Back to Blog 
DeFiWeb3 SecurityAuditAMM
Oracle manipulation in DeFi: how price feeds become attack vectors
11 min
In this article: How flash loan-powered oracle manipulation works at the EVM level, the constant product formula exploit sequence, and three defense layers (TWAPs, Chainlink circuit breakers, liquidity depth checks) to protect your protocol from price feed attacks.
Blockchains operate as closed, deterministic state machines. By design, an Ethereum smart contract lacks the native capability to execute HTTP requests to query real-world data, such as the price of a financial asset.
To solve this isolation, DeFi protocols rely on oracles: bridges that inject off-chain data into the blockchain. This data feeds the business logic for loan issuance, liquidations, and derivative pricing.
This external dependency creates a critical attack vector in the ecosystem. If an agent artificially alters the price feed read by the smart contract, the protocol will execute mathematically correct instructions based on a false premise. The immediate result is protocol insolvency through deterministic arbitrage — without the need to exploit traditional software bugs.
How oracle manipulation exploits work
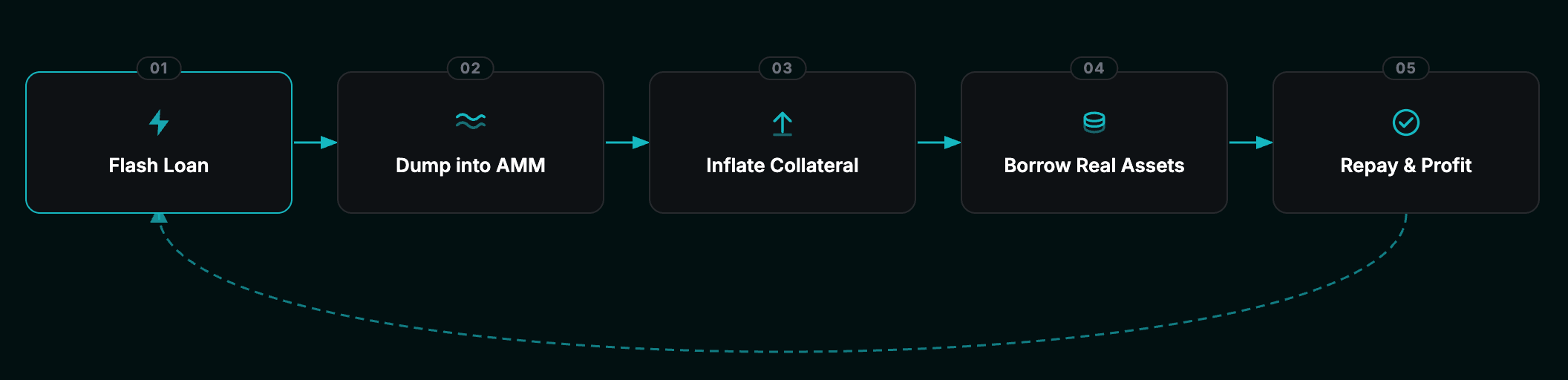
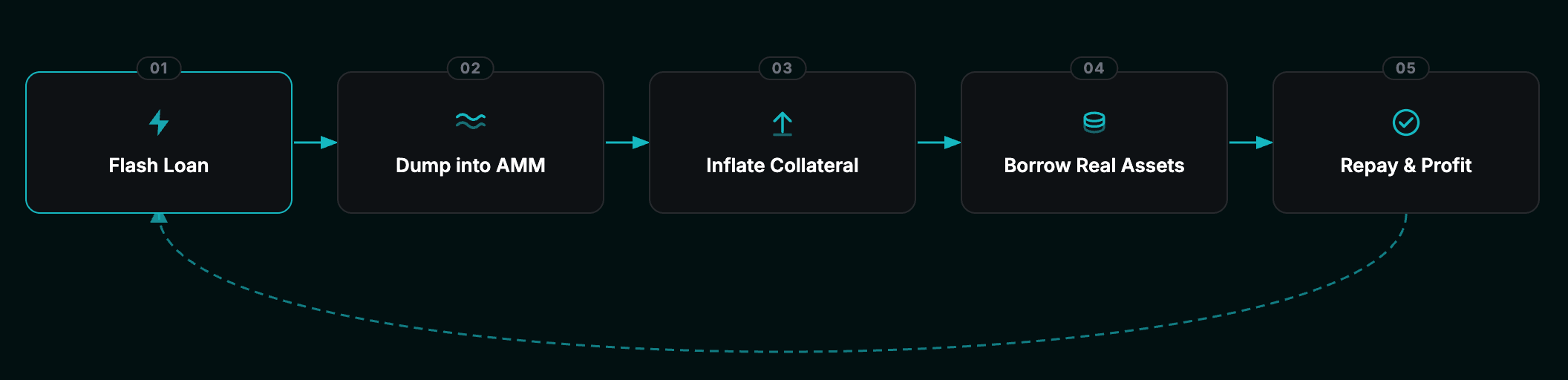
The majority of oracle manipulation attacks exploit the atomic interaction between uncollateralized loans (flash loans) and the mathematical formulas of automated market makers (AMMs).
