Back to Blog 
AuditWeb3 Security
Move vs. Rust vs. Solidity: The Ultimate L1 Blockchain Security Comparison (2026)
12 min
The architectural landscape of Layer 1 (L1) blockchains has undergone a radical transformation over the past decade, driven largely by the harsh lessons learned from adversarial exploits. In the nascent stages of smart contract development, the primary objective was expressivity, providing developers with a Turing-complete canvas to build decentralized applications (dApps). Ethereum and its native language, Solidity, pioneered this era, establishing a dominant paradigm based on a mutable global state and synchronous composability.
However, this flexibility came at a staggering cost. The "Code is Law" ethos was severely tested by the 2016 DAO hack, and subsequent years saw billions of dollars lost to reentrancy attacks, integer overflows, and uninitialized proxies. These incidents highlighted a fundamental dissonance in early blockchain architecture: the languages used to manage immutable financial value were inherited from web development paradigms that prioritized flexibility over rigorous safety.
As the industry matured, a second generation of architectures emerged, prioritizing performance and throughput. Solana, utilizing the Rust programming language, introduced a stateless execution model designed to maximize hardware utilization through parallelization. This shifted the bottleneck from the network to the developer's ability to manage complex concurrency and account validation logic. While Rust provided memory safety, it did not inherently solve the logical pitfalls of blockchain state management, leading to a new class of vulnerabilities such as account confusion and missing signer checks.
Most recently, the Move programming language, born from Meta’s Diem project, has introduced a third paradigm: resource-oriented architectures. Adopted by Aptos and Sui, Move was designed from first principles to enforce digital scarcity and access control at the type-system level. By treating assets as "resources" that adhere to linear logic, meaning they can never be implicitly copied or discarded, Move attempts to eliminate entire classes of vulnerabilities that plague Solidity and Rust.
For L1 architects, the choice between Solidity (EVM), Rust (SVM), and Move (MoveVM) is no longer merely a preference for syntax; it is a fundamental decision about the security topology, state model, and risk profile of the network. This report provides an exhaustive, security-first comparison of these three paradigms.
Security Paradigms and Design Philosophies
The security posture of a blockchain is downstream of its programming language's design philosophy. While Solidity, Rust, and Move are all Turing-complete, they optimize for radically different constraints.
Solidity: The Contract-Centric Singleton Model
Solidity targets the Ethereum Virtual Machine (EVM), a quasi-Turing-complete stack machine operating as a singleton computer. Its primary abstraction is the Smart Contract, which encapsulates both logic and state within a single addressable entity.
The EVM utilizes a mutable Merkle Patricia Trie for global state. This model enables synchronous, atomic composability, the engine of the DeFi ecosystem, allowing complex interactions like flash loans in a single block. However, Solidity operates on an "implicit unsafe" default. Functions are historically public, state variables are mutable, and external calls can hijack control flow via fallback functions. Assets in Solidity are represented as data (integers in a mapping) rather than physical-like resources, creating a "ledger-based" model where conservation of mass is a logic requirement rather than a system guarantee.
Rust (Solana): The Stateless Account Model
Rust is a systems language adapted for the Solana Virtual Machine (SVM). Solana programs are stateless; they contain only logic. State is stored in separate Accounts, data buffers passed to the program during execution.
This decoupling allows for massive parallelization by identifying non-overlapping transactions. Rust’s borrow checker guarantees memory safety at compile time, preventing null pointer dereferencing and buffer overflows. However, this does not translate to logic safety. The burden of verifying the provenance and authority of input accounts falls entirely on the developer, shifting risk toward "account confusion" and "missing signer checks."
Move: The Resource-Centric Model
Move introduces Resource-Oriented Programming, implementing linear logic within the type system. A struct defined as a resource behaves like a physical object: it must be used exactly once and cannot be implicitly copied or dropped.
Security is enforced at both the source level and the bytecode level. The Move Bytecode Verifier runs on-chain before execution, ensuring that even malicious bytecode cannot violate type safety or resource linearity. Historically, Move also restricted dynamic dispatch to prevent reentrancy, ensuring the call graph is determined at compile time.
