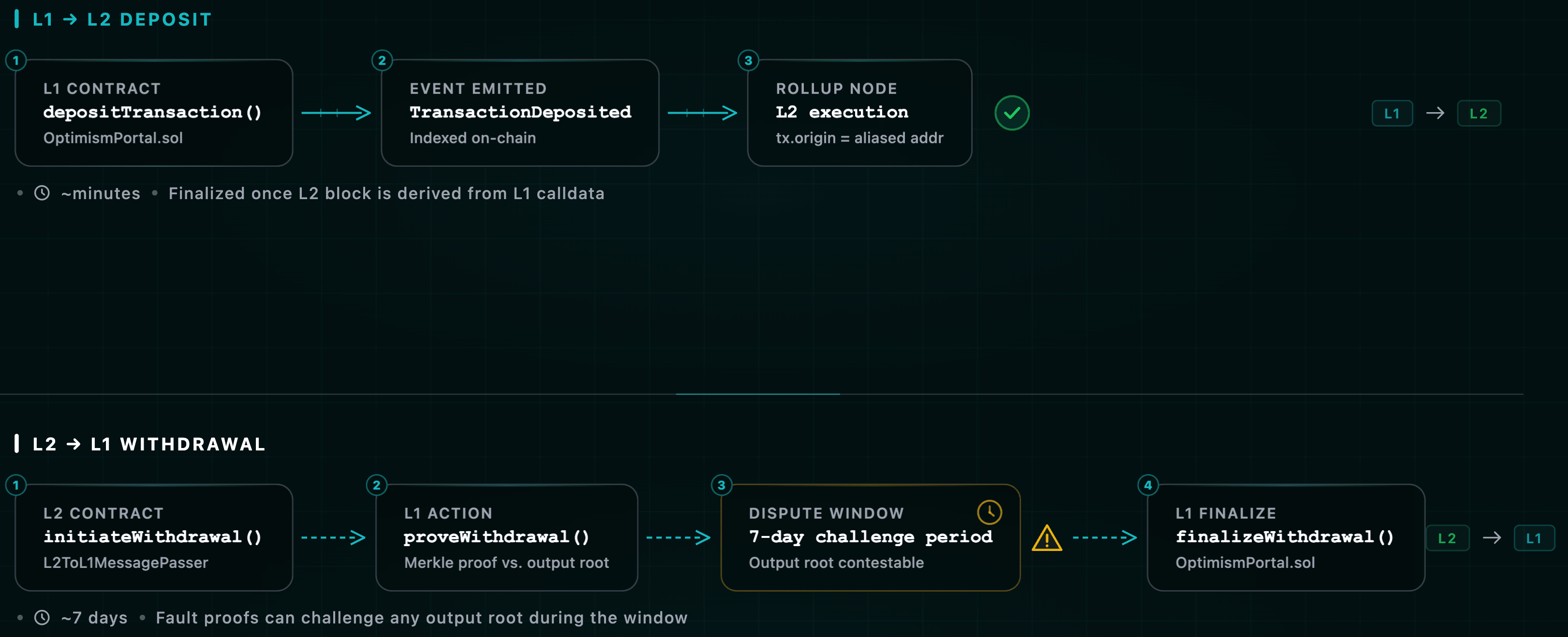
Bridging infrastructure is the highest-value attack surface in any L2 ecosystem. Base uses the standard OP Stack cross-domain messaging protocols. The mechanics are asymmetric: deposits are fast and guaranteed; withdrawals are slow and fraud-proof-dependent.