Flash loans allow a contract to borrow unlimited liquidity, provided the principal plus fees is returned within the same Ethereum Virtual Machine (EVM) transaction. If the repayment fails, the transaction reverts, mitigating counterparty risk. This democratizes market manipulation by removing the requirement for upfront capital.
AMMs determine the spot price of an asset using the constant product formula . The price of asset is a function of the reserve ratio (). The exploit occurs through a straightforward transactional sequence:
- Acquire — The attacker obtains a massive volume of liquidity via a flash loan.
- Imbalance — The capital is dumped into a low-liquidity AMM pool, inflating variable and depleting . The spot price of the target asset suffers an instant artificial distortion.
- Exploit — The attacker deposits the artificially inflated asset as collateral in a lending protocol (the victim) that relies on this specific AMM as its price oracle.
- Extract — The protocol values the deposit at the inflated price, allowing the attacker to borrow real, liquid assets far exceeding the actual value of their collateral.
- Close — The attacker uses a fraction of the extracted funds to repay the flash loan and closes the atomic transaction, leaving the victim protocol with bad debt.
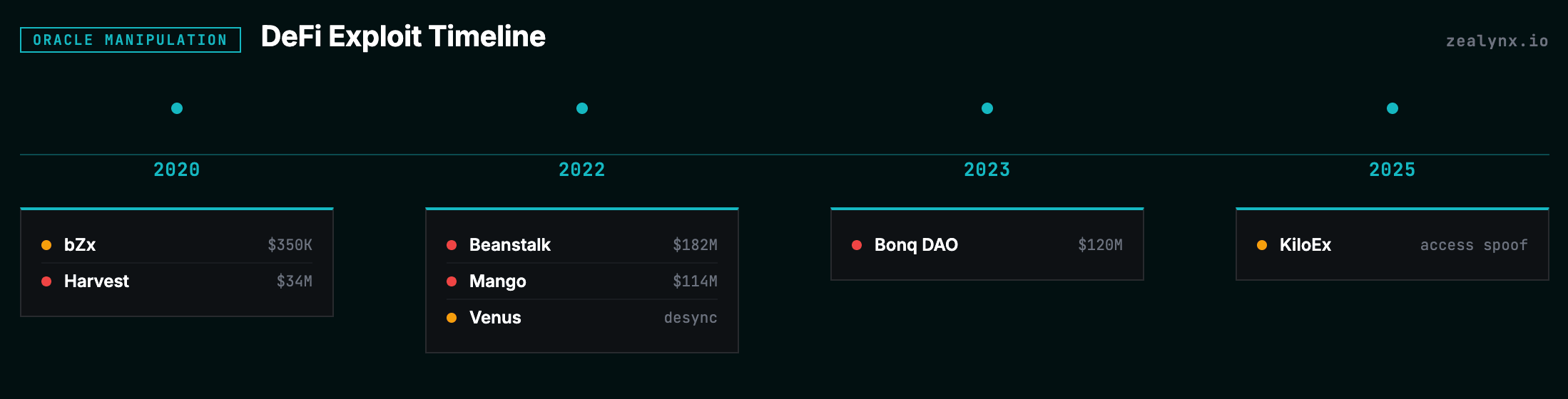
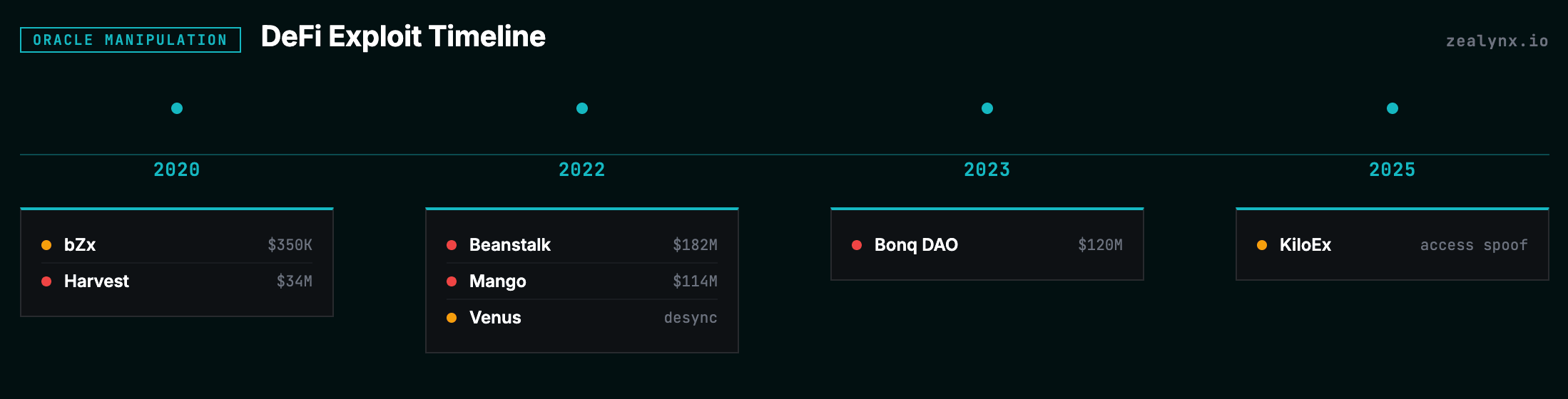
Historical architectural failures
The history of DeFi exploits reveals consistent patterns of architectural flaws. The table below condenses the most instructive cases:
| Protocol | Year | Primary attack vector | Core architectural failure |
|---|---|---|---|
| bZx | 2020 | Spot price (flash loan) | Strict reliance on a single DEX oracle (Kyber/Uniswap) to calculate the spot price. |
| Harvest | 2020 | Virtual price (flash loan) | Trust in the algorithmic calculation of stablecoin proportions within Curve Finance pools to price shares. |
| Beanstalk | 2022 | Governance subversion | Capital injection via flash loan into an AMM pool resulted in atomic acquisition of 78% of voting power, bypassing time-locks. |
| Mango | 2022 | Cross-margin (real capital) | Use of a low-liquidity asset (MNGO) as collateral to borrow liquid assets. The price was inflated using organic capital, without a flash loan. |
| Venus | 2022 | Infrastructure desync | The Chainlink oracle triggered a 0.01, but the protocol kept lending based on the hardcoded price. |
| Bonq DAO | 2023 | Parameter injection | The smart contract lacked maximum limit validation on the updatePrice function, allowing arbitrary injection of valuation data. |
| KiloEx | 2025 | Access spoofing | A flaw in the Minimal Forwarder contract allowed bypassing validations and sending forged signatures to the setPrices function. |
Each of these incidents demonstrates a common theme: the protocol trusted a single source of price truth without validation or fallback. Understanding these patterns is essential for anyone building or auditing smart contracts.