Comparative Security Philosophies
| Feature | Solidity (EVM) | Rust (Solana/SVM) | Move (Aptos/Sui) |
|---|---|---|---|
| Primary Abstraction | Smart Contract (Code + State) | Program (Logic) + Accounts (State) | Modules (Logic) + Resources (State) |
| Asset Representation | Integers in a Mapping (Data) | Data in an Account (Buffer) | Linear Types (Resources) |
| Safety Enforcement | Runtime checks (Gas, Reverts) | Compile-time (Borrow Checker) | Compile-time + Bytecode Verification |
| Default Access | Public / Open | Check signatures manually | Restricted by module visibility |
| State Model | Global Mutable Trie | External Account Buffers | Global Storage / Object Store |
| Reentrancy Risk | High | Low (CPI depth limits) | Extremely Low (Resource Locking) |
Resource Models and Asset Safety
The representation of assets determines the classes of bugs theoretically possible on the network.
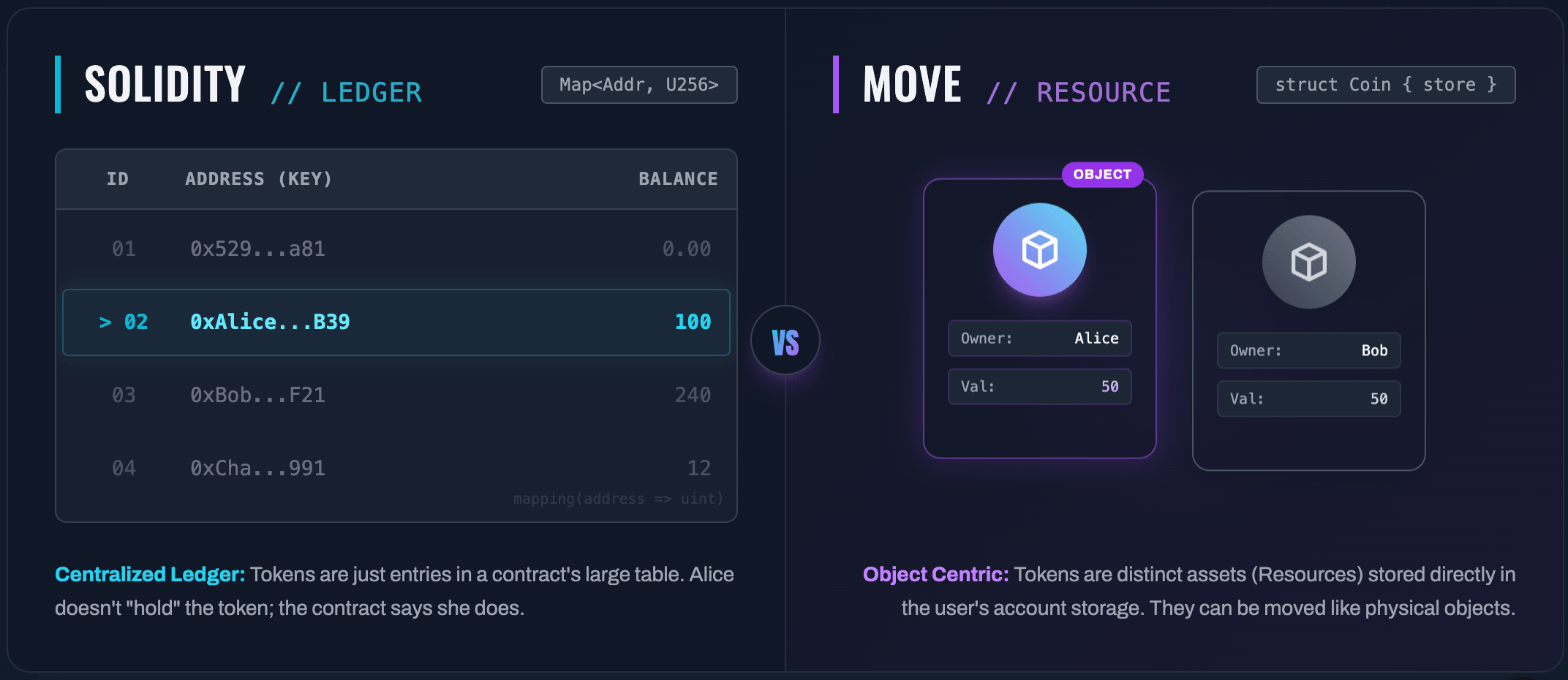
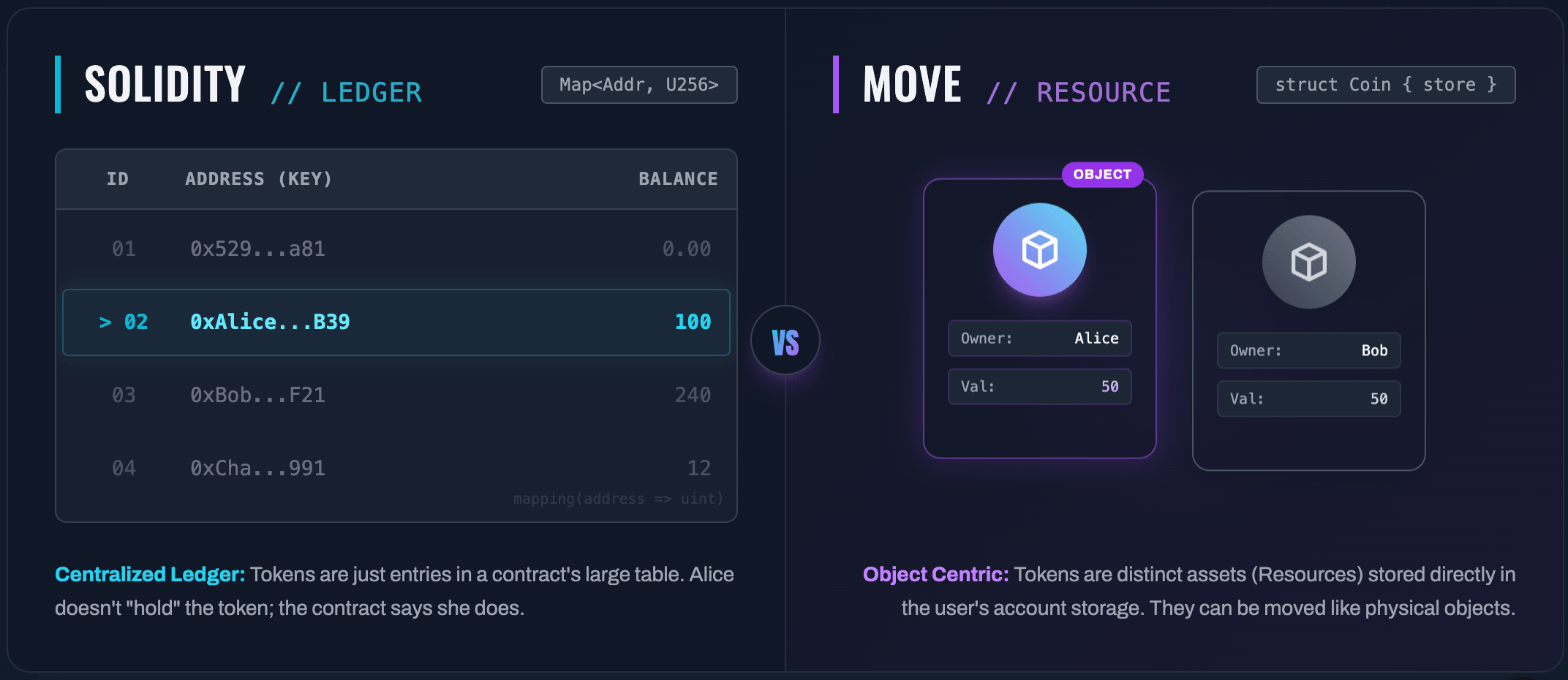
The Solidity "Assets as Integers" Problem
In the EVM, an asset is a logical entry in a hash table:
1mapping(address => uint256) balances;
The VM has no inherent understanding that these integers represent value. This leads to:
- Integer Overflows: Prior to 0.8.0, 0 - 1 could result in
MAX_UINT. - The "Phantom" Asset Problem: Assets sent to contracts without handling logic are permanently locked; the VM cannot enforce that assets must reside in valid locations.