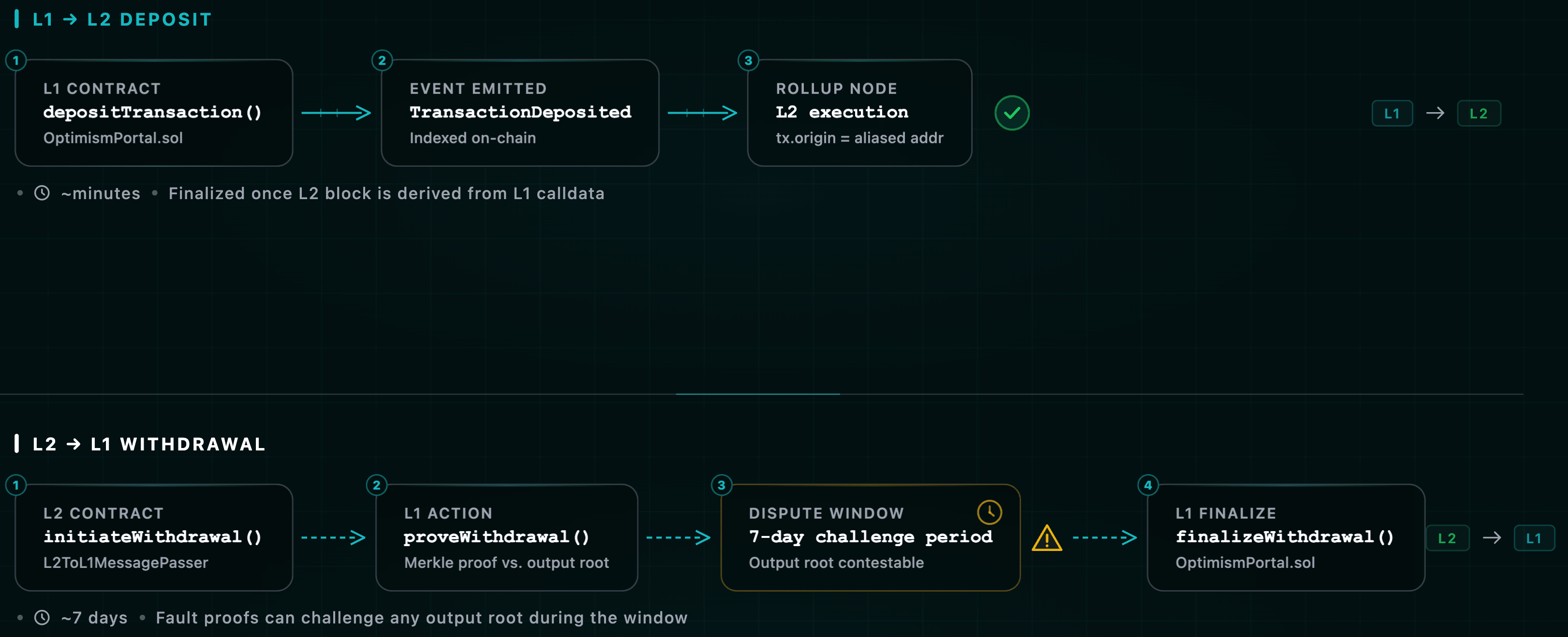
L1→L2 deposits
Flow: User calls
depositTransaction() on OptimismPortal (L1) → emits TransactionDeposited event → op-node derives deposit transaction → L2 execution engine processes it.Security properties:
- Deposits are guaranteed inclusion at the start of each epoch's first L2 block.
- Deposit transactions lack cryptographic signatures (
v,r,sare zeroed) — authenticity is guaranteed by L1 inclusion and canonical derivation. - Authentication uses a cryptographically derived
sourceHash:keccak256(bytes32(uint256(0)), keccak256(l1BlockHash, bytes32(uint256(l1LogIndex)))). - Address aliasing applies: when an L1 contract sends a deposit, its address is offset by
0x1111...1111on L2. Without this, an attacker could deploy a contract at the same address on L1 and L2, spoof identity cross-chain, and bypass authorization.
Known edge case: If an L1 contract deposits ETH via
OptimismPortal and the corresponding L2 execution reverts (logic error, insufficient gas), the ETH is minted to the aliased sender address on L2. If the L1 sender contract cannot control its aliased L2 counterpart, those funds are permanently stranded.L2→L1 withdrawals
Flow (3-step, all finalized on L1):
- Initiate: Call
L2ToL1MessagePasser.initiateWithdrawal()on L2. Stores a withdrawal hash in the contract's Merkle-Patricia trie. - Prove: After the output root containing the withdrawal is proposed on L1, submit a Merkle proof to
OptimismPortal2.proveWithdrawalTransaction(). - Finalize: After the dispute window elapses (~7 days) and the state root is confirmed, call
OptimismPortal2.finalizeWithdrawalTransaction().
Minimum withdrawal time: ~7 days from proof submission.
Security layers:
- The Guardian role (Optimism Security Council) can reject finalized roots during an airgap window after game resolution.
DelayedWETHholds dispute game bonds with a payout delay for redirection if a game resolves incorrectly.- The Guardian can shift the system to
PermissionedDisputeGameunder active attack.
Cross-domain message authentication
The
CrossDomainMessenger system provides authenticated cross-chain function calls in both directions. Critical security considerations:- Replay protection — Messages include a nonce. Verify nonce handling is correct in both messenger contracts.
- Failed message replay — Failed messages can be replayed on the target chain. Target contracts must be idempotent to handle this safely.
- Sender authentication —
xDomainMessageSender()returns the authenticated cross-chain sender, but only when called by the messenger contract itself. Contracts must verifymsg.sender == address(messenger)before trusting this value. - Gas estimation — Cross-domain messages must budget for both L1 and L2 execution costs. Under-gassed messages fail and enter the replay queue.
Audit actions
- Verify every cross-domain message handler checks the aliased sender address before executing privileged logic.
- Test deposit failure scenarios. What happens when L2 execution of a deposit reverts? Are funds recoverable?
- Confirm withdrawal handlers are idempotent. A withdrawal proven against an invalidated root must be re-provable against a valid root without double-spending.
- Implement rate limits and circuit breakers on bridge-connected contracts. A bridge exploit should not cascade into total protocol insolvency. See our bridge security checklist for 100+ specific checks.
