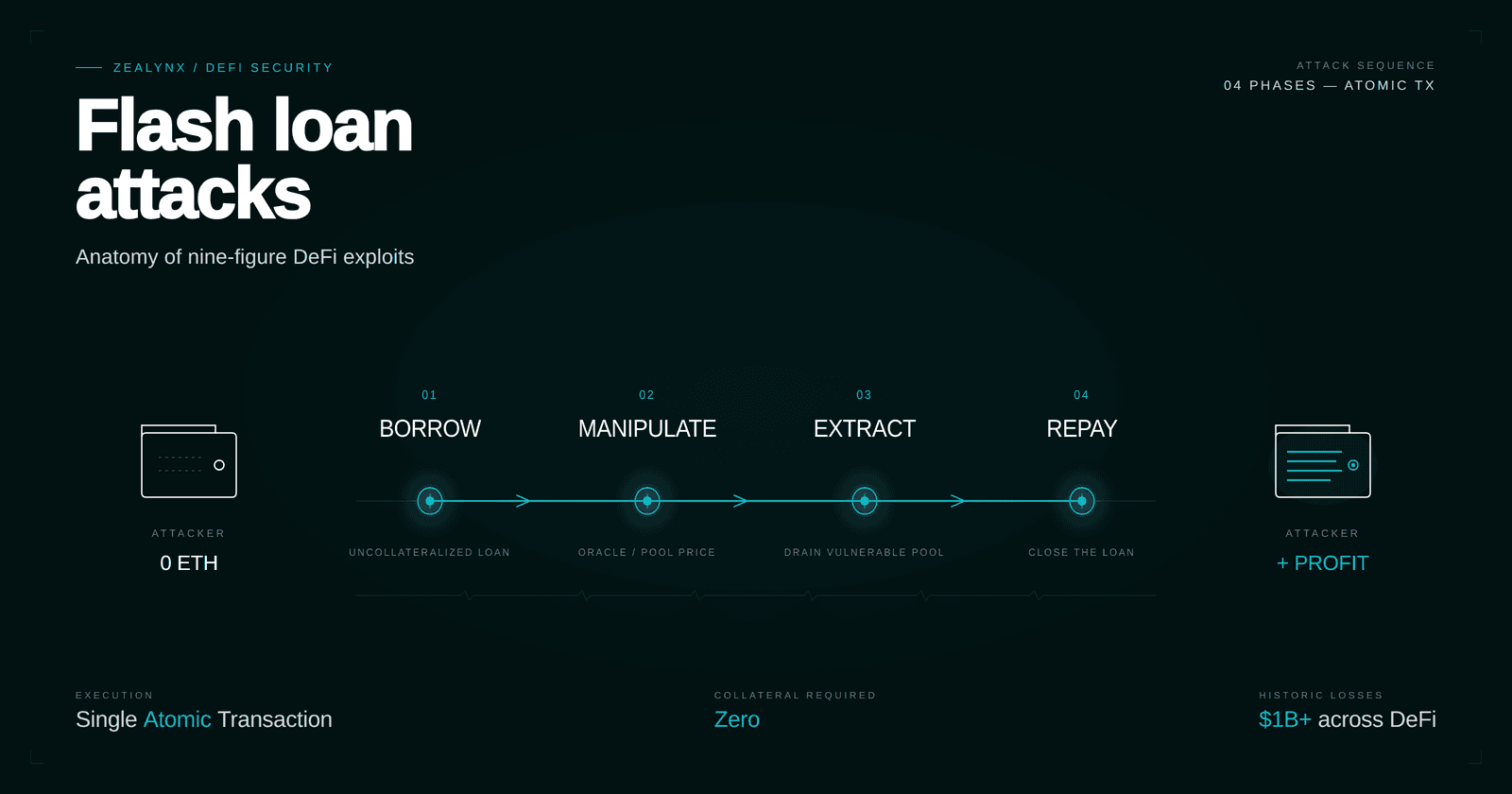
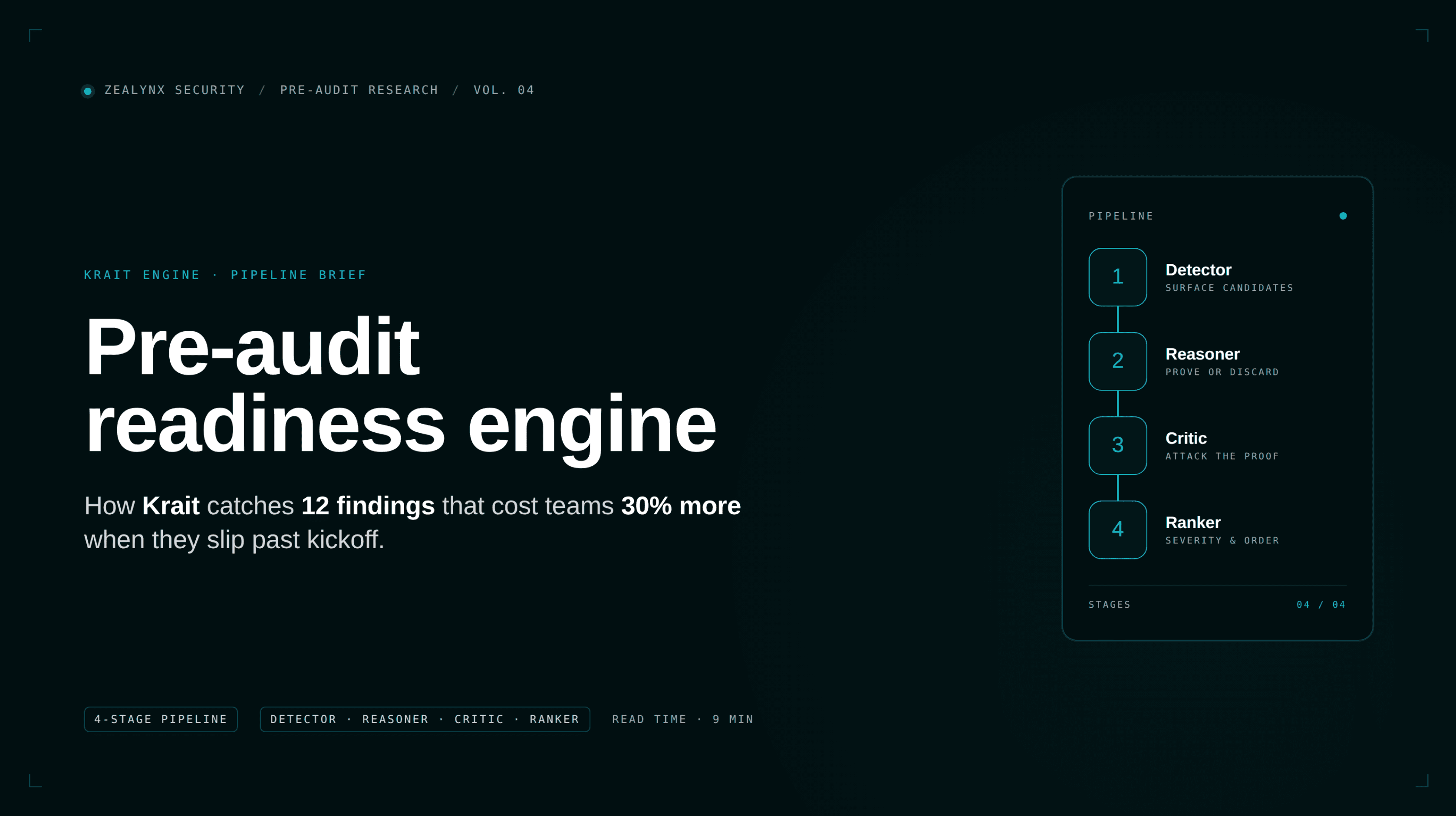
Who is Zealynx? Why DeFi teams choose our top-tier