Secure oracle models
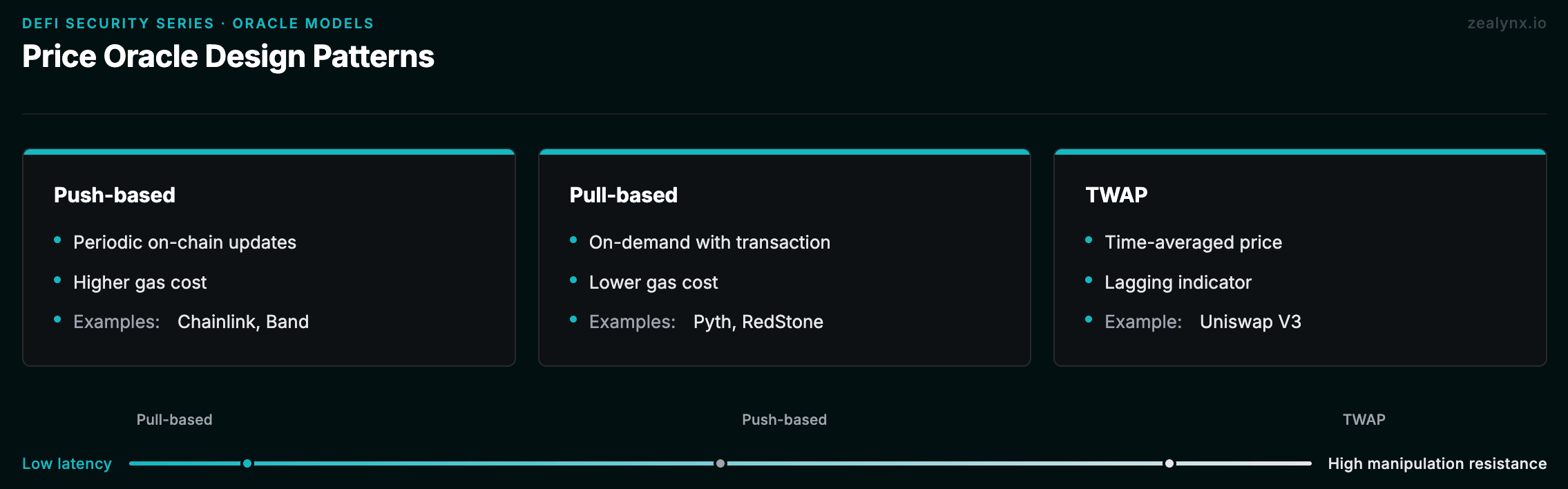
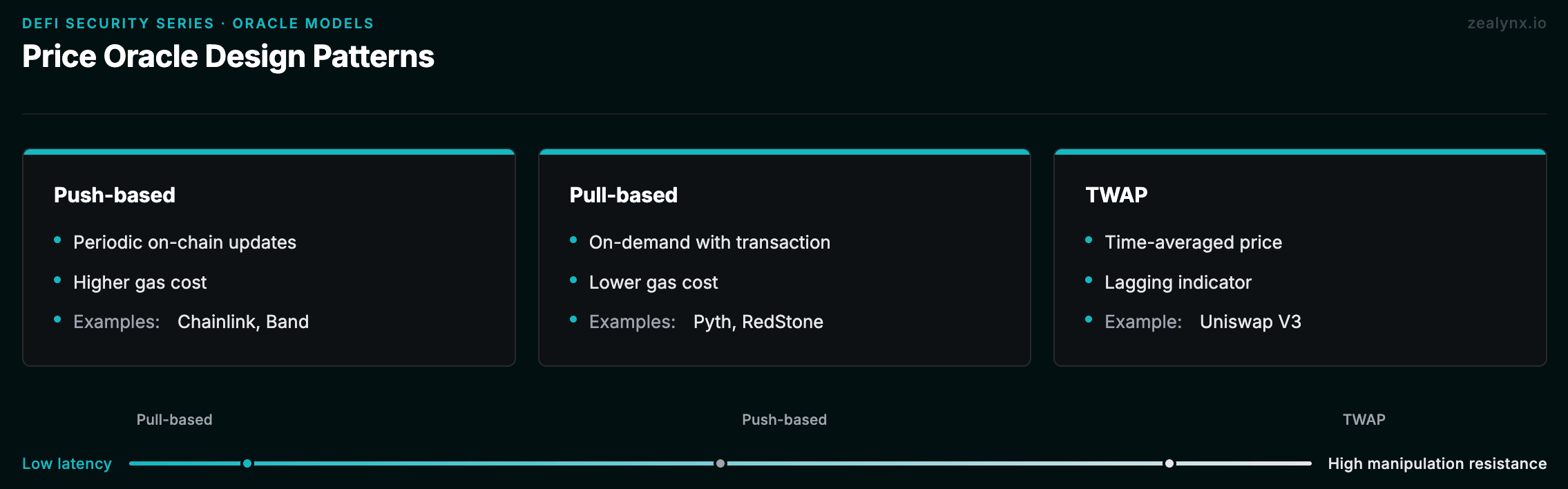
To mitigate oracle manipulation risk, architects must choose the appropriate data delivery model for their protocol's latency requirements.
Push-based oracles (e.g., Chainlink)
In this model, autonomous nodes publish price data on-chain periodically or when the deviation threshold exceeds a pre-configured percentage. It is stable for low-frequency lending protocols but incurs high maintenance gas costs and may lag during extreme network volatility.
1// Push-based: Chainlink price feed2(, int256 price, , uint256 updatedAt, ) = priceFeed.latestRoundData();3require(block.timestamp - updatedAt < MAX_STALENESS, "Stale price");
Pull-based oracles (e.g., Pyth, RedStone)
Focused on high-frequency protocols (like perpetual derivative exchanges), providers sign off-chain price updates. The smart contract "pulls" this validated update only when the user submits a transaction. This eliminates gas consumption during downtime and reduces latency to the block level.
1// Pull-based: price submitted with user transaction2function executeSwap(bytes calldata priceUpdate) external {3 pyth.updatePriceFeeds(priceUpdate);4 int64 price = pyth.getPrice(feedId).price;5 // Execute swap with validated price6}
Time-weighted average prices (TWAP)
The TWAP model (e.g., Uniswap V3) archives past interactions to create a mathematical average over a fixed time window (e.g., 30 minutes). This negates the viability of atomic flash loans but turns the oracle into a lagging indicator. During real market crashes, the protocol may fail to liquidate collateral in time.
To understand how TWAP oracles evolved across Uniswap versions, see our deep dive on Uniswap V3 architecture and the mathematics behind moving averages in DeFi.
Oracle extractable value (OEV)
The temporal discrepancy in oracle updates creates arbitrage windows extracted by MEV bots (mempool sniping). New architectures internalize this flow by routing updates through dedicated Order Flow Auctions (OFAs). The bid paid by the winning bot is redirected to the protocol's treasury, retaining value instead of leaking capital.
Auditing price integration
Your practical next step is to audit your protocol's price ingestion routine under the principle of defense in depth.
Do not rely on the spot price of a single AMM pair. Implement a hybrid architecture: couple a primary decentralized pull or push oracle with a secondary on-chain TWAP oracle as a fallback.
Add an algorithmic circuit breaker logic that, upon detecting an atypical variance (>10%) between the two sources or the activation of extreme hardcoded limits, immediately pauses new issuances and borrows — without freezing collateral protection deposits — until valuations stabilize.
1function getValidatedPrice() internal view returns (uint256) {2 uint256 primaryPrice = getPrimaryOraclePrice();3 uint256 twapPrice = getTWAPPrice();45 uint256 deviation = calculateDeviation(primaryPrice, twapPrice);67 // Circuit breaker: pause on >10% deviation8 require(deviation < 1000, "Price deviation circuit breaker");910 return primaryPrice;11}
Get the DeFi Protocol Security Checklist
15 vulnerabilities every DeFi team should check before mainnet. Used by 30+ protocols.
No spam. Unsubscribe anytime.
Furthermore, formally verify the economic logic using static analysis tools and SMT solvers (like the OVer framework or Slither) prior to mainnet deployment. For a structured approach to pre-deployment verification, review our pre-audit checklist.
Oracle integration checklist
- Use multiple independent price sources (push + TWAP fallback)
- Validate staleness on every oracle read
- Implement circuit breakers for abnormal deviations
- Set sanity bounds (min/max) on accepted prices
- Test with flash loan attack simulations in your fuzzing suite
- Verify decimal handling across different token standards
- Add time-locks for governance-controlled oracle updates
- Monitor on-chain for large single-block price swings
If you are evaluating whether your protocol's oracle architecture meets production-grade standards, our audit readiness assessment walks you through a structured review across 39 DeFi verticals.
Get in touch
Oracle security is one of the highest-stakes areas in DeFi protocol design. A single misconfigured price feed can drain an entire treasury in one transaction.
At Zealynx, we specialize in smart contract security audits with deep expertise in oracle integration, AMM mechanics, and defense-in-depth workflows. Whether you are launching a new lending protocol or upgrading your oracle infrastructure, we help you identify the architectural flaws before attackers do.
FAQ: Oracle manipulation and DeFi security
1. What is an oracle in blockchain, and why do smart contracts need one?
An oracle is a service that feeds external data — such as asset prices, interest rates, or event outcomes — into a blockchain. Smart contracts are deterministic and isolated: they cannot make HTTP requests or access APIs. Without oracles, a lending protocol would have no way to know the current price of ETH to calculate whether a borrower's collateral is sufficient. Oracles bridge this gap, but the dependency creates an attack surface that must be secured at the architectural level.
2. How do flash loans enable oracle manipulation attacks?
Flash loans allow anyone to borrow unlimited capital with zero collateral, as long as the loan is repaid within a single transaction. An attacker uses this borrowed capital to execute a massive trade on a low-liquidity AMM pool, artificially skewing the price reported by the pool's reserves. They then exploit a victim protocol that reads this manipulated price — for example, depositing the inflated asset as collateral to borrow real assets. If any step fails, the entire transaction reverts and the attacker loses nothing but gas fees, making these attacks risk-free to attempt.
3. What is the difference between push-based and pull-based oracles?
Push-based oracles (like Chainlink) have off-chain nodes that proactively publish price updates on-chain at regular intervals or when prices deviate past a threshold. The protocol reads the latest on-chain value. Pull-based oracles (like Pyth or RedStone) keep signed price data off-chain until a user submits a transaction — the price update is included with the transaction and verified on-chain at execution time. Pull-based models are cheaper (no gas spent during idle periods) and lower latency, making them suited for high-frequency trading protocols like perpetual exchanges.
4. Can TWAP oracles be manipulated, and what are their limitations?
TWAP (time-weighted average price) oracles are resistant to single-transaction manipulation because they average prices over a time window (e.g., 30 minutes across multiple blocks). However, they can be manipulated by a well-funded attacker who sustains artificial prices across many blocks — this is expensive but not impossible. Their main limitation is latency: during a real market crash, the TWAP lags behind the true price, potentially delaying critical liquidations and exposing the protocol to bad debt.
5. What is a circuit breaker in the context of oracle security?
A circuit breaker is a defensive mechanism that automatically pauses protocol operations when it detects abnormal price behavior — such as a price deviation exceeding 10% between two oracle sources, or a price change that exceeds historical norms within a single block. It acts as a safety net: instead of executing transactions based on potentially manipulated data, the protocol halts new borrows and issuances until the price stabilizes. Critically, well-designed circuit breakers should not freeze existing collateral deposits, so users can still protect their positions.
6. How should a protocol audit its oracle integration before mainnet deployment?
Start with a hybrid oracle architecture: combine a primary decentralized oracle (Chainlink or Pyth) with a secondary on-chain TWAP as a fallback. Validate staleness on every read, implement circuit breakers for abnormal deviations, and set sanity bounds on accepted prices. Run flash loan attack simulations in your fuzz testing suite. Verify decimal handling across all supported tokens. Use static analysis tools like Slither and SMT solvers for formal verification of economic logic. Finally, have an independent security team review the integration — oracle flaws are among the most expensive bugs in DeFi.
Glossary
| Term | Definition |
|---|---|
| Oracle | A service that provides external data (prices, events, random numbers) to smart contracts that cannot access off-chain information directly. |
| Flash loan | Uncollateralized loan borrowed and repaid within a single transaction, often used for arbitrage or attacks. |
| Automated market maker | A protocol that uses mathematical formulas to price assets in liquidity pools instead of order books. |
| TWAP | Time-weighted average price — an oracle model that averages prices over a time window to resist single-transaction manipulation. |
| MEV | Maximal extractable value — profit extracted by reordering, inserting, or censoring transactions within a block. |
| Circuit breaker | A defensive mechanism that pauses operations when anomalous price behavior is detected. |
| Constant product formula | The AMM pricing model used by Uniswap and similar DEXs. |
| Price oracle manipulation | An attack where an attacker artificially skews the price reported by a price oracle to exploit dependent protocols. |
| Defense in depth | A security strategy using multiple layered defenses so that if one fails, others still protect the system. |
Is Your Oracle Integration Exploit-Proof?
Spot price reliance, missing staleness checks, and no circuit breakers are the three patterns that cost DeFi protocols the most. Our oracle security reviews cover Chainlink, Pyth, and Uniswap TWAP integrations — plus flash loan attack simulation against your specific price-dependent logic.
Get the DeFi Protocol Security Checklist
15 vulnerabilities every DeFi team should check before mainnet. Used by 30+ protocols.
No spam. Unsubscribe anytime.