- If integrating third-party bridges (Across, Stargate, Hop), audit their specific trust model: key custody, challenge periods, oracle dependencies, and liquidity pool solvency assumptions.
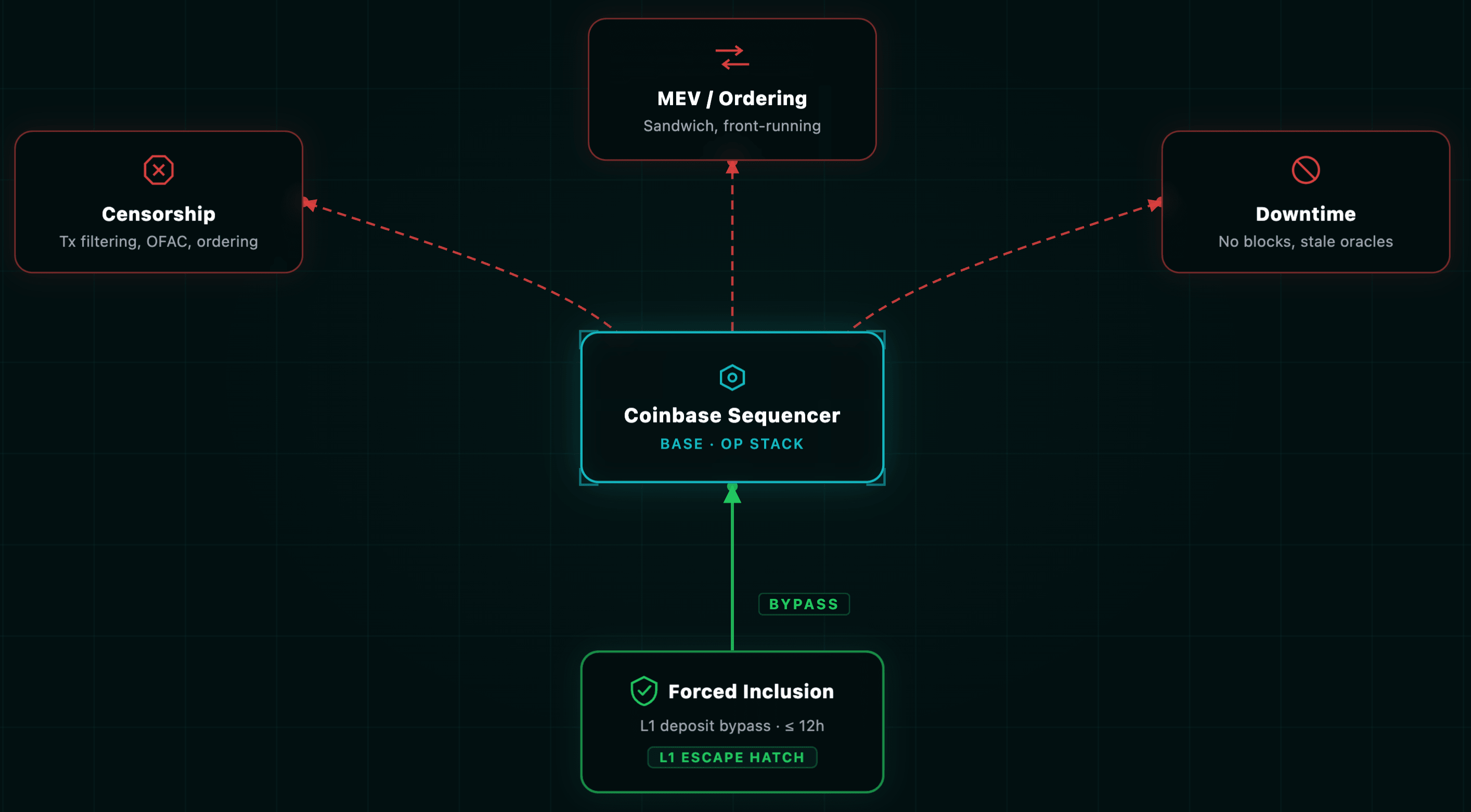
Defend against sequencer-level threats
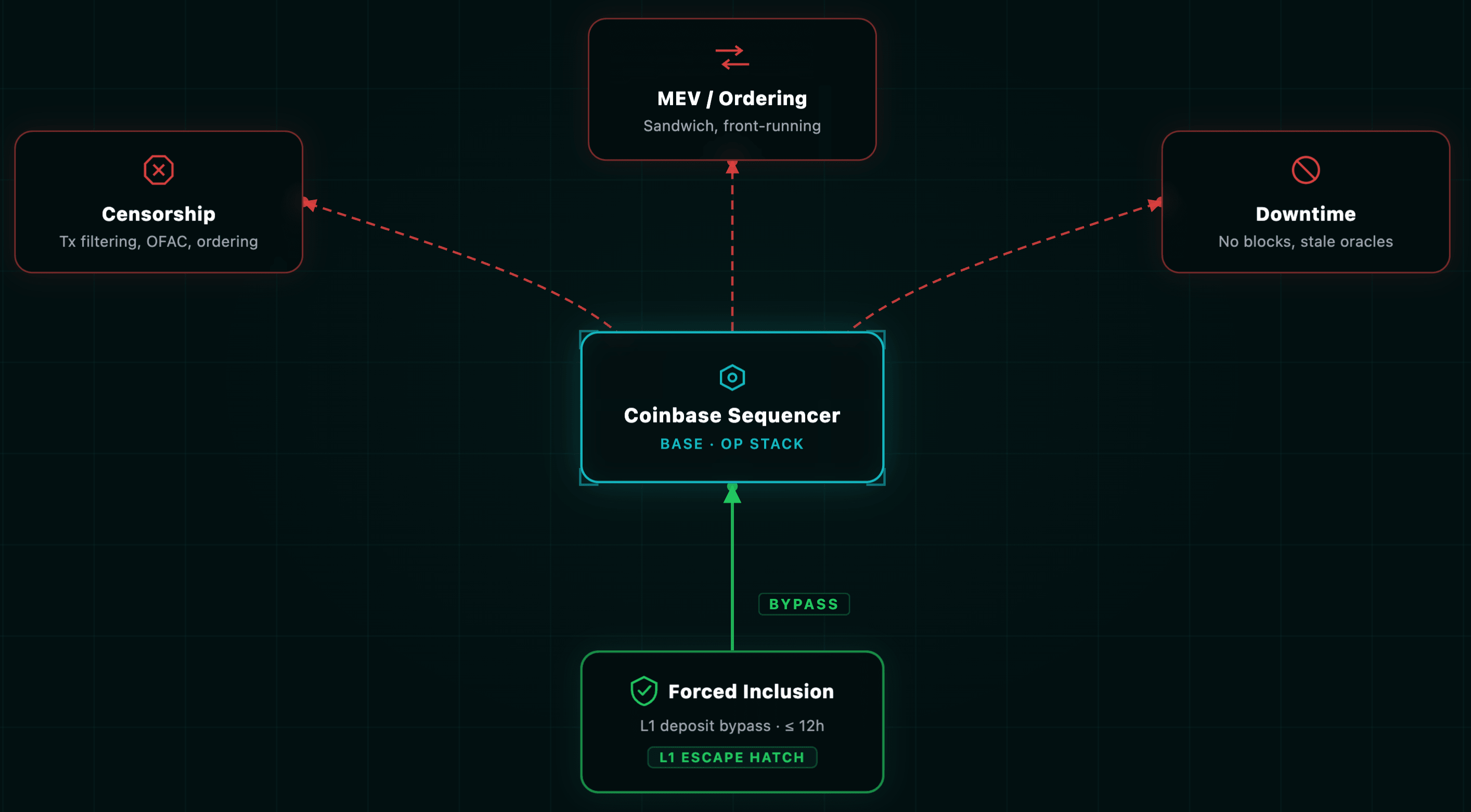
Base operates a single centralized sequencer run by Coinbase. This is a structural constraint, not a bug — but it produces a specific threat model that contracts must be designed around.
Censorship and ordering
- The sequencer has unilateral transaction ordering power. Assume sandwich attacks and front-running are possible at the infrastructure level. For mitigation strategies, see our guide on MEV protection.
- OFAC/regulatory filtering at the sequencer is possible. Transactions from sanctioned addresses may be refused.
- The sequencer cannot steal funds, but censorship of time-sensitive transactions (oracle updates, liquidations, auction bids, governance votes) can cause indirect fund loss.
Downtime
- If the sequencer goes offline, no new L2 transactions are processed. On August 5, 2025, Base experienced a ~33-minute block production halt at block 33,792,704.
- A subtler failure mode: the sequencer continues producing L2 blocks and issuing pre-confirmations but fails to post batches to L1. This creates a state divergence where users see "confirmed" transactions that have no L1 data availability backing.
- During prolonged downtime, price oracles stale out, liquidity indexes become volatile, and leveraged positions become vulnerable to cascading liquidations the instant the network resumes.
Forced inclusion
Users can bypass the sequencer entirely by submitting transactions to
OptimismPortal.depositTransaction() on L1. The protocol guarantees these deposit transactions appear at the start of the corresponding epoch's first L2 block. If the sequencer omits them, the output root becomes invalid and will be challenged.The forced inclusion path has a latency defined by
FORCE_INCLUSION_PERIOD — up to 12 hours. Any protocol-critical flow (liquidations, auctions, governance finalization) must be designed to tolerate this delay.Audit implication for commit-reveal schemes: The reveal window must never be shorter than L1 confirmation depth +
FORCE_INCLUSION_PERIOD. Otherwise, a validator with L1 censorship capability can front-run the reveal via the L1 deposit path.Audit actions
- Test sequencer downtime scenarios: What happens to your protocol if no L2 blocks are produced for 1 hour? 12 hours? 24 hours?