smart contract audits
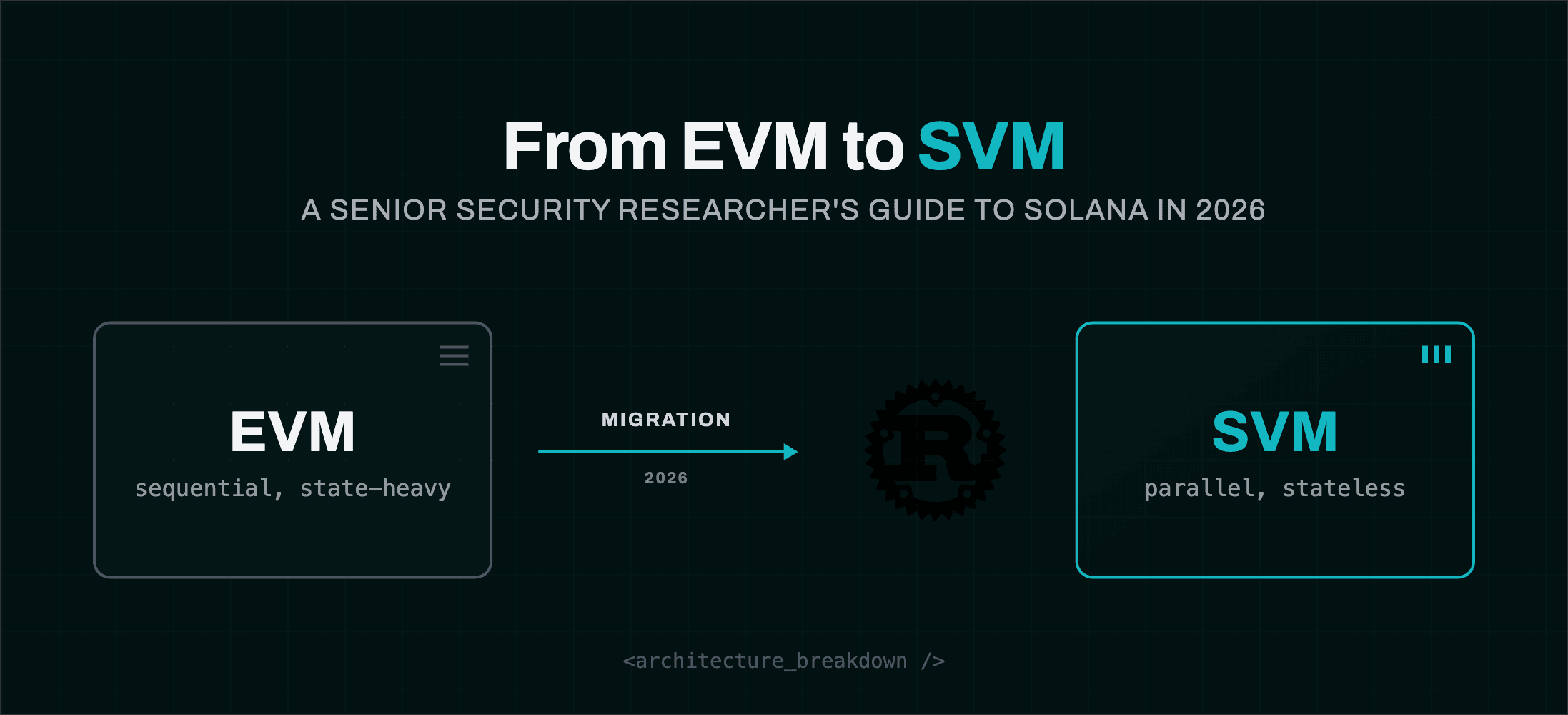
Zealynx is a founder-led Web3 security firm. 33+ audits across 30+ protocols on EVM and Solana, smart contract audits, penetration testing, AI security, and the Zealynx Audit Grants program.