OWASP Smart Contract Top 10
Annual empirically-anchored ranking of the most impactful smart contract vulnerability classes, published by the OWASP Smart Contract Security project.
The OWASP Smart Contract Top 10 is an annual ranking of the most impactful smart contract vulnerability classes, maintained by the OWASP Smart Contract Security (SCS) project. OWASP — the Open Worldwide Application Security Project — is the same non-profit that has published the canonical web-application "top 10" since 2003. The smart contract list adapts that methodology to on-chain code: each year's ranking is anchored to deduplicated incident data from the prior calendar year, weighted by financial impact and exploit frequency. The 2026 edition is anchored to 122 deduplicated 2025 incidents representing roughly $905M in contract-only losses.
Why the list matters
Unlike vendor-published "top vulnerabilities" articles, the OWASP smart contract top 10 is empirically-anchored and consensus-reviewed by working-group contributors from multiple audit firms, formal-methods researchers, and protocol teams. It is the closest thing the industry has to a shared language for prioritizing security work. Audit firms reference it in scoping conversations; protocol teams reference it in pre-launch checklists; insurance underwriters reference it when pricing coverage. A finding tagged "SC02:2026" or "SC10:2026" is immediately legible to any technical reviewer.
The 2026 list
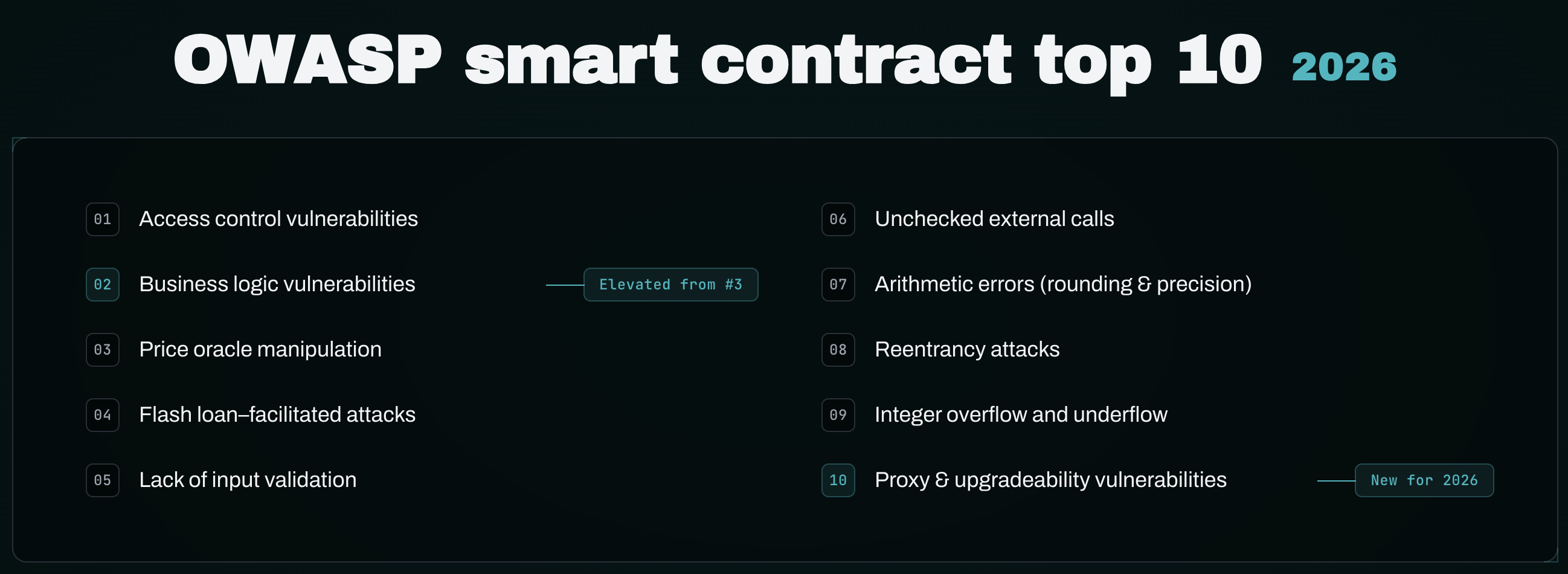
The complete OWASP Smart Contract Top 10 2026:
- SC01:2026 — Access control vulnerabilities
- SC02:2026 — Business logic vulnerabilities
- SC03:2026 — Price oracle manipulation
- SC04:2026 — Flash loan–facilitated attacks
- SC05:2026 — Lack of input validation
- SC06:2026 — Unchecked external calls
- SC07:2026 — Arithmetic errors (rounding & precision)
- SC08:2026 — Reentrancy attacks
- SC09:2026 — Integer overflow and underflow
- SC10:2026 — Proxy & upgradeability vulnerabilities
What changed from 2025 to 2026
Two structural changes carry the weight of the 2026 revision. Business logic vulnerabilities moved from #3 (titled "Logic Errors") to #2, with scope explicitly expanded to cover reward and fee logic flaws, eligibility and limit bypasses, path-dependent state machines, and cross-module assumptions. The rename signals OWASP's recognition that invariant collapse — where every individual code-level check passes but the protocol still fails because the rules being enforced do not match the rules the protocol needed to enforce — is now the largest single-protocol loss category. Worked examples include Yearn yETH ($9M, November 2025), Cetus ($223M, May 2025), and Balancer V2 ComposableStablePool ($128M, November 2025).