- Design graceful degradation: If oracle updates or keeper transactions stop arriving, implement fallback logic with extended execution windows.
- Do not assume ordering fairness. Unlike L1 where block builders compete, Base's single sequencer controls the mempool unilaterally.
Get the DeFi Protocol Security Checklist
15 vulnerabilities every DeFi team should check before mainnet. Used by 30+ protocols.
No spam. Unsubscribe anytime.
Harden proxy upgrade paths
On L2 where gas is cheap, upgrade transactions are inexpensive — and so are malicious upgrades. The OP Stack uses the Transparent Proxy pattern with a separated
ProxyAdmin authority to resolve function selector collisions. For a comprehensive overview, see our proxy upgradeability security checklist and upgrade patterns security guide.On Base Mainnet, the
ProxyAdmin resides at 0x4200...0018. The L1 bridge administrator contracts are controlled by Gnosis Safe multisigs. The Base Mainnet ProxyAdmin owner is 0x7bB41C3008B3f03FE483B28b8DB90e19Cf07595c.Upgrade-specific vulnerability classes
- Unguarded initializers: Proxies cannot use constructors. If the
initialize()function lacks aninitializermodifier, an attacker can re-initialize the contract post-deployment, overwriting permission variables. This is one of the most common access control failures in deployed contracts. - Storage layout collisions: Upgrades must maintain exact slot ordering from previous implementations. Reordering, removing, or resizing state variables corrupts persistent state.
- Privilege conflation: The
ProxyAdminowner must never coincide with the protocol's functional manager. A social-engineeredupgradeToAndCallcan redirect the implementation to an attacker-controlled contract.
Audit actions
- Run
slither-check-upgradeabilityon all proxy contracts to detect storage layout violations automatically. - Verify initializers are protected and cannot be re-called after deployment.
- Confirm no
selfdestructexists in implementation contracts (even post-EIP-6780). - Implement a timelock for your protocol's own upgrades, independent of whether Base system contracts have one. Give users exit time before parameter changes take effect.
- Monitor OP Stack network upgrades (Bedrock, Ecotone, Fjord, Jovian). Each can change gas pricing, fee calculation, and fault proof behavior. Test your contracts on testnet before mainnet activation.
Configure auditing tools for Base
Because Base is EVM-equivalent at the bytecode level, standard Solidity auditing tools work with minimal configuration. The bytecode is identical — tools analyze source and bytecode, not the chain runtime. But automated tools do not catch L2-specific issues without explicit configuration.
Tool matrix
| Tool | Type | Base-specific notes |
|---|---|---|
| Slither | Static analysis | Works out of the box. Includes an Optimism-specific deprecated predeploy detector. Write custom detectors for block.number misuse, missing L1 data fee accounting, and tx.origin aliasing. |
| Foundry | Testing, fuzzing, forking | Use forge test --fork-url https://mainnet.base.org --chain-id 8453 for live-state testing. Use vm.createSelectFork() to pin tests to specific historical blocks for exploit reproduction. |
| Mythril | Symbolic execution | Chain-agnostic bytecode analysis. Slower than Slither but higher-confidence on deep execution paths (reentrancy, integer edge cases). |
| Echidna | Property-based fuzzing | Define economic invariants and let Echidna attempt to break them. Low false-positive rate compared to static analysis. Can fork Base state. For more on fuzzing, see our fuzzing and formal verification guide. |
| Certora Prover | Formal verification | Chain-agnostic CVL rule verification. Recommended for high-value contracts (bridges, lending protocols, governance) requiring mathematical certainty. |
What automated tools miss
Manual review is mandatory for:
- Cross-domain message authentication failures
- Address aliasing mishandling on deposit paths
- Sequencer dependency assumptions in time-sensitive logic
- L1 data fee impact on protocol economics
- Predeploy interaction correctness (especially
L1Blockstaleness) - Withdrawal flow correctness and idempotency under fault proof invalidation
For a broader perspective on layered security approaches, see our defense-in-depth workflow.
