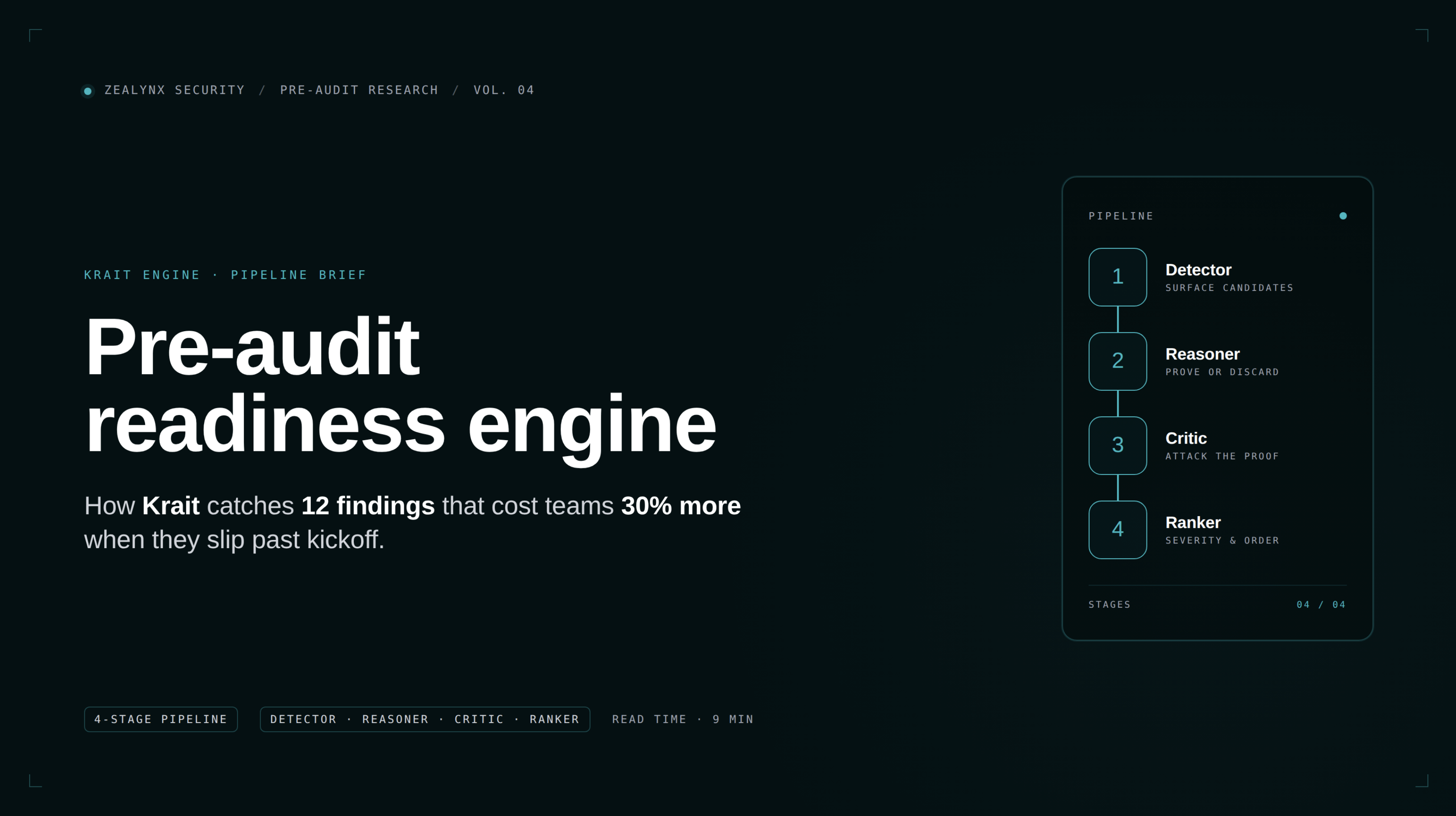
Pre-Audit Readiness Engine
A pipeline that simulates a senior security researcher's first pass on a smart contract repo to catch the mechanical and process findings that would otherwise inflate a paid audit by ~30%.