Proxy & upgradeability vulnerabilities is a new category at #10, added because uninitialized ERC1967 proxies became an automated attack campaign in 2025. Kinto Protocol ($1.55M, July 2025) is the most-cited specific case; aggregate losses across the broader campaign exceeded $10M. The category covers four sub-issues: upgrade and admin role hijack, initialization and re-initialization, delegatecall context errors, and storage layout collisions.
Reentrancy dropped from #2 to #8 because mature controls — ReentrancyGuard, ReentrancyGuardTransient, Slither and Mythril detection — handle the classic pattern reliably. The category remains in the top ten because callback-driven reentrancy (ERC-721/1155/3525/777 hooks, ERC-4626 hooks, flash-loan callbacks) and read-only reentrancy still produce findings.
Compound exploit pattern
The 2026 list emphasizes that single-vector exploits are rare in modern incident data. The default exploit chain combines categories: flash loan supplies adversarial capital (SC04) → oracle manipulation skews a price reference (SC03) → business logic flaw permits an under-collateralized action (SC02) → unchecked external call or proxy weakness finalizes extraction (SC06/SC10). Each step in isolation can pass review. The composition violates an invariant nobody declared. This is why the audit response across the 2026 list is invariant testing, formal verification of high-value properties, and trust-boundary mapping — not a category-by-category code review.
Audit response
The structural audit response across all ten categories shares a common shape: map the trust boundaries; define invariants in plain English (ten or more for any non-trivial protocol); translate invariants into property tests via Foundry stateful fuzz, Echidna, or Medusa; apply formal verification (Halmos, Certora) to the high-value subset; manual review for what tooling cannot reach (business logic correctness against protocol intent, off-chain trust assumptions, game-theoretic edge cases); continuous verification post-deployment via the same invariants run as on-chain monitors and CI property tests.
Related resources
- OWASP Smart Contract Top 10 2026: changes and audit guide — full walkthrough of every category with worked 2025/2026 incidents.
- 2025 DeFi hacks: $3.4B exploit lessons — the empirical base the 2026 list is anchored to.
- Divide and conquer auditing — the trust-boundary methodology the audit response depends on.
- The power of fuzzing and formal verification — the tooling matrix for the invariant-testing layer.
Articles Using This Term
Learn more about OWASP Smart Contract Top 10 in these articles:
OWASP Smart Contract Top 10 2026: changes and audit guide
The 2026 OWASP Smart Contract Top 10 elevated business logic to #2 and added proxy & upgradeability at #10. Here's what changed and how to audit.

2025 DeFi Hacks: $3.4B Exploit Lessons You Must Know
$3.4B lost in 2025: Bybit, Cetus, Balancer breakdowns. Zealynx auditors explain blind signing, supply chain attacks, and how to close audit blind spots.
How Smart Contract Audits Boost Gas Savings and Market Cap: Real ROI Insights
Smart contract audits cut gas costs, attract investors, and set legal standard of care. Zealynx breaks down the measurable ROI — beyond just avoiding a hack.
Related Terms
Access Control
Security mechanisms that restrict which addresses can call specific functions in a smart contract, preventing unauthorized actions.
Flash Loan
Uncollateralized loan borrowed and repaid within a single transaction, often used for arbitrage or attacks.
Price Oracle Manipulation
An attack where an attacker artificially skews the price reported by a price oracle to exploit protocols that rely on it.
Reentrancy Attack
A vulnerability where external calls allow malicious contracts to recursively call back before state updates complete.
Proxy Pattern
Smart contract design separating storage and logic, enabling upgrades by changing implementation while preserving state.
Invariant Testing
Property-based testing approach verifying that critical protocol conditions remain true across all possible execution paths.
Trust Boundary
Interface where data enters protocol or assets move between components, representing highest-risk areas requiring focused security analysis.
Need expert guidance on OWASP Smart Contract Top 10?
Our team at Zealynx has deep expertise in blockchain security and DeFi protocols. Whether you need an audit or consultation, we're here to help.
Get a Quote