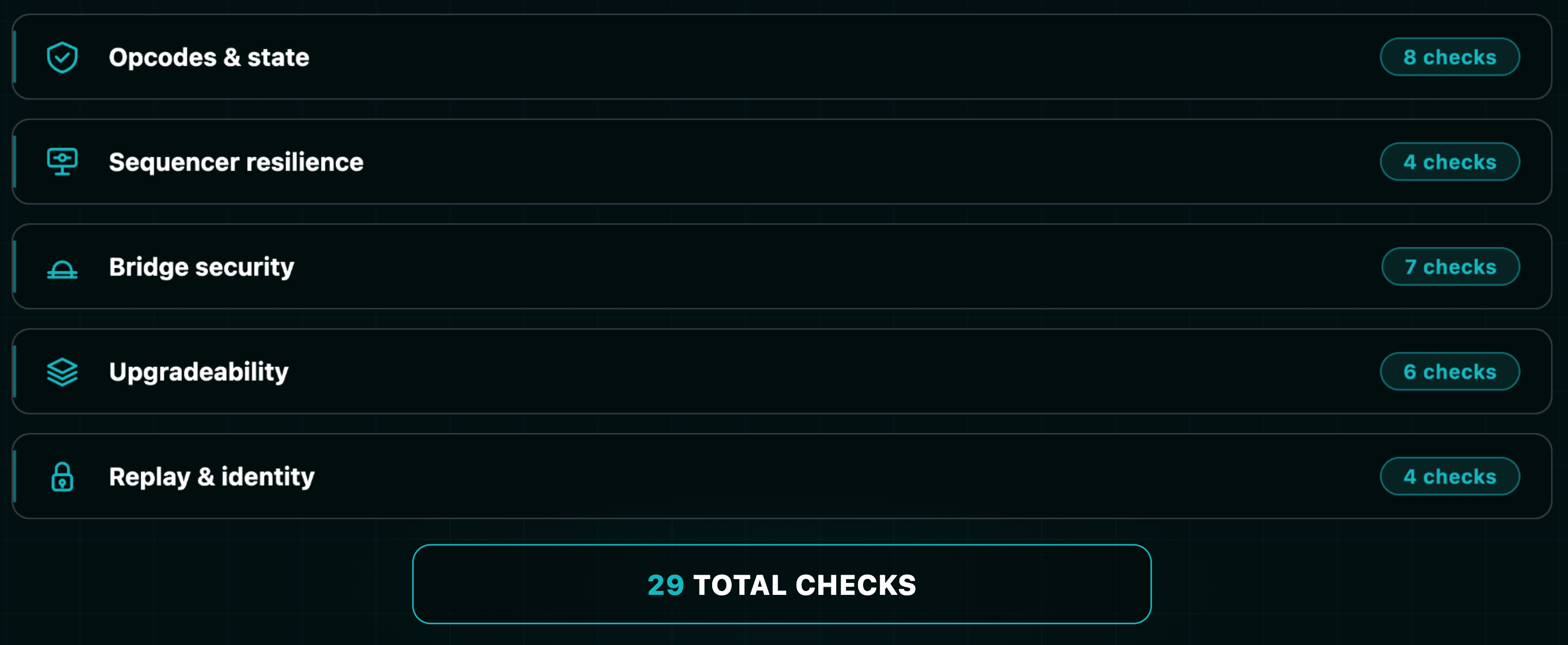
Apply the L2 security checklist
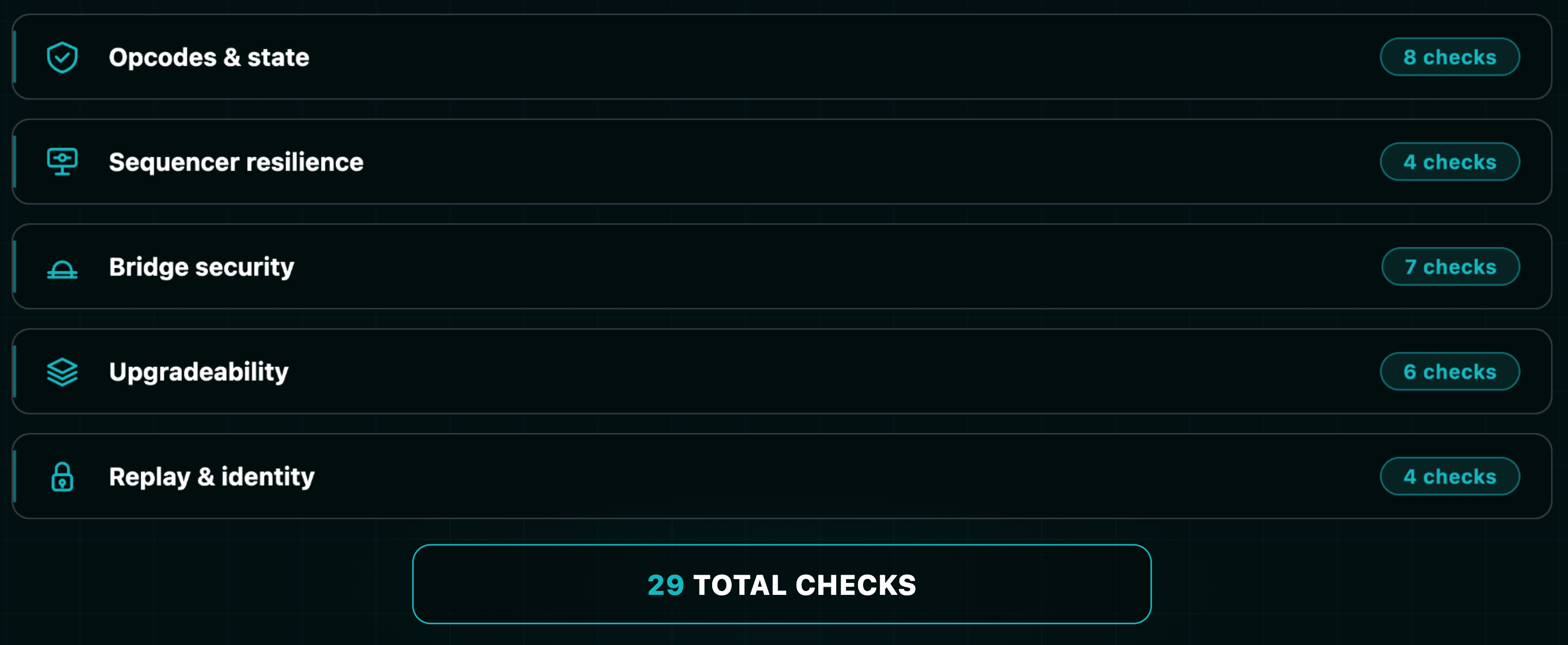
This is the consolidated checklist. Every item maps to a specific divergence or vulnerability class documented above. Use this alongside our pre-audit checklist for maximum coverage.