A pre-audit readiness engine is a tooling layer that runs before a paid manual audit, with one purpose: catch the findings and process gaps that should never reach a senior auditor's billable hour. It is not a static analyzer like Slither, not a single-pass LLM scanner, and not a replacement for a manual review. It sits between those tools and the human audit and is designed to lower the cost of the human audit by raising the quality of the input.
Why It Exists
Auditors charge for the time it takes to understand your code. Conservatively, 30% of an audit bill is a tax on unpreparedness: reverse-engineering intent, deciphering undocumented architecture, triaging untriaged Slither warnings, dealing with broken commits during the engagement. A pre-audit readiness engine targets that 30% directly.
What It Has To Do
- Detect like an auditor, not like a pattern matcher. Reason about whether a flagged pattern is actually exploitable in the code's context, not just whether it matches a regex.
- Eliminate false positives. A noisy report is worse than no report — teams learn to skim past warnings, and the real bug gets missed. Effective readiness engines run an explicit false-positive elimination layer (Krait calls these Kill Gates) that tries to disprove every candidate finding.
- Cover process gaps that code analysis cannot see. Frozen commit.
scope.txt. NatSpec coverage. Invariant list. Branch coverage report. These do not appear in any static analyzer's output but are the single largest cost driver in real audits.
How It Differs From Adjacent Tools
| Tool class | What it does | What it does not do |
|---|---|---|
| Static analyzer (Slither, Aderyn) | Emits warnings against fixed AST patterns | Reason about exploitability, suppress noise, cover docs/process |
| Single-pass LLM scanner | One LLM read over the code, lists possible issues | Disprove its own findings, reproduce on shadow audits |
| Manual audit | Human researcher finds economic and logic bugs | Run on every PR, scale to a 24h iteration loop |
| Pre-audit readiness engine | All of the above as a structured pipeline | Replace the manual audit on economic/business-logic bugs |
Krait As The Reference Implementation
Krait is the Zealynx implementation. It runs a 4-phase pipeline (Detector → Reasoner → Critic → Ranker), is benchmarked publicly against 40 Code4rena / Sherlock / CodeHawks contests via shadow audits, and reached 100% precision at 0.2 FPs per contest in its most recent five-contest cycle. The methodology and pattern library are open-source at github.com/ZealynxSecurity/krait. Full breakdown in the pre-audit readiness engine deep dive.
When To Use One
- Before paying for the first audit on a new protocol.
- Before each follow-up audit on a maintained protocol — the readiness score gives the auditor an updated context map.
- Inside the engineering CI loop on every PR that touches contracts, to catch regressions before they reach the freeze.
- Before a tier-1 exchange listing or institutional integration that requires an audit history.
Related Concepts
- Audit Readiness — the state of the codebase; a pre-audit readiness engine measures and improves it.
- Shadow Audit — the public benchmark format used to validate that a readiness engine catches real bugs.
- Audit Scope — what a readiness engine helps you define and lock before the engagement begins.
Articles Using This Term
Learn more about Pre-Audit Readiness Engine in these articles:
Related Terms
Audit Readiness
The state of a protocol's codebase and documentation being prepared for a formal security audit, including frozen code, test coverage, and documented invariants.
Shadow Audit
A training exercise where you audit a real past security contest on a known-graded protocol fork, inside a time-boxed window, with your findings scored against the actual contest results.
Audit Scope
The defined boundaries of a security audit, specifying which contracts, functions, and concerns will be reviewed.
NatSpec
Natural Language Specification Format - Ethereum's standard for documenting smart contract code with structured inline comments.
Need expert guidance on Pre-Audit Readiness Engine?
Our team at Zealynx has deep expertise in blockchain security and DeFi protocols. Whether you need an audit or consultation, we're here to help.
Get a Quote