Sybil Attack
An attack where a single entity creates many pseudonymous identities (wallets, accounts, nodes) to gain disproportionate influence in a system that assumes one-entity-one-identity. Common in airdrops, DAO governance, quadratic voting, and public-goods funding.
A Sybil attack is a security threat where a single adversary creates numerous pseudonymous identities (wallets, accounts, nodes) to subvert systems that weight influence per-identity rather than per-capital. Named after the subject of the 1973 book about dissociative identity disorder, Sybil attacks exploit the fundamental pseudonymity of permissionless blockchain networks where anyone can generate unlimited addresses at near-zero cost.
In computing and crypto, the attack pattern is straightforward: if a system rewards unique participants, an attacker can manufacture fake participants to siphon rewards.
Where Sybil Attacks Appear in Web3
Airdrops and token distributions. Projects distributing tokens "to the community" often find most supply goes to sybil farmers who created dozens of wallets to qualify as separate users. The LayerZero, Arbitrum, and Optimism airdrops all saw significant sybil activity that the teams partially filtered before distribution. Sybil farming dilutes legitimate recipients and concentrates tokens with attackers.
DAO governance. Protocols that weight voting power by wallet count (one wallet, one vote) are vulnerable to attackers creating many low-balance wallets to swing proposals. Combined with vote buying or delegation, Sybil addresses can artificially inflate participation metrics, manipulate quorum calculations, or distribute governance power to evade per-address caps.
Quadratic voting. The quadratic cost function (Cost = Votes²) is designed to reduce whale influence — 100 votes cost 10,000 tokens from a single address. But an attacker splitting tokens across 100 addresses pays only 100 tokens total for 100 votes, completely bypassing the quadratic penalty.
Quadratic funding. QF rewards the number of unique donors. Without defense, an attacker could create 100 wallets, donate $1 from each, and siphon a large share of the matching pool.
Automated farming. Scripts can generate thousands of wallets, distribute funds to each, perform minimum-required activity, and claim any reward distributions — a scaled-up form of the classic attack.
How Systems Defend Against Sybils
Different systems use different combinations:
- Proof of Personhood (PoP) systems like Gitcoin Passport, Worldcoin, Holonym, and BrightID attempt to verify unique human identity through biometric, social graph, or credential-based attestation. These create identity verification layers that make Sybil creation expensive or impossible.
- On-chain history. Require a wallet to have been active for a minimum time or to have completed specific actions that cost real value (gas on mainnet, NFT holdings, staking).
- Graph analysis. Techniques using Graph Convolutional Neural Networks (GCNN) and clustering algorithms detect coordinated wallet behavior — similar transaction timing, shared funding sources, identical interaction patterns — to identify and neutralize Sybil clusters.
- Social graph analysis. Trust paths through existing verified identities — sybils often show up as isolated nodes with no legitimate social connections.
- Economic deterrence. Minimum balances, staking requirements, bond deposits, or activity thresholds that make creating hundreds of fake identities prohibitively expensive.
Sybil-Resistance Is Not Sybil-Proof
No system is fully sybil-proof. The goal is to make sybil attacks economically irrational — the cost of faking identities exceeds the value extracted. A well-designed QF round with Passport verification plus statistical analysis can be very hard to game at small scale, though sophisticated attackers with capital can still extract some value.
Why It Matters
Sybil resistance is the foundation of any mechanism that treats individuals as meaningful voting or funding units. In the context of public goods funding, failing to defend against sybils means the matching pool gets drained by farmers instead of directed to the projects genuinely valued by the community. In DAO governance, Sybil attacks can hijack proposal outcomes and misallocate treasury funds. The entire incentive structure collapses either way. This is why QF rounds like the TheDAO Fund's Ethereum Security round build Passport requirements into the donation flow from day one, and why mature DAOs layer proof-of-personhood onto voting systems.
Articles Using This Term
Learn more about Sybil Attack in these articles:

Quadratic Funding Explained: Ethereum Security QF Round and Zealynx Academy
Quadratic funding rewards supporter count over donation size. TheDAO Fund's 500 ETH Ethereum Security QF round explained, and why Zealynx Academy joined.
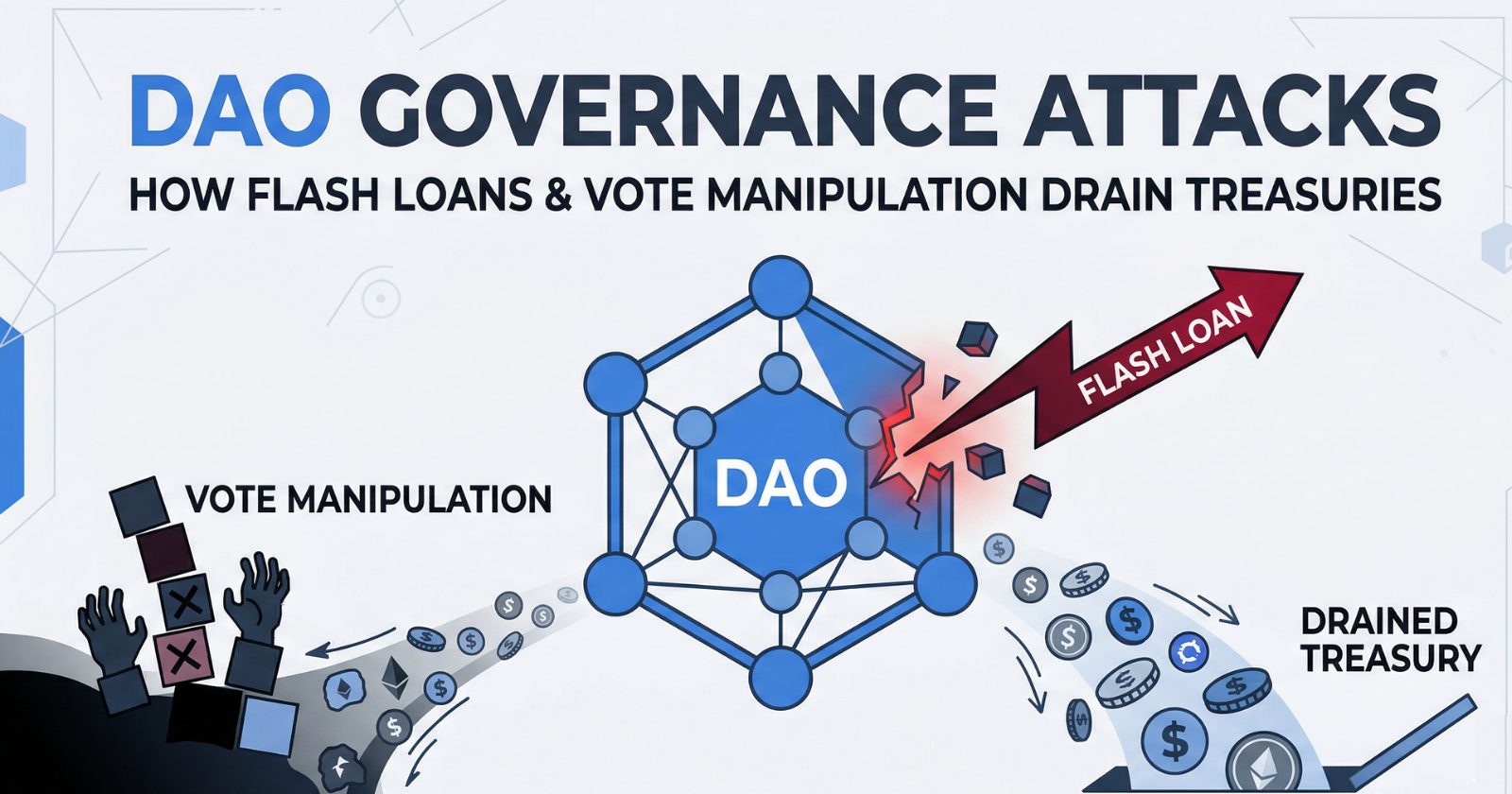
DAO governance attacks: how flash loans and vote manipulation drain treasuries
How attackers exploit DAO governance with flash loans, EVM opcode injection, and quorum exhaustion — plus audit strategies and defense architectures.
Related Terms
Gitcoin Passport
A decentralized identity and proof-of-humanity system used to verify that a wallet is operated by a real person. Donations in quadratic funding rounds only count toward matching if the donor holds a Passport score above a threshold (commonly 50+).
Quadratic Funding
A funding mechanism that amplifies donations based on the number of unique supporters rather than total amount raised. Used by Gitcoin, Giveth, and Optimism for public goods funding.
Quadratic Voting
A voting mechanism where the cost of additional votes scales geometrically, reducing plutocratic dominance but vulnerable to Sybil attacks.
DAO (Decentralized Autonomous Organization)
A blockchain-based organization governed by smart contracts and token-weighted voting rather than centralized management.
Governance Attack
An exploit that weaponizes a protocol's legitimate voting mechanics to pass malicious proposals or drain treasury funds.
Public Goods
Goods or services whose benefits are shared broadly but are hard to fund through normal markets because no single actor can capture the value. Open-source infrastructure, security research, and education are common Web3 examples.
Need expert guidance on Sybil Attack?
Our team at Zealynx has deep expertise in blockchain security and DeFi protocols. Whether you need an audit or consultation, we're here to help.
Get a Quote