Opcodes and state
- All
block.numberreferences reviewed for L2 timing (2s blocks vs. 12s) -
block.timestampused instead ofblock.numberfor time-dependent logic - L1 state accessed via
L1Blockpredeploy, not opcodes - L1Block staleness accounted for (values lag L1 tip by up to ~12s)
-
PREVRANDAOnot used for security-critical randomness -
tx.originaliasing handled for L1→L2 deposit paths - Gas estimation includes L1 data fee via
GasPriceOracle.getL1Fee() - No assumptions about deflationary base fee mechanics on L2
Sequencer resilience
- Protocol tolerates sequencer downtime (1h, 12h, 24h scenarios tested)
- Liquidation/auction/governance flows tolerate 12-hour forced inclusion delay
- Oracle fallback logic for stale price feeds during downtime
- No assumption of transaction ordering fairness
Bridge security
- Cross-domain message handlers verify
msg.sender == messengerbefore trustingxDomainMessageSender() - Address aliasing correctly applied/de-aliased in authentication logic
- Deposit failure scenarios tested (L2 execution revert, insufficient gas)
- Withdrawal handlers are idempotent across fault proof invalidation cycles
- 7-day withdrawal delay respected — no UX or logic assumes fast L2→L1 settlement
- Rate limits and circuit breakers on bridge-connected contracts
- Third-party bridge trust models audited independently
Upgradeability
-
slither-check-upgradeabilityrun on all proxy contracts - Initializers protected by
initializermodifier, not re-callable - Storage layout compatibility verified across all upgrade versions
- No
selfdestructin implementation contracts - Protocol-level timelock on upgrades, independent of system-level controls
- Contracts tested against upcoming OP Stack upgrades on testnet
Replay and cross-chain identity
- EIP-155 enforced — chain ID (8453) embedded in all signed payloads
- Cross-chain message nonces validated, with expiration deadlines
- No assumption that identical addresses on L1 and L2 imply identical bytecode
- Commit-reveal windows account for L1 confirmation depth +
FORCE_INCLUSION_PERIOD
Reference: Key addresses (Base mainnet)
| Contract | Address |
|---|---|
| L2CrossDomainMessenger | 0x4200000000000000000000000000000000000007 |
| L2StandardBridge | 0x4200000000000000000000000000000000000010 |
| SequencerFeeVault | 0x4200000000000000000000000000000000000011 |
| L1Block | 0x4200000000000000000000000000000000000015 |
| L2ToL1MessagePasser | 0x4200000000000000000000000000000000000016 |
| ProxyAdmin | 0x4200000000000000000000000000000000000018 |
| BaseFeeVault | 0x4200000000000000000000000000000000000019 |
| GasPriceOracle | 0x420000000000000000000000000000000000000F |
| Base Chain ID | 8453 |
Get in touch
At Zealynx, we specialize in L2 smart contract security — the exact intersection of EVM mechanics, rollup architecture, and cross-chain trust boundaries where these vulnerabilities live. Whether you're deploying on Base, Optimism, or any OP Stack chain, our team audits for the L2-specific divergences that automated tools miss — request an audit.
Want to stay ahead with more in-depth analyses like this? Subscribe to our newsletter and ensure you don't miss out on future insights.
FAQ: Base L2 security audit
1. What is EVM equivalence, and why doesn't it guarantee security on Base?
EVM equivalence means that Base runs the same bytecode instructions and execution logic as Ethereum mainnet through a minimally modified execution client (
op-geth). However, equivalence applies only to opcode behavior — not to the surrounding chain environment. Block timing (2 seconds vs. 12 seconds), the dual gas fee model (L2 execution + L1 data fee), transaction origin aliasing on deposit transactions, and sequencer-controlled timestamps all differ from Ethereum L1. Contracts that rely on block-denominated time delays, tx.origin checks, or single-fee gas estimation will behave differently — or break entirely — on Base despite running identical bytecode.2. What is address aliasing on Base and how can it break access control?
Address aliasing is a safety mechanism applied to L1→L2 deposit transactions. When an L1 contract (not an EOA) sends a deposit to Base, the sender's address is offset by adding
0x1111000000000000000000000000000000001111. This prevents an attacker from deploying a contract at the same address on both L1 and L2 to spoof cross-chain identity. The problem arises when a smart contract uses tx.origin for access control: on a deposit transaction, tx.origin returns the aliased address, not the original L1 sender. Any tx.origin-based authorization check will fail or, worse, pass for an unintended address. Contracts receiving L1→L2 deposits must explicitly handle aliasing in their authentication logic.3. Why does `block.number` behave differently on Base than on Ethereum?
Ethereum L1 produces blocks approximately every 12 seconds, while Base produces blocks every 2 seconds — six times faster. This means any logic using
block.number to measure time durations will execute six times faster than intended. A 1,000-block cooldown that enforces ~3.3 hours on Ethereum mainnet enforces only ~33 minutes on Base. Vesting schedules, governance timelocks, auction windows, and rate-limiting logic all need to be converted from block-denominated to timestamp-denominated values. The fix is to use block.timestamp instead, which behaves consistently regardless of block production rate.4. What happens if the Base sequencer goes down — can it affect my protocol?
Yes. Base operates a single centralized sequencer run by Coinbase. If it goes offline, no new L2 transactions are processed. During downtime, price oracle feeds stale out, pending liquidations cannot execute, auction deadlines may pass without bids, and governance proposals may expire. When the sequencer resumes, the sudden processing of queued transactions can trigger cascading liquidations from stale prices. Protocols must implement graceful degradation: oracle staleness checks with fallback logic, extended execution windows for time-critical operations, and circuit breakers that pause sensitive functions when no new blocks arrive for a defined threshold. Users can still force-include transactions via L1 deposits, but with up to 12 hours of latency.
5. How does the dual gas fee model on Base affect smart contract economics?
Unlike Ethereum L1 where users pay a single execution gas fee, Base transactions incur two costs: L2 execution gas (cheap, similar to any L2) and an L1 data fee (for posting transaction data to Ethereum for data availability). The L1 data fee often dominates total transaction cost and fluctuates with Ethereum L1 gas prices and blob base fees. Protocols that hardcode gas assumptions, implement gas-based refund mechanisms, or estimate transaction costs without querying the
GasPriceOracle predeploy at 0x420...000F will systematically underprice operations. Call GasPriceOracle.getL1Fee(bytes) with the unsigned RLP-encoded transaction to get the accurate total cost. Additionally, L2 base fees are not burned (they accumulate in BaseFeeVault), which breaks any tokenomics model assuming deflationary ETH mechanics.6. What is the 7-day withdrawal delay on Base and can my protocol work around it?
The 7-day withdrawal delay is fundamental to the optimistic rollup security model. When withdrawing assets from Base to Ethereum L1, users must: (1) initiate the withdrawal on L2, (2) submit a Merkle proof on L1 after the output root is proposed, and (3) wait for the dispute window (~7 days) before finalizing. This window allows anyone to challenge an invalid state root through the fault proof system. No protocol should build logic that bypasses or shortens this delay — it is the only mechanism preventing a malicious proposer from draining the bridge with a fraudulent state root. If your users need faster L2→L1 liquidity, integrate a third-party fast bridge (Across, Stargate, Hop) that uses its own liquidity pools to front the withdrawal, but audit that bridge's trust model independently: key custody, oracle dependencies, and pool solvency assumptions are all additional attack vectors.
Glossary
| Term | Definition |
|---|---|
| Optimistic Rollup | A Layer-2 scaling solution that assumes transactions are valid unless challenged via fault proofs during a dispute window. |
| Bisection Game | An interactive dispute resolution protocol that narrows a disagreement about state transitions to a single instruction step for on-chain verification. |
| Predeploy Contract | A system-level smart contract deployed at a predetermined address in the genesis state of an L2 chain, governing bridging, fees, and chain configuration. |
| Address Aliasing | A cross-domain safety mechanism that offsets contract sender addresses by a fixed constant to prevent identity spoofing between L1 and L2. |
| EVM | The Ethereum Virtual Machine — the runtime environment that executes smart contract bytecode on Ethereum and EVM-compatible chains. |
| Cross-Chain | Communication or asset transfer between different blockchain networks or layers. |
| Proxy Pattern | A smart contract design where a proxy contract delegates calls to an implementation contract, enabling upgradeability while preserving state and address. |
| Replay Attack | An attack where a valid transaction or message is maliciously resubmitted to execute multiple times or on a different chain. |
Get the DeFi Protocol Security Checklist
15 vulnerabilities every DeFi team should check before mainnet. Used by 30+ protocols.
No spam. Unsubscribe anytime.