The Move "Assets as Resources" Solution
Move treats assets as first-class resources. For a token, developers omit the
copy and drop abilities:1struct Coin<phantom CoinType> has store {2 value: u643}
Because it lacks
copy, let c2 = c1; is a move operation; c1 becomes invalid. Because it lacks drop, a Coin cannot go out of scope without being explicitly handled (deposited or burned).The "Hot Potato" Pattern: Developers can create structs with no abilities. These must be consumed by a specific function before a transaction ends, enforcing atomicity for complex operations like flash loans at the type system level.
Rust (Solana): The Validation-Heavy Account Model
In Solana, assets are data in accounts owned by the Token Program. The developer must manually verify:
- Source account ownership.
- Signer authority.
- The legitimacy of the Token Program ID.
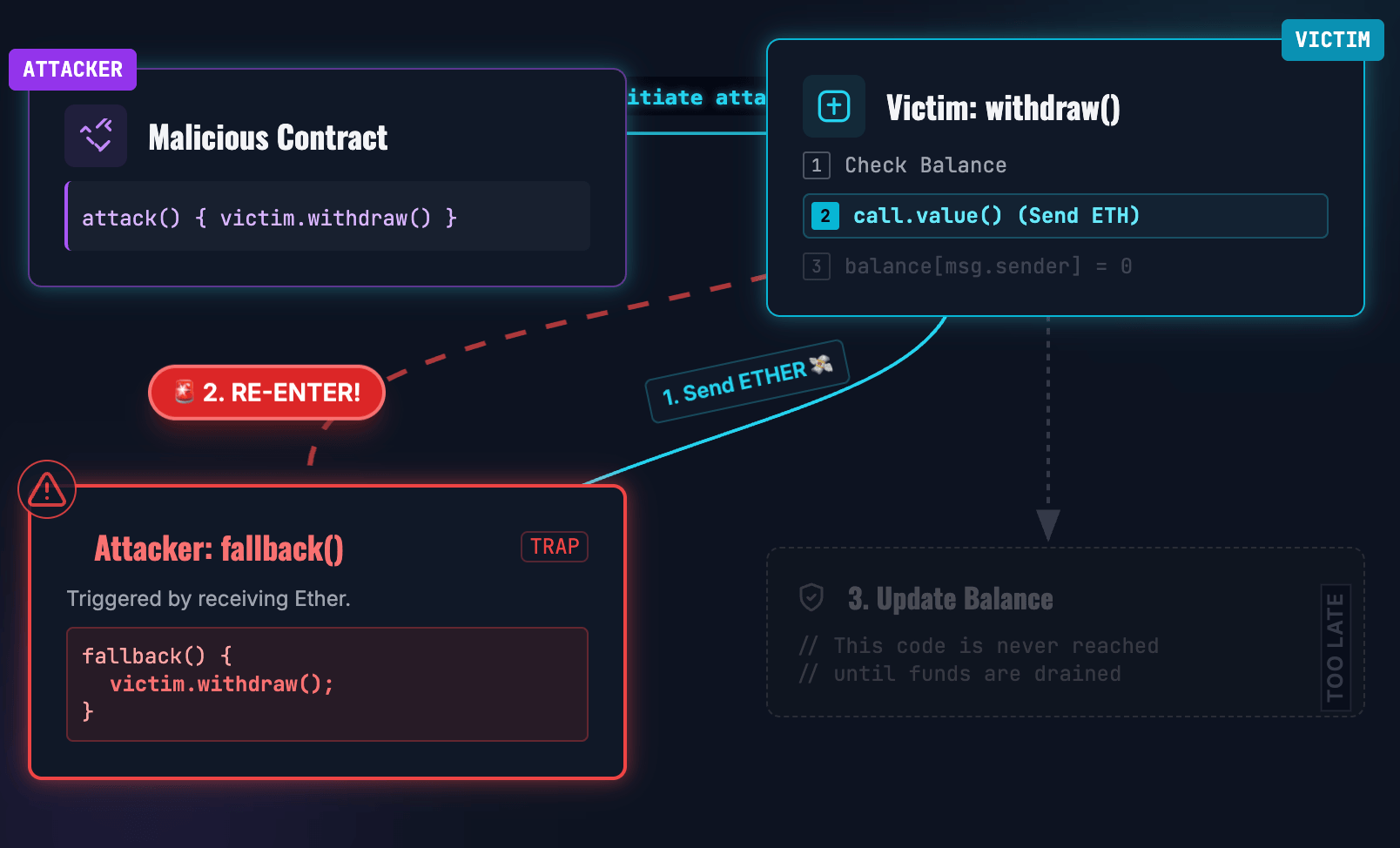
Reentrancy: The Billion-Dollar Bug
Reentrancy occurs when external code hijacks the control flow to execute a function repeatedly before the first execution finishes.
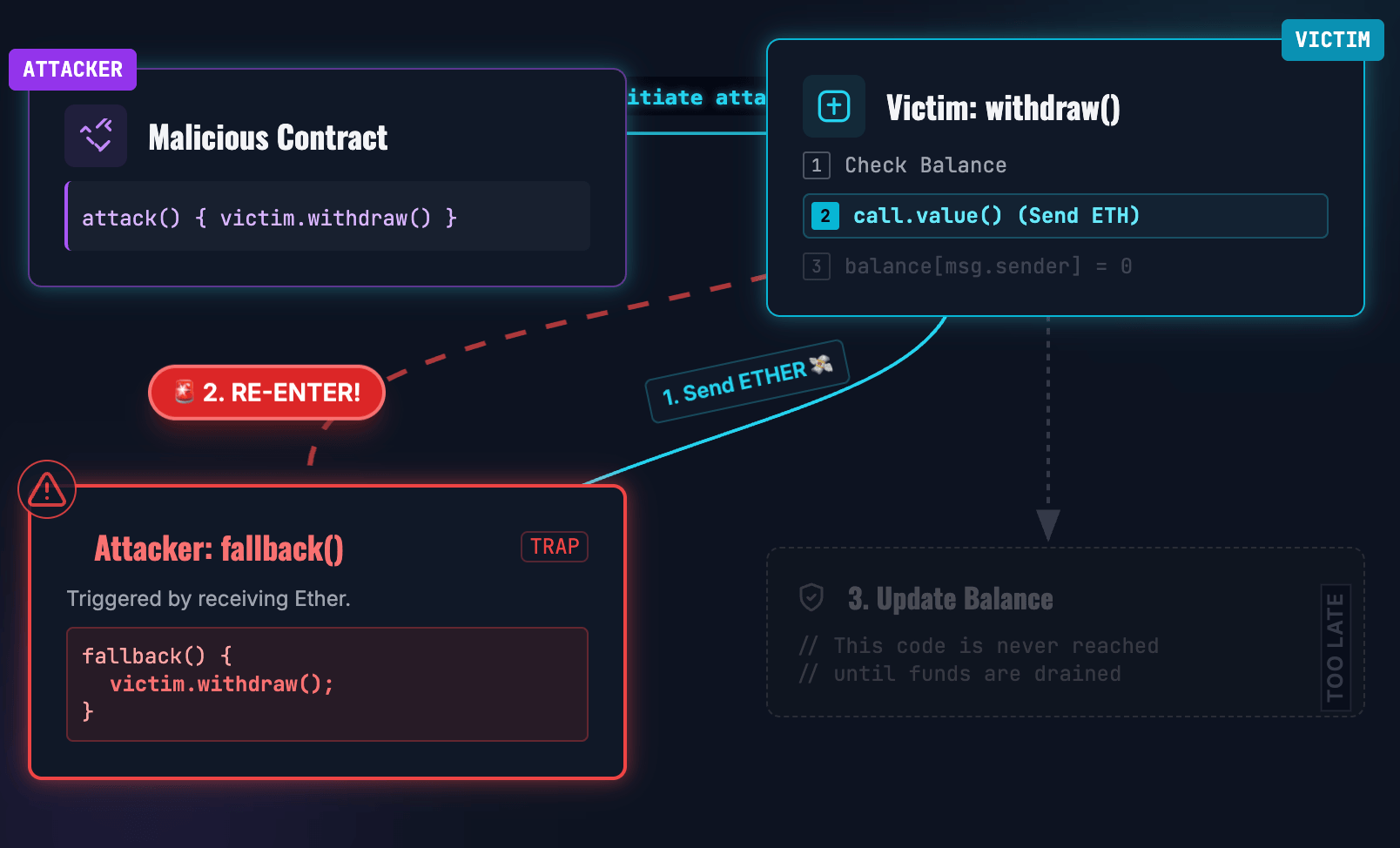
Solidity: The "Checks-Effects-Interactions" Struggle
Solidity’s
call function forwards control flow to the recipient, often triggering a malicious fallback function.1// Vulnerable Solidity Code Example2function withdraw() public {3 uint bal = balances[msg.sender];4 require(bal > 0);56 (bool sent, ) = msg.sender.call{value: bal}(""); // External Call7 require(sent, "Failed to send Ether");89 balances[msg.sender] = 0; // State Update happens too late!10}
Read-Only Reentrancy: A variant where the reentrant call targets a
view function (like an oracle price), which returns "dirty" state because the parent transaction hasn't finished its update.Rust (Solana): CPI and the Depth Limit
Solana mitigates this via:
- RefCell Panic: The runtime prevents an account from being borrowed mutably twice in the same instruction.
- CPI Depth Limit: Solana enforces a hard limit of 4 on Cross-Program Invocation depth, preventing the deep stacks required for recursive draining.
Move: Structural Prevention
Move addresses reentrancy at the VM level:
- No Dynamic Dispatch: Traditionally, Move modules only call explicit dependencies, removing unexpected callbacks.
- Resource Locking: In Aptos, modifying a resource requires a mutable reference.
1let balance = borrow_global_mut<Balance>(addr);2// balance is now locked.
If an external call attempts to re-enter and borrow
Balance again, the VM aborts with EALREADY_BORROWED. This also solves Read-Only reentrancy, as the borrow checker prevents an immutable reference from existing while a mutable one is active.Comparison of Move Implementations: Aptos vs. Sui
Aptos: Global Storage
Aptos utilizes an account-centric model. Resources are stored under addresses via
borrow_global<T>(address). It achieves parallelism via Block-STM, which optimistically executes transactions and re-runs them if conflicts are detected.Sui: Object-Centric
Are you audit-ready?
Download the free Pre-Audit Readiness Checklist used by 30+ protocols preparing for their first audit.
No spam. Unsubscribe anytime.
Sui treats everything as an Object with a unique ID. Transactions declare object dependencies upfront. Owned Objects bypass global consensus for instant finality, while Shared Objects go through consensus.
Move Implementation Differences
| Feature | Aptos Move | Sui Move |
|---|---|---|
| State Storage | Global Map (Address, Type) | Object Store (ObjectID) |
| Concurrency | Optimistic (Block-STM) | Deterministic (DAG / Inputs) |
| Access Control | Signer checks | Capabilities (Object Possession) |
| Upgrades | Compatible policies | Immutable Packages + UpgradeCap |
| Best Use Case | Deep DeFi / Composability | Gaming / NFTs / High-Throughput |
Access Control: Identity vs. Capabilities
Solidity: Identity-Based
Relies on
msg.sender. This often leads to centralized "God Mode" roles and is vulnerable to phishing if tx.origin is used incorrectly.Move: Capability-Based
Authority is an object (Capability), not an identity.
1struct AdminCap has key, store { id: UID }23public entry fun mint(_: &AdminCap,...) { ... }
The
mint function doesn't check who called it; it checks if the caller provided the AdminCap. This allows permissions to be transferred or held by MultiSigs without changing contract logic.Upgradeability Patterns and Risks
Solidity: Proxy Patterns
Uses
delegatecall to point a Proxy to a Logic contract. This is prone to Storage Collisions (misaligned variables) and Uninitialized Proxies.Move (Aptos): Native Checks
The VM validates new bytecode against the old. It ensures memory layout safety (no changing existing structs) and API safety (public signatures must persist), preventing storage collisions by design.
Formal Verification: The Move Prover
While Solidity relies on external tools like Slither or Certora, Move integrates the Move Prover (MVP) into its toolchain. In this way, Move brings Formal Verification closer to the developer workflow. Developers write specifications (invariants) directly in the code:
1invariant balance >= 0;2invariant global<Supply>(addr).total == sum(all_coin_balances);
The Prover uses SMT solvers to mathematically prove these invariants hold for all possible execution paths.
Conclusion
For L1 architects, the choice of language defines the network's risk profile:
- Solidity (EVM): "Trust the Developer." High flexibility, but requires a fortress of external audits.
- Rust (Solana): "Trust the Implementation." Maximum performance, but high complexity in account validation.
- Move: "Trust the Compiler." By treating assets as linear resources, Move eliminates entire vulnerability classes at the VM level.
In the era of billion-dollar exploits, Move’s resource-oriented paradigm represents the most significant architectural advancement in blockchain security since the invention of the smart contract.
FAQ: Move vs. Rust vs. Solidity Security
1. Why is Move considered safer than Solidity?
Move uses "Linear Logic" for resources, meaning assets cannot be copied or discarded by accident. This eliminates entire classes of bugs like "floating tokens" or "double spending" that are possible in Solidity's ledger-based model, reducing the reliance on manual security checks.
2. Does Rust's memory safety prevent smart contract hacks?
No. Rust's memory safety prevents system-level crashes (like buffer overflows), but it does not prevent logic errors. Developers must still manually verify account ownership and signatures. Many Solana exploits stem from "missing signer checks", a logic flaw that Rust's compiler does not catch.
3. What is Reentrancy and why does it still happen in 2026?
Reentrancy happens when a malicious contract calls back into the calling contract before state is updated. Despite being a known issue for a decade, it persists because Solidity defaults to "checks-effects-interactions" manual patterns. Move prevents this at the architectural level by disabling dynamic dispatch or locking resources during execution.
4. Are Solidity audits still necessary if I use formal verification?
Yes. Formal Verification proves that the code matches the specification, but it cannot prove that the specification itself is economically sound. An audit is still required to close the "Logic vs. Intent" gap.
5. How does the cost of auditing Move code compare to Solidity?
Due to the specialized skill set required, Move (and Rust) audits often command a premium over Solidity audits. However, the stricter compiler checks in Move can reduce the time spent on "low-hanging fruit" bugs. See our 2026 Audit Pricing Guide for exact benchmarks.
6. Can I port my Solidity dApp to Aptos/Sui easily?
Direct porting is difficult because the paradigms are different (Contract-centric vs. Resource-centric). It is often better to rewrite the logic to leverage Move's native security features rather than trying to force Solidity patterns into Move, which can lead to inefficient and less secure code.
Partner with Zealynx
Whether you are building on EVM, Solana, or Move, security is the foundation of your TVL. At Zealynx, we specialize in cross-chain security reviews, from gas optimization in Solidity to resource analysis in Move.
Glossary
| Term | Definition |
|---|---|
| Reentrancy | A vulnerability where an external call hijacks control flow to re-execute a function before its first invocation completes, enabling repeated state manipulation. |
| Linear Logic | A type system property in Move where resources must be used exactly once and cannot be implicitly copied or discarded, enforcing digital scarcity at the language level. |
| Bytecode Verifier | An on-chain component in the MoveVM that validates bytecode for type safety and resource linearity before execution, preventing malicious code from violating invariants. |
| EVM | The Ethereum Virtual Machine, a stack-based execution environment that runs smart contracts on Ethereum and compatible blockchains. |
| Formal Verification | A mathematical method for proving that code meets its specification across all possible execution paths, using SMT solvers and invariant checking. |
Are you audit-ready?
Download the free Pre-Audit Readiness Checklist used by 30+ protocols preparing for their first audit.
No spam. Unsubscribe